Setting up network routes: the choice of connection used for the Internet; simultaneous use of multiple connections for different purposes
Table of contents
1. How in Linux to choose the connection used for the Internet
2. How to simultaneously use multiple connections for different purposes
3. Using OpenVPN for all connections except for certain IP addresses, networks or sites
4. Setting computer as a network gateway
I already talked about ‘How to switch between Internet connections in Windows’, now we will consider the same question for Linux. In addition, I'll show you how you can use both connections to the Internet at the same time, for example, through one you can scan, and through another you can simply surf websites. And also I will show a couple interesting tricks.
How in Linux to choose the connection used for the Internet
A computer can be simultaneously connected to several networks and any one of them can be used for Internet access. In order to access the global network, in fact, only one network is used, and the other (or others) are in reserve. The operating system selects the connection that has the best characteristics. If you want to switch between Internet connections without disconnecting from the one that is used by default, that's what I'm going to show now.
If you followed the link I gave just above (switching between Internet connections in Windows), then you know that for each network interface there is a so-called default route - through this route all traffic that does not correspond to other routing rules pass. If your computer is connected to several networks, the system keeps several default routes at once, but assigns them the so-called metrics - the rating of the connection quality. The lower this value, the higher the connection priority.
To see the default routes, use the command:
ip route list default
An example in my case (I'm connected to two networks):
default via 192.168.0.1 dev wlo1 proto dhcp metric 600 default via 192.168.0.1 dev wlp0s20f0u1 proto dhcp metric 601
It is seen that I have two default routes for the network interface wlo1 and wlp0s20f0u1. And the first metric is 600, and the second metric is 601. Since the first value is less, the first connection has priority.
In order the system to start using wlp0s20f0u1 and wlo1 keep in reserve, we need to set the metric for wlp0s20f0u1 to any value lower than 600.
In subsequent commands, replace the interface names with their names on your system - they may differ. Also adjust IP addresses.
You cannot change the route, so we will delete the default route of interest, and add exactly the same, but with the new metric. Pay attention to the peculiarity - both my routes have the same IP address of the gateway (router), so that the system understands exactly what we want from it, will also indicate the name of the interface.
Delete the default route for the wlp0s20f0u1 interface:
sudo ip route del default dev wlp0s20f0u1
Add the default route for the interface wlp0s20f0u1 (also specify the router’s IP):
sudo ip route add default via 192.168.0.1 dev wlp0s20f0u1 metric 100
Do the check:
ip route list default
The metric for wlp0s20f0u1 is changed:
default via 192.168.0.1 dev wlp0s20f0u1 metric 100 default via 192.168.0.1 dev wlo1 proto dhcp metric 600
Checking the external IP address also shows that now the Internet connection is performed via wlp0s20f0u1. By the way, the Wi-Fi level indicator in NetworkManager began to show the signal for the network on wlp0s20f0u1.
The changes you make will disappear when you reboot your computer. Or you can return everything as it was again deleting the route for one of the interfaces and adding it again with the previous metric value.
How to simultaneously use multiple connections for different purposes
The previous method is suitable for switching between multiple connections. But what if we want to use both channels simultaneously? For example, through one connection, I want to browse sites, and through another do a scan? Or I want to open one site through one connection, and another site - through another?
This can be done by specifying routes. Routes are rules that answer the question: a request to this IP on which interface to transmit?
You can see the available routes with the following command:
ip route
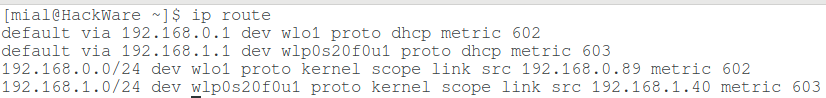
Example in my case:
The meaning of the first two lines with default via string was considered a bit higher - these are the default routes. Consider the other two:
192.168.0.0/24 dev wlo1 proto kernel scope link src 192.168.0.89 metric 602 192.168.1.0/24 dev wlp0s20f0u1 proto kernel scope link src 192.168.1.40 metric 603
For example, the 92.168.0.0/24 dev wlo1 proto kernel scope link src 192.168.0.89 metric 602 line indicates that requests to IP addresses belonging to 192.168.0.0/24 (for example, to address 192.168.0.20) will be forwarded through interface wlo1. Also, there are additional options, including metrics.
For example, I want all requests to any IP belonging to 172.16.0.0/12 network to go to the wlp0s20f0u1 interface. While all the others – would go on the default route, which is wlo1.
wlo1 is already the default route, so we do nothing with it.
To add a routing rule by which any requests to 172.16.0.0/12 will be sent through a gateway with IP 192.168.1.1 from the wlp0s20f0u1 interface:
sudo ip route add 172.16.0.0/12 via 192.168.1.1 dev wlp0s20f0u1 metric 5
We check:
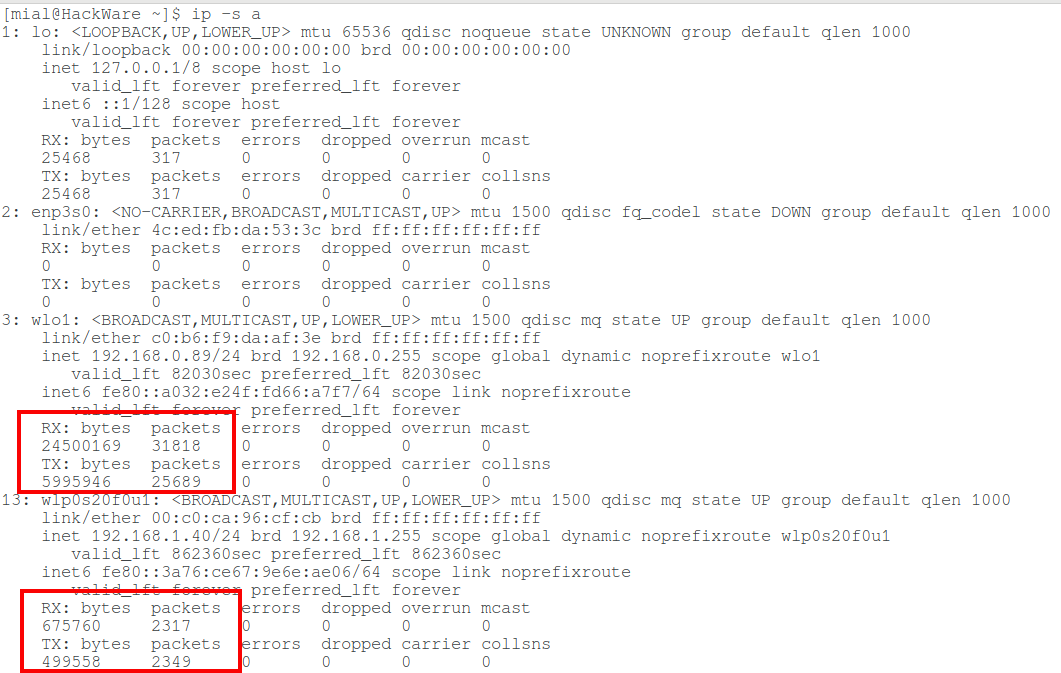
Now, for testing in practice, we look at the values of the transmitted and received data for network interfaces:
ip -s a
I have:
For wlo1:
Received: packet byte
24500169 31818
Sent bytes of packets
5995946 25689
For wlp0s20f0u1:
Received: packet byte
675760 2317
Sent bytes of packets
499558 2349
I will open a website, for example miloserdov.org. Again we look at the statistics:
For wlo1:
Received: packet byte
33755547 38510
Sent bytes of packets
6410882 28040
For wlp0s20f0u1, the values have not changed.
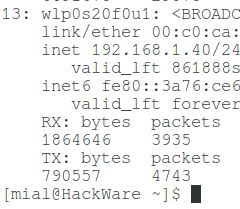
If you access the IP address 172.28.20.13 or any other belonging to the 172.16.0.0/12 network, you will see how the number of transmitted data for wlp0s20f0u1 has changed:
You can add any number of routes. You can also add one IP address (not subnets):
sudo ip route add 185.117.153.79 via 192.168.1.1 dev wlp0s20f0u1 metric 5
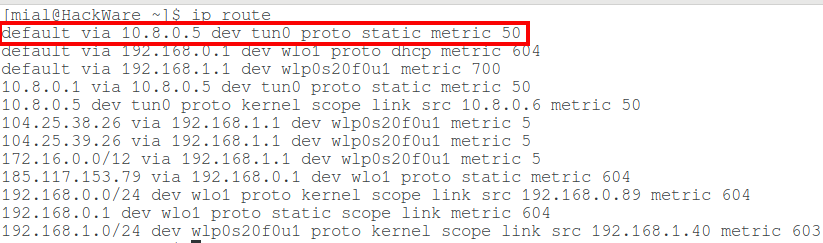
Using OpenVPN for all connections except for certain IP addresses, networks or sites
If you access the Internet through OpenVPN, then when establishing a connection to OpenVPN server, a new default route is created, for example:
default via 10.8.0.5 dev tun0 proto static metric 50
I think you already guessed that if we want to connect to a site or subnet bypassing OpenVPN, then it is enough for us to create a new route with a lower metric. In this case, you do not need to touch the route with interface tun0. As a result, it turns out that all connections will be made through OpenVPN, but when accessing the sites for whose IP the special route was set, the connection will be performed bypassing OpenVPN. By the way, the metric need not be lower - because the default route is used only in those cases when there is no special rule. That is, if you created a special routing rule for the IP address 185.117.153.79 with a metric of 500, then in the case of accessing address 185.117.153.79 such a rule will take precedence over the default via 10.8.0.5 dev tun0 proto static metric 50 rule, since it is a certain rule, and the default route leaves only those packages that did not leave earlier by any special rule.
Setting computer as a network gateway
You can configure other devices on the network so that they will not use a router as a gateway, but a specific computer on the local network. Traffic transmitted to this gateway-computer can be analyzed, or, for example, transmitted to the outside world via Tor or VPN. This is a bit like a man-in-the-middle attack. The difference in the methods of achieving the result: with MitM attack, manipulations with the ARP cache are performed. Here we just set up another computer to use our computer as a gateway.
I will show you the example of two computers running Linux.
On the first, I enable routing of incoming traffic:
sudo sysctl -w net.ipv4.ip_forward=1
The previous command is a complete analog of this command:
echo "1" > /proc/sys/net/ipv4/ip_forward
In addition, on the first computer, I run Wireshark to monitor traffic. As the filter I input icmp. The ICMP protocol is used for ping, tracing, and through this protocol errors are transmitted, such as ‘host unavailable’, ‘network unavailable’ and the like.
I do not configure anything on the first computer, only I look at its IP address in the local network - it is 192.168.0.51.
On the second computer, I delete the existing default route, and I set up a new route through 192.168.0.51:
sudo ip route del default sudo ip route add default via 192.168.0.51 metric 1
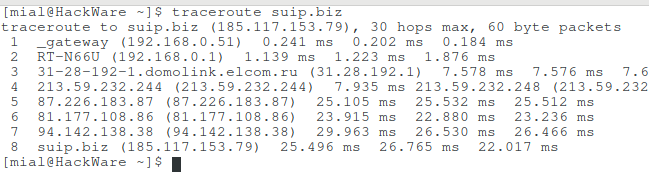
On the second computer, I trace route to the site:
traceroute suip.biz
Pay attention to the first two lines:
1 _gateway (192.168.0.51) 0.566 ms 0.547 ms 0.538 ms 2 RT-N66U (192.168.0.1) 1.521 ms 1.695 ms 1.802 ms
That is, first the traffic goes to the computer with the address 192.168.0.51 and only then to IP 192.168.0.1, that is, to the router.
I turn to the first computer and see that the traffic really went through it.
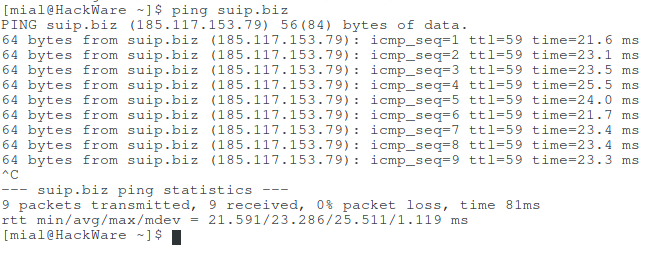
On the second computer I run ping:
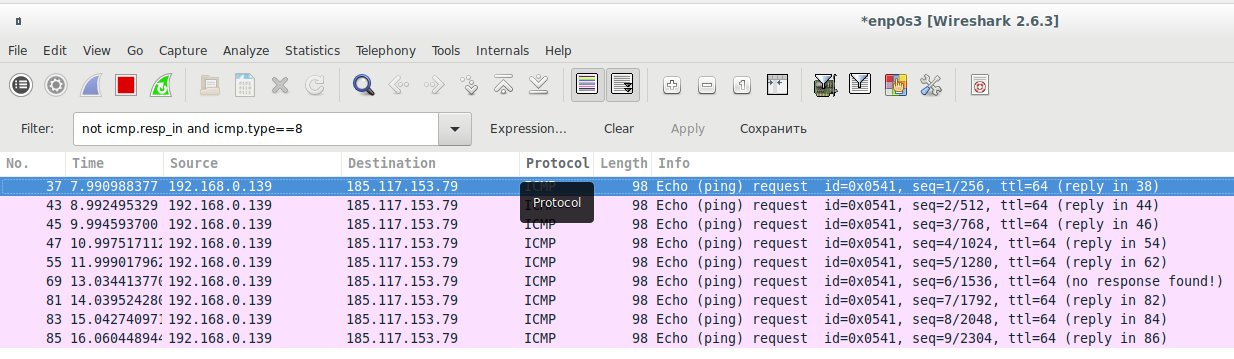
On the first computer as a filter I set
not icmp.resp_in and icmp.type==8
This filter means showing only pings:
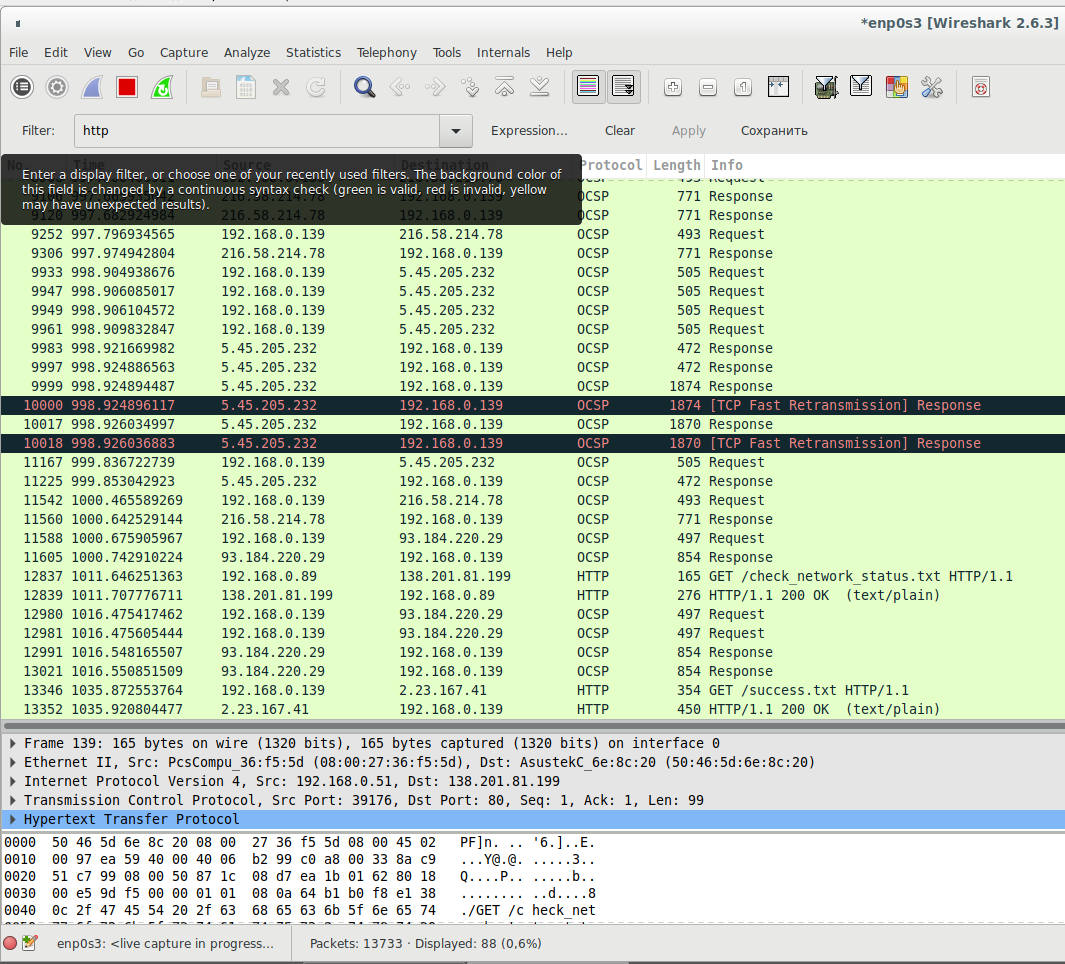
This works not only for the ICMP protocol, but also for other traffic. For example, on the second computer in a web browser, I open a website, and on the first computer I use a filter
http
You can see the web traffic for which the destination and the source address is 192.168.0.139, this is the IP address of the second computer.
Conclusion
Understanding how network routes work, you can very fine-tune the use of any network interfaces in your system.
These same principles for creating routes (and even these same commands) also work in routers.
If you want, you can turn one of the computers into a router (including plugging the Internet provider’s wire into it) and use it to analyze traffic, or very fine-tuning the rules that may not be available for your router.
For Windows systems, you can also configure routes for individual networks and IP by using the ROUTE command. With it you can set not only the default route, but also for networks and addresses, instead of 0.0.0.0 MASK 0.0.0.0, it is enough to specify specific IP addresses and network mask.
Related articles:
- How to switch between Internet connections in Windows (87.1%)
- How to configure Kali Linux to use a static IP address (51.6%)
- Introduction to IPv6 Addresses: How to Use and How to Explore the Network (Part 2) (51.6%)
- Introduction to IPv6 Addresses: How to Use and How to Explore the Network (Part 1) (51.1%)
- Windows Computer name: how to change and use (51.1%)
- How in Windows view the contents of a Linux disk and copy files from it (RANDOM - 50.4%)