How to decrypt WPA traffic in Wireshark
Let's start with the theory in order to understand why the process of decrypting Wi-Fi traffic in Wireshark requires some effort and why one cannot just decrypt any captured Wi-Fi traffic even if one has a password from the Access Point.
When transmitting via Wi-Fi, the traffic is encrypted using PTK (the Pairwise transient key). At the same time, PTK is dynamic, that is, it is created anew for each new connection. Thus, it turns out that Wi-Fi traffic for each connection in the same Access Point is encrypted with different PTKs, and even for the same Client after reconnecting PTK changes. To calculate PTK, you need data from a four-way handshake, as well as a password of a Wi-Fi network (in fact, you also need other information, such as the network name (SSID), but obtaining this data is not a problem).
The main thing you need to understand: to decrypt Wi-Fi traffic, you need a four-way handshake. And not any, but exactly the one that happened to transmit the traffic that needs to be decrypted. But to use the captured handshake you need a password of the Wi-Fi network.
So, to decrypt Wi-Fi traffic is needed:
1) a handshake that occurred between the Client and the Access Point immediately prior to the exchange of decrypted information
2) password to connect to the Access Point
Next will be shown two examples of capturing Wi-Fi traffic and its decryption. The first data capture is done using Airodump-ng, and then the wireless traffic will be decrypted in Wireshark. In the second example, the data will be captured and decrypted using only Wireshark.
Capturing Wi-Fi traffic in Airodump-ng
In order for the data to be suitable for decryption, it is necessary that the Wi-Fi card does not switch channels, but capture information on one channel on which the target Access Point operates. Therefore, we start by collecting information about the target access point.
We look at the names of wireless interfaces:
iw dev
We set the INTERFACE into monitor mode with commands like this:
sudo ip link set INTERFACE down sudo iw INTERFACE set monitor control sudo ip link set INTERFACE up
Run airodump-ng with a command like:
sudo airodump-ng INTERFACE
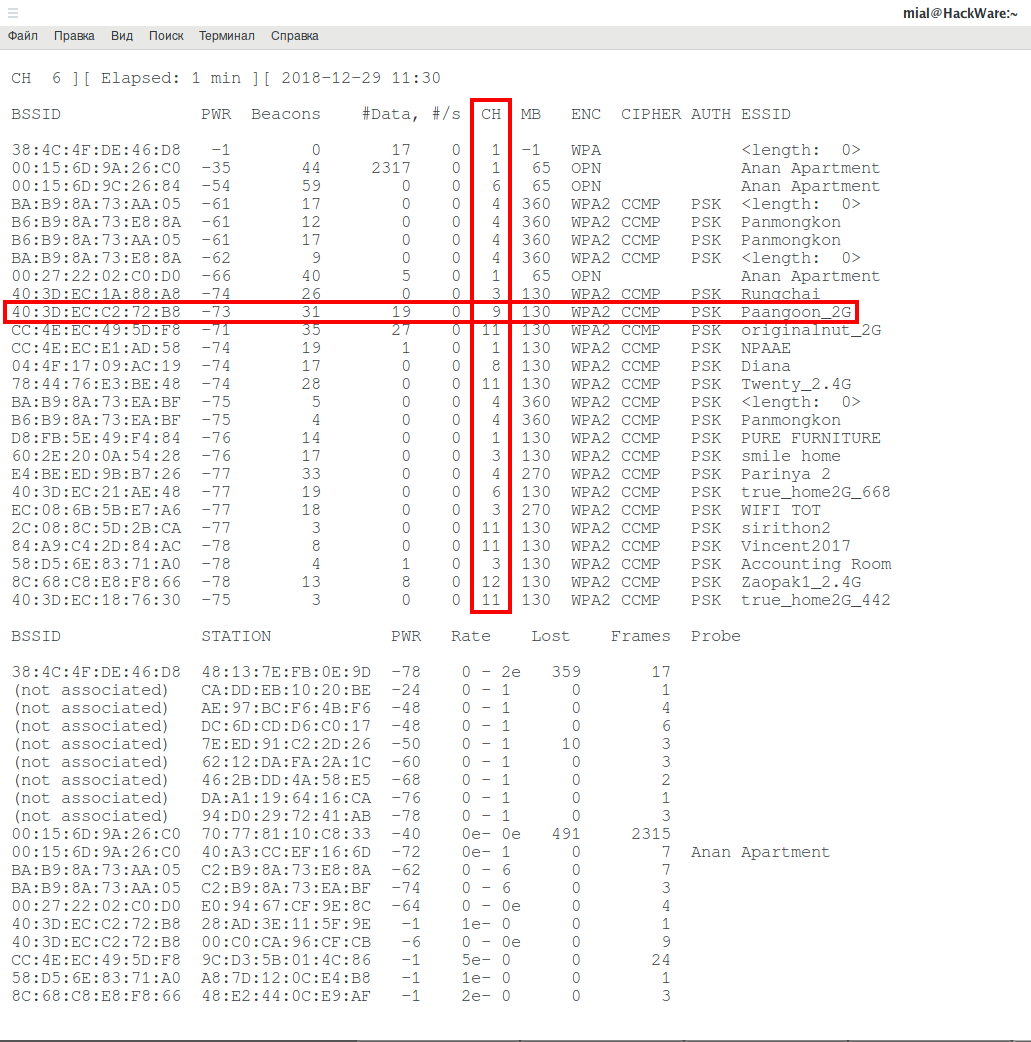
For example, I want to capture and decrypt traffic for the Paangoon_2G Access Point, which operates on channel 9.
Then I need to restart airodump-ng with a command like this:
sudo airodump-ng INTERFACE --channel CHANNEL --write FILE_NAME
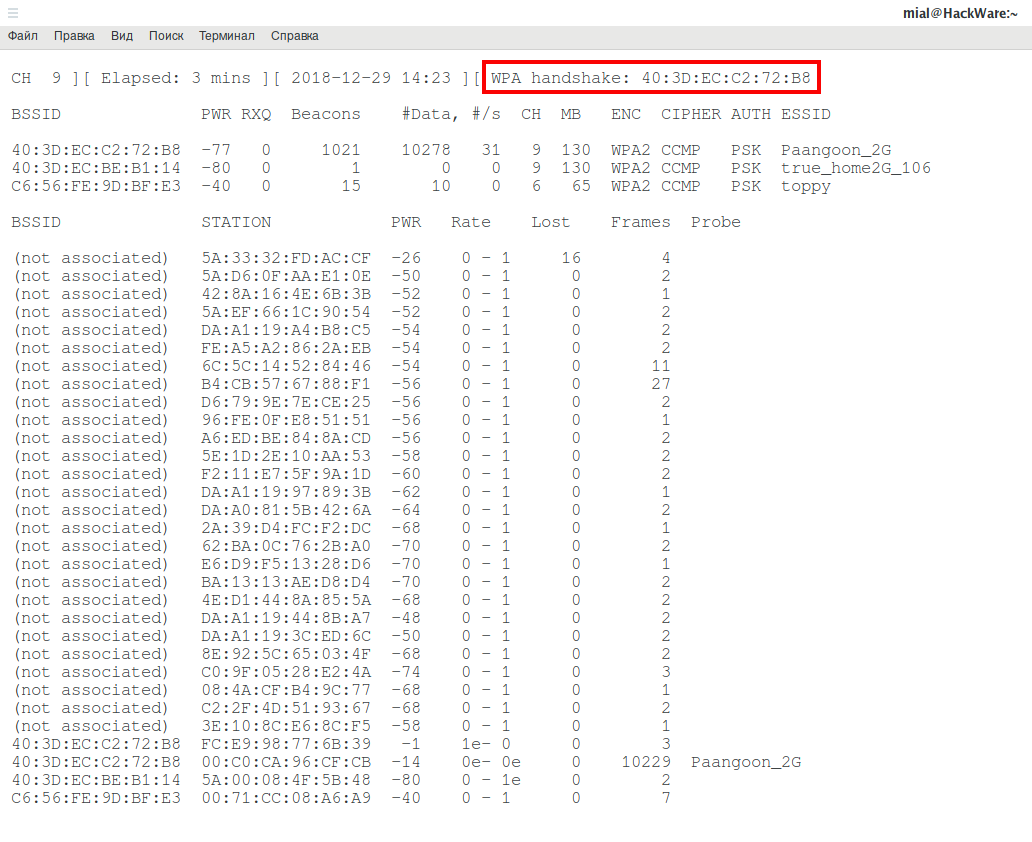
The WPA handshake string says that a four-way handshake was captured. It means that:
- now we can decrypt the Wi-Fi data (if we have the key of the Wi-Fi network)
- we can decrypt only data for a specific client (with which a handshake was made)
- we will be able to decrypt the data that was sent only after this captured handshake
Wi-Fi traffic decryption in Wireshark
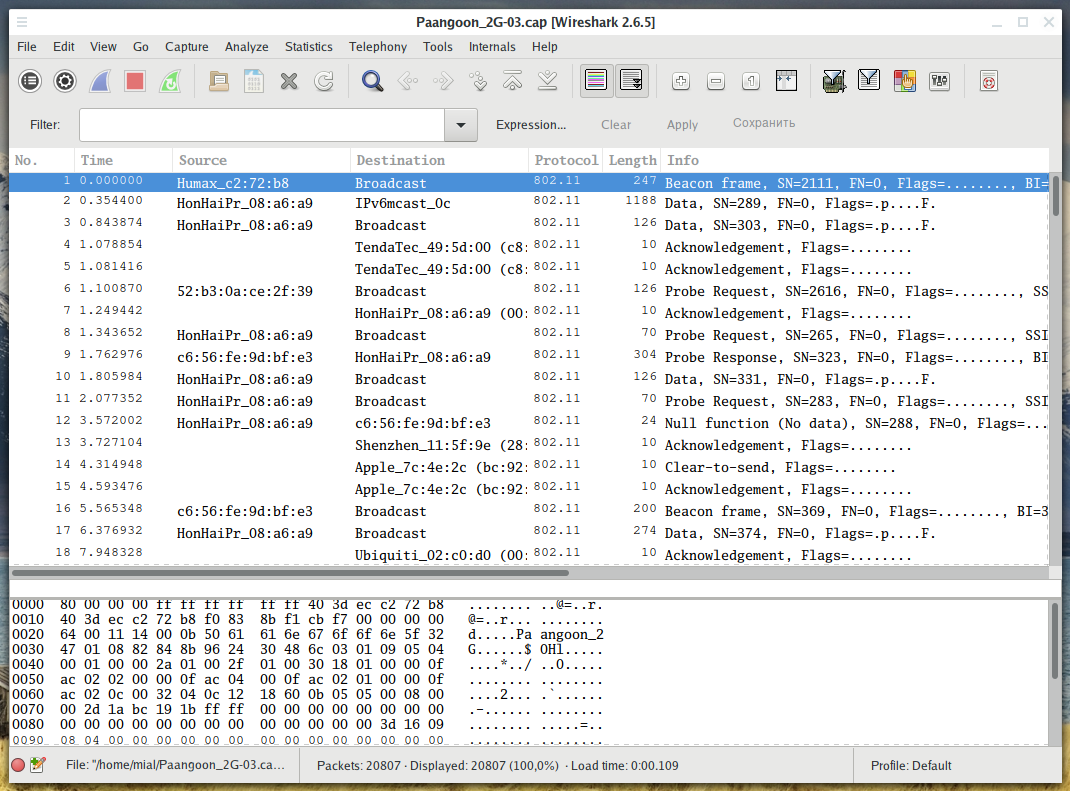
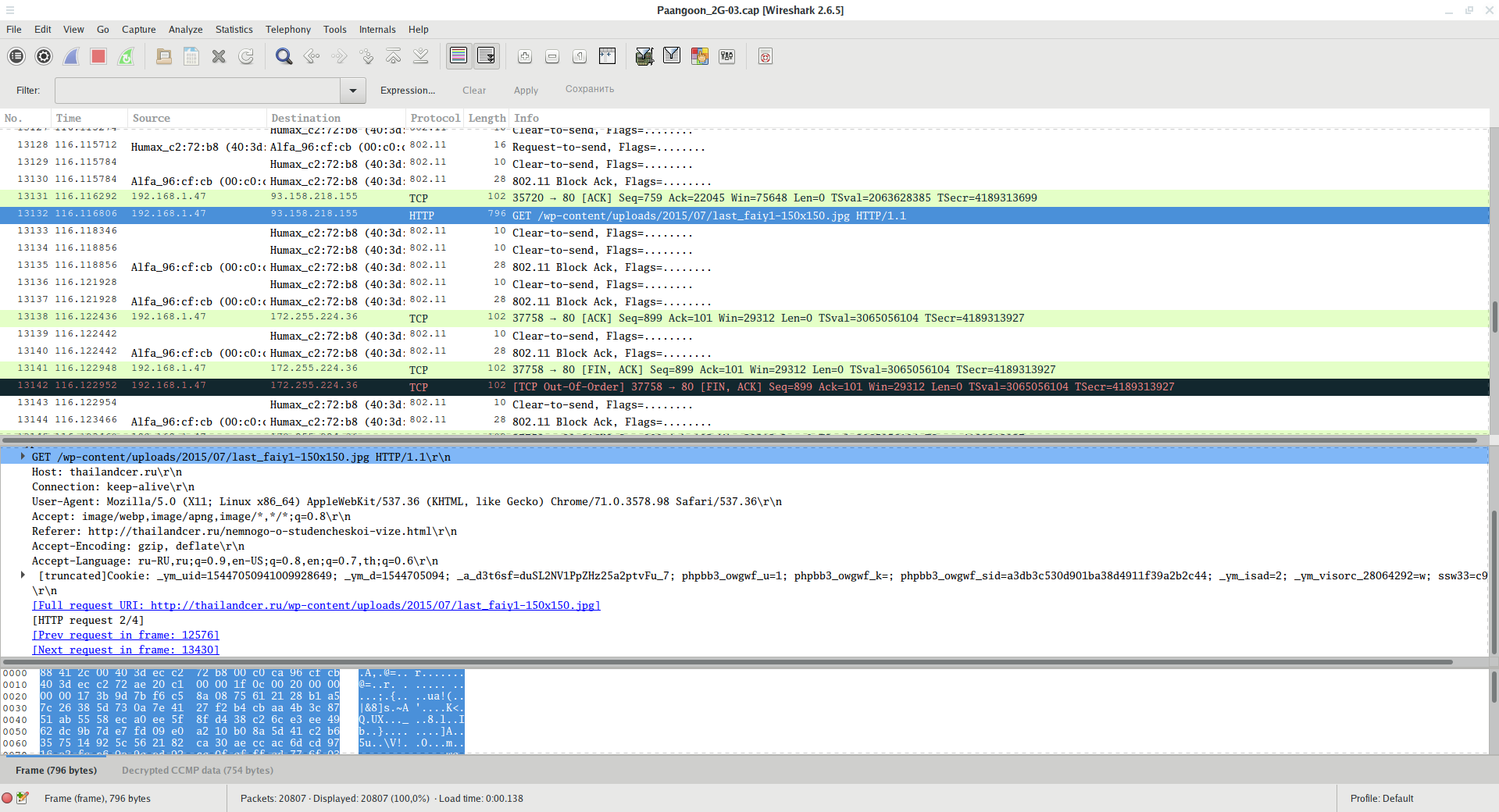
Open the capture file in Wireshark. In its original form, the traffic looks like this:
That is, without decryption, we see only the MAC addresses of the data transfer participants, some types of packets, as well as data packets — in which the payload is encrypted.
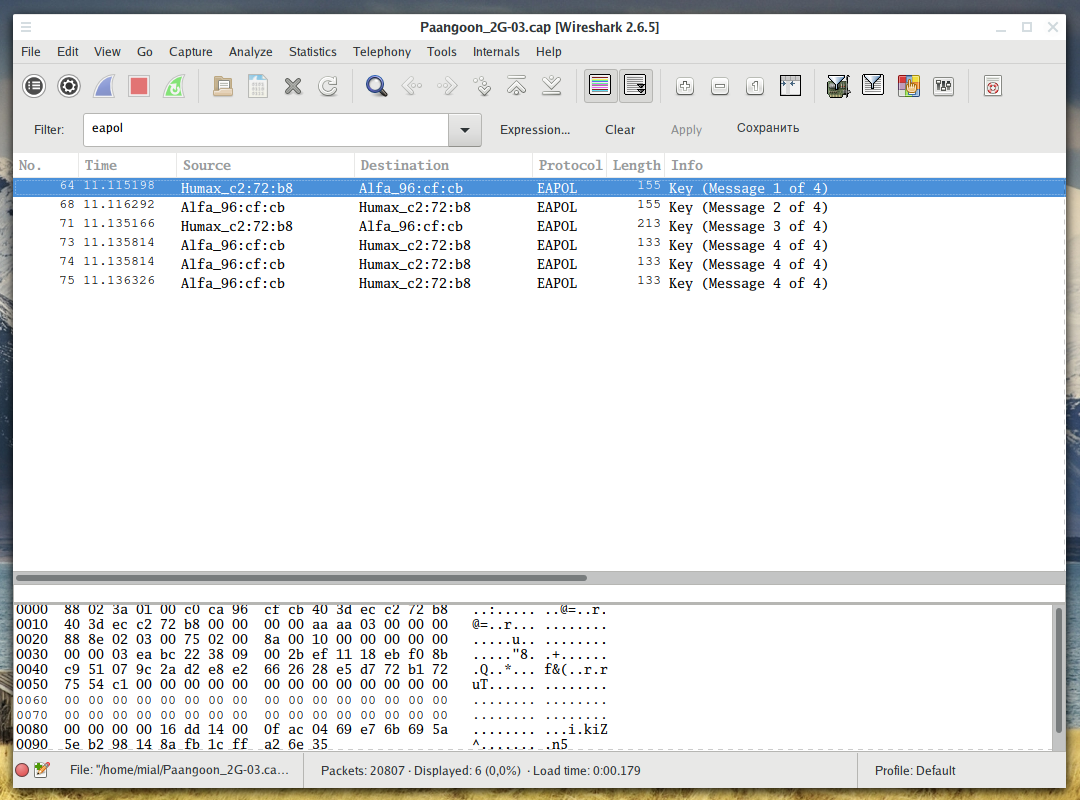
Before decoding, make sure that there is a handshake, otherwise there is no point in continuing:
eapol
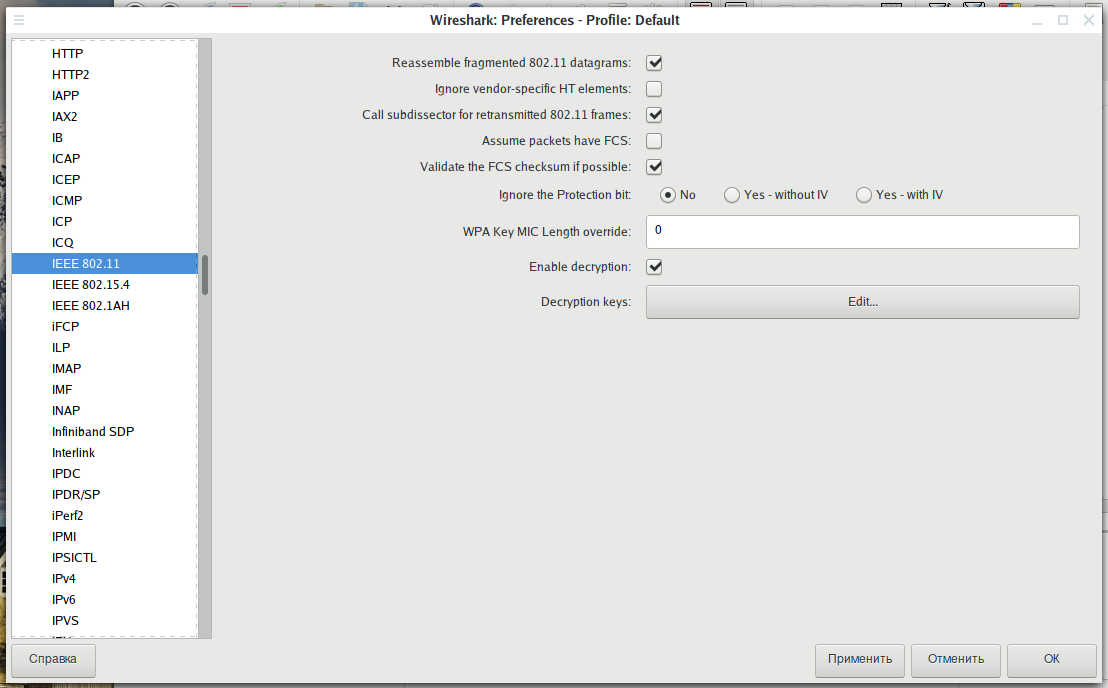
Before decoding, we need to make some changes in the IEEE 802.11 protocol settings.
Go to Edit → Preferences, expand the protocol section and select IEEE 802.11. The settings should be:
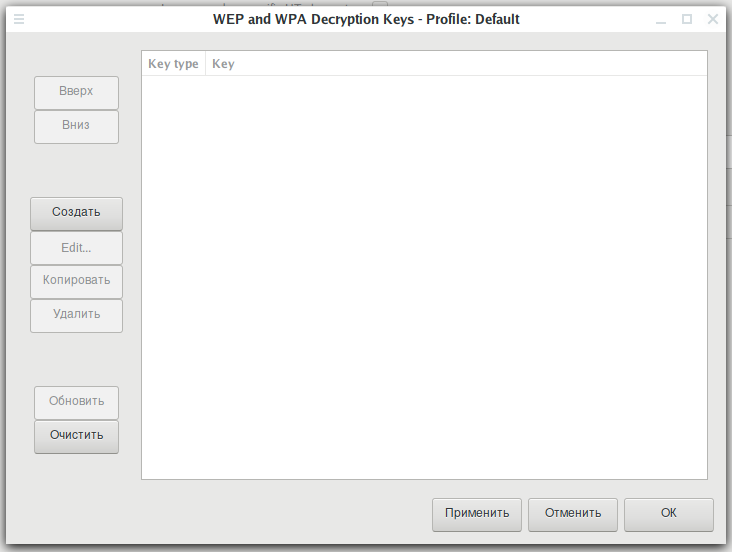
When you have the same settings as in the previous screenshot, click on the Edit button next to Decryption Keys (to add a WEP/WPA key):
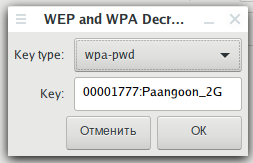
Click the Create button. In the window that opens, in the Key type field, select wpa-pwd, enter the password for the Wi-Fi network, and after the colon enter the name (SSID) of the network and click OK.
For example, in my case, the password is 00001777, and the network name is Paangoon_2G, then I enter:
00001777:Paangoon_2G
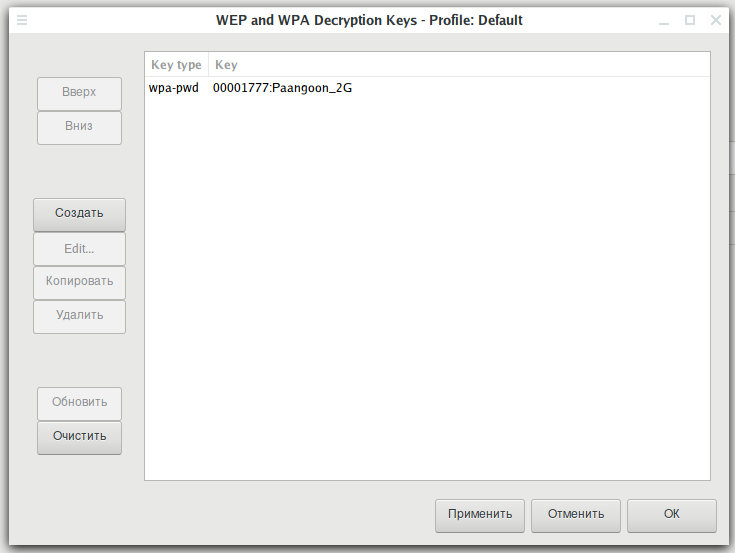
Click Apply:
Traffic will be decrypted:
Now there are visible DNS, HTTP requests and responses, as well as other network packets.
If traffic is captured not only for this network, but also for other networks operating on the same channel, or for this network but other clients for which no handshakes are taken, then this traffic will not be decrypted.
Capture Wi-Fi in Wireshark
Wi-Fi traffic can be captured directly in Wireshark. But we first need to switch the Wi-Fi card to the same channel as the target Access Point. This is done by commands like:
sudo ip link set INTERFACE down sudo iw INTERFACE set monitor control sudo ip link set INTERFACE up sudo iw dev INTERFACE set channel CHANNEL
In these commands, the words INTERFACE and CHANNEL must be replaced with actual data.
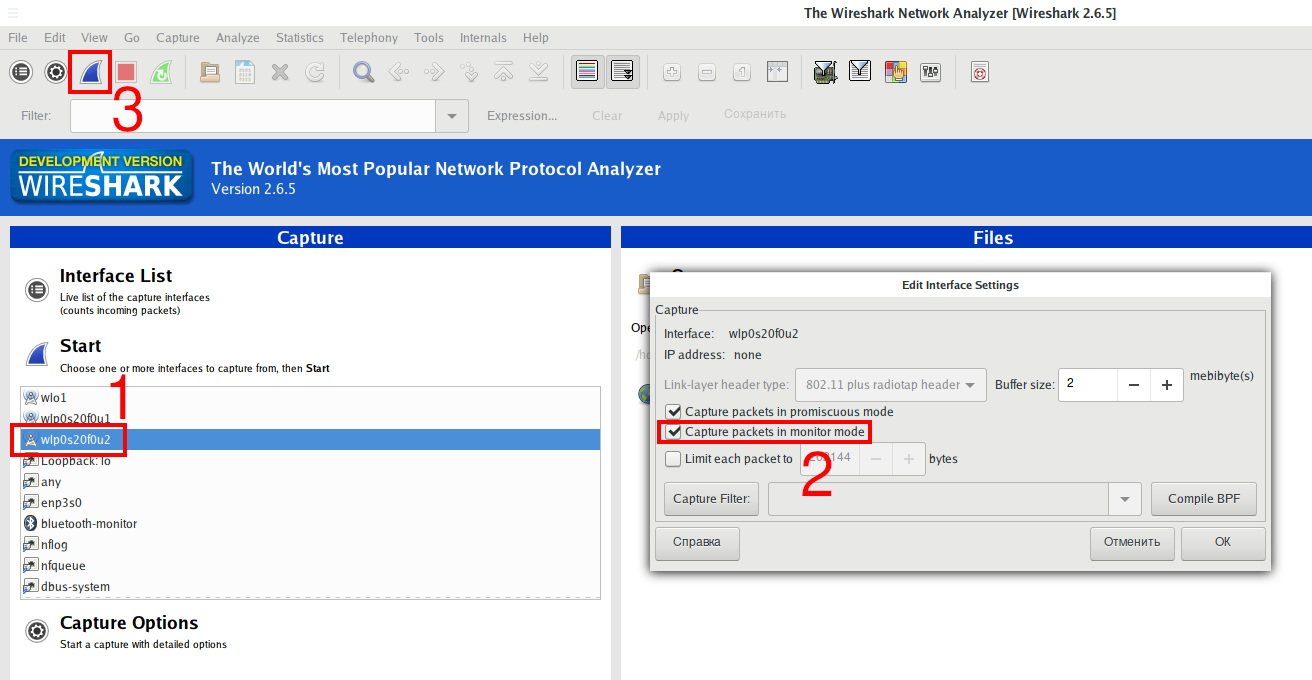
When the interface is switched to the desired channel, in Wireshark, find this interface, in its properties, check the Capture packets in monitor mode box. Then start capturing data:
The subsequent decryption is performed in exactly the same way as shown above.
Conclusion
To decrypt WEP Wi-Fi traffic, you only need to know the password. But APs with WEP almost never occur nowadays.
Related articles:
- How to capture a Wi-Fi handshake in tcpdump (83.4%)
- How to intercept and analyze traffic in open Wi-Fi (77.2%)
- How to hack Wi-Fi (76.4%)
- Hacking Wi-Fi without users in Aircrack-ng (76.4%)
- BoopSuite is an alternative to Airodump-ng, Airmon-ng and Aireplay-ng (72.8%)
- Comprehensive Guide to John the Ripper. Part 6: How to brute force non-standard hashes (RANDOM - 2%)
Hello,
Thanks for the great step-by-step instructions. I followed them to the letter but I can't seem to make the 4-way handshake appear.
I have not been able to find any of the reported "monitor mode" settings (described on the wireshark wiki). I have a whole slew of packets captured that are encrypted that I'd like to see the contents of.
I'm running macOS Mojave 10.14.3 on an intel iMac circa 2014. My wireless router (en0) is an Airport Extreme circa about 2010.
For the sake of argument, my WiFi password is "password" and the network name is "My Home Network" with spaces (not sure if spaces are allowed in the wpa-pwd key settings). I entered "password:My Home Network" and clicked ok, but I can't see any decrypted http packets or anything noticeably different - only 802.11. I definitely don't see the 4-way handshake happening in the capture.
Furthermore I'm wanting to capture packets sent to and from a specific Mac device with the address 36:56:9C:4D:4C:5C across the span of an entire day. Is there a way to limit captures to only that device to prevent very large file sizes from 24 hours of captures?
Any ideas what settings I may be missing or have screwed up that are preventing the 4-way handshake from occuring?
Thanks!
Hello! I guess the reason — you did not capture 4-way handshake.
Start off with Wireshark filter:
If you will see no captured packages, it means you did not capture the handshake.
Before trying to decrypt WPA traffic, try to perform less complex tasks like capturing 4-way handshake.
Thanks! I do not see any packets when using that filter, so I believe you're right. I'm not able to see the 4-way handshake happen tho. I've left (forget network) the wifi and re-joined it during a capture, but maybe my settings are wrong. I have the network password and SSID entered in the IEEE 802.11 settings, but I think something else is missing. I have a sample capture here: https://waterloooil.com/test/capture.pcap.
I don't see the 4-way handshake using that filter. I've set up the network password and SSID in wireshark so something else must be missing. Here's an example capture: https://waterloooil.com/test/capture.pcap.