Hacking websites training in Windows
Many web applications have been created that specifically contain vulnerabilities to train hacker skills.
Some of them are distributed installed and configured specifically for this purpose intended Linux distributions, some can be installed by yourself in any Linux distribution (for an example see the article “How to install OWASP Mutillidae II and Damn Vulnerable Web Application (DVWA) in Kali Linux”.
And in this article I will explain how to install and configure vulnerable web applications in Windows. Installation instructions will be given for:
- OWASP Mutillidae II
- Damn Vulnerable Web Application (DVWA)
- bWAPP
You can install only one of them or all at once – they are independent of each other.
This manual will be useful to those who are more accustomed to working in Windows. In addition, some of the vulnerabilities have their own specifics: for example, the OS command injection on Linux and on Windows is exploited in different ways.
All of these vulnerable web applications run on a web server (actually, like any other web applications). Therefore, we need a web server. You can install it in any way, I have the instruction ‘How to install web server on Windows 10 (Apache 2.4, PHP 7, MySQL 8.0 and phpMyAdmin)’ and my web server is installed in accordance with it. If your web server is installed in another way, then you may need to slightly edit the paths in the file system, but, in general, the installation principle is the same everywhere.
After installing the web server, also see the article “How to protect the Apache web server from hacking in Windows” - otherwise, while you learn to hack, you will be hacked.
In the c:\Server\data\htdocs\ folder create the directory pentest.
In the c:\Server\data\htdocs\pentest\ folder create the .htaccess file, open it with a text editor, and copy there:
Require local
This setting ensures that no one from outside can access these vulnerable environments. Otherwise, a hacker can hack the entire computer through these vulnerable web applications because in Windows the web server has permissions to all folders and files.
If you need a web server to be accessible on the local network (for example, you will attack web applications from another computer with Kali Linux), then instead of the above line, insert in the .htaccess file:
Require ip 127 Require ip 192.168 Require ip ::1
This setting allows access for IP in 127.0.0.0/8 and 192.168.0.0/16 ranges, as well as IPv6 addresses ::1/128 (0:0:0:0:0:0:0:1) (analogous to localhost).
In any case, access to vulnerable environments should be as limited as possible to outsiders.
How to install OWASP Mutillidae II in Windows
Moving on to installing and configuring OWASP Mutillidae II.
Download the OWASP Mutillidae II: https://github.com/webpwnized/mutillidae/archive/master.zip (this is the official site, always the latest version).
Unzip the downloaded archive into the folder c:\Server\data\htdocs\pentest\ and rename it from mutillidae-master to mutillidae.
Open the c:\Server\data\htdocs\pentest\mutillidae\.htaccess file, delete the lines from it:
Order Deny,Allow Deny from all ## This allows access from localhost Allow from 127. Allow from localhost ## This is to allow access from other machines on Virtual Box host-only networks. Allow from 192.168.0.0/16
and add the lines instead:
Require ip 127 Require ip 192.168 Require ip ::1
Save and close the file.
Open the c:\Server\data\htdocs\pentest\mutillidae\includes\database-config.inc file and in the line
define('DB_PASSWORD', 'mutillidae');
instead of mutillidae, set your password from MySQL (empty by default).
Save and close the file.
Now in your web browser, open http://localhost/pentest/mutillidae
On the page, find 3. Try to setup/reset the DB to see if that helps in it go to http://localhost/pentest/mutillidae/set-up-database.php
Now reopen http://localhost/pentest/mutillidae:
Everything is ready – now you can begin to train to hack websites.
How to install Damn Vulnerable Web Application (DVWA) in Windows
Now install and configure the Damn Vulnerable Web Application (DVWA).
Download the latest version of Damn Vulnerable Web Application (DVWA) from the official website at the link: https://github.com/ethicalhack3r/DVWA/archive/master.zip
Unzip the downloaded archive to c:\Server\data\htdocs\pentest\ and rename it from DVWA-master to DVWA.
In the c:\Server\data\htdocs\pentest\DVWA\config\ folder find the config.inc.php.dist file and copy it to the same folder, but with the name config.inc.php (or just rename it).
Open the c:\Server\data\htdocs\pentest\DVWA\config\config.inc.php file and find the line
$_DVWA[ 'db_password' ] = 'p@ssw0rd';
and replace p@ssw0rd with your actual password. By default, the password is blank.
Open the c:\Server\bin\PHP\php.ini file and find the line there:
allow_url_include = Off
replace this line with:
allow_url_include = On
Restart the web server for the changes to take effect:
c:\Server\bin\Apache24\bin\httpd.exe -k restart
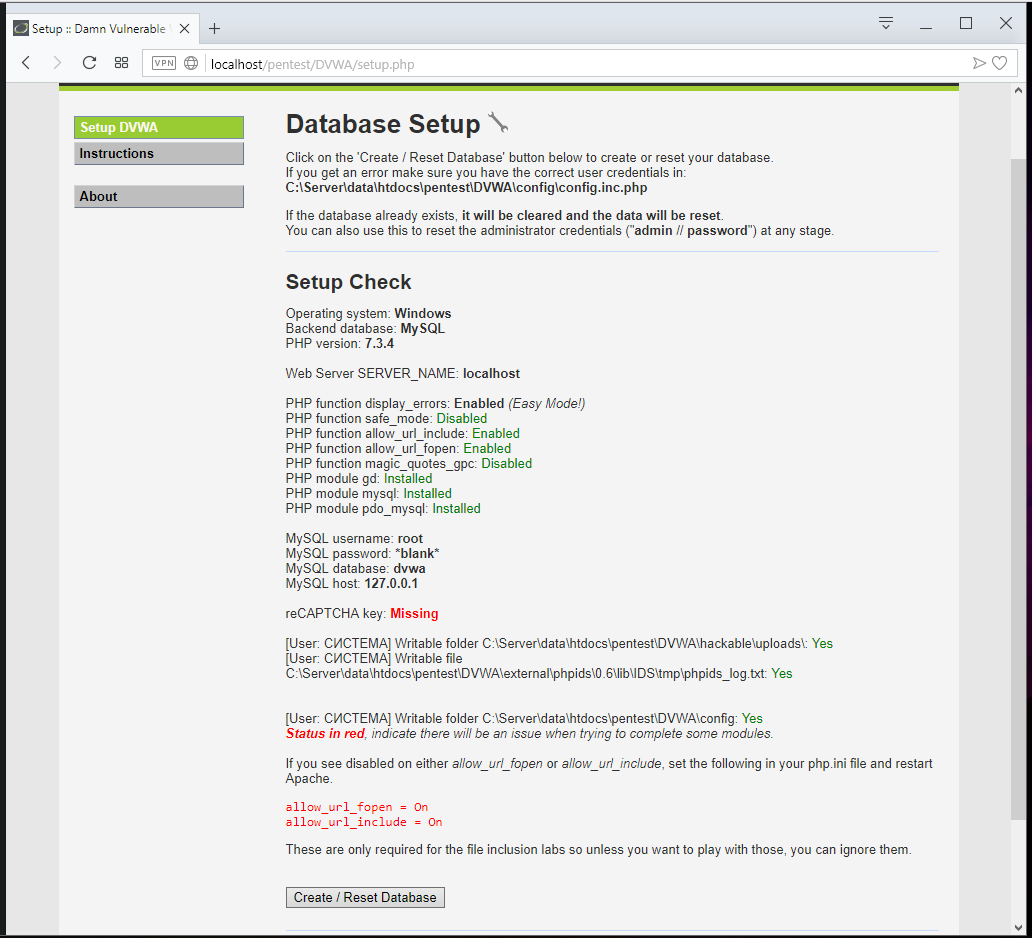
Open http://localhost/pentest/DVWA/ and click the Create / Reset Database button there:
Log in to http://localhost/pentest/DVWA/login.php:
By the way, username: admin, password: password.
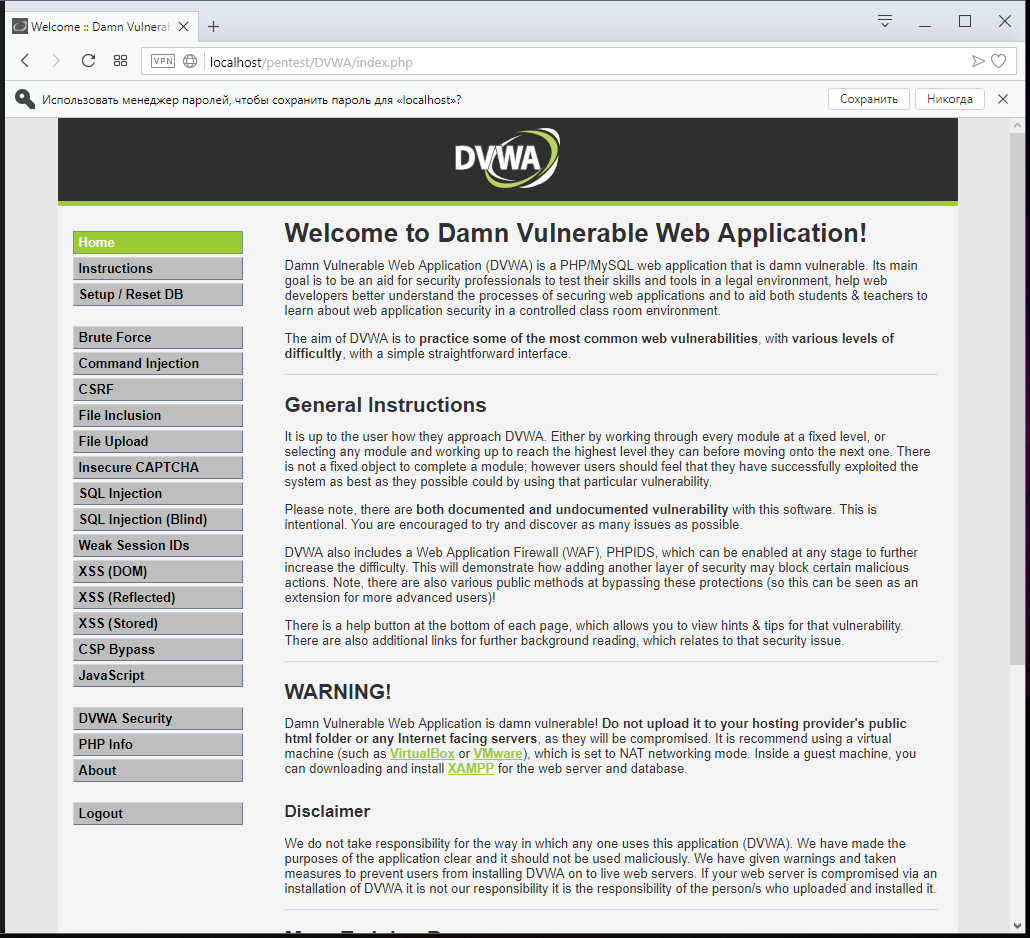
And everything is ready:
Do not forget to change the level of complexity, as the default is set to impossible, for this, go to the DVWA Security tab: http://localhost/pentest/DVWA/security.php
How to install bWAPP in Windows
Finally install and configure bWAPP in Windows
Download the latest version of bWAPP: https://sourceforge.net/projects/bwapp/files/latest/download
In the c:\Server\data\htdocs\pentest\ folder create a directory bWAPP. Extract the contents of the bWAPP_latest.zip archive to the c:\Server\data\htdocs\pentest\bWAPP\ directory.
Open the c:\Server\data\htdocs\pentest\bWAPP\bWAPP\admin\settings.php file and find the line in it:
$db_password = "bug";
In this line, change the bug to the password of your MySQL (empty by default). Save and close this file.
Follow http://localhost/pentest/bWAPP/bWAPP/install.php the link.
Find Click here to install there bWAPP and the http://localhost/pentest/bWAPP/bWAPP/install.php?install=yes link – click on it.
Everything is ready, go to http://localhost/pentest/bWAPP/bWAPP/
Username: bee, password: bug
Note: unfortunately, due to the fact that bWAPP has not been updated for a long time, some of its pages are not compatible with new versions of PHP. For example, pages for practicing SQL injections will generate an error due to the use of the mysql_connect() function. In principle, there are no special problems in fixing – just move to mysqli_connect(). To do this, edit the c:\Server\data\htdocs\pentest\bWAPP\bWAPP\connect.php file (you can simply copy the contents of c:\Server\data\htdocs\pentest\bWAPP\bWAPP\connect_i.php into it, and also all files of the type c:\Server\data\htdocs\pentest\bWAPP\bWAPP\sqli_*.php.
If you wish, you can do it yourself – a bonus exercise. Or simply use the other vulnerable environments discussed above to practice using SQL injection.
Conclusion
If you have installed a web server specifically for training in vulnerable web applications and you are afraid that the server may impair the security of your computer, then you can disable the web server after practicing penetration testing.
To disable the web server and remove its services from startup, run:
c:\Server\bin\Apache24\bin\httpd.exe -k stop c:\Server\bin\Apache24\bin\httpd.exe -k uninstall net stop mysql c:\Server\bin\mysql-8.0\bin\mysqld --remove
In this case, the server will be completely disabled, as if it is not on the computer at all, but the sites and databases will remain.
The next time you go back to practice and you will need a web server, start all the services you need:
c:\Server\bin\Apache24\bin\httpd.exe -k install c:\Server\bin\Apache24\bin\httpd.exe -k start C:\Server\bin\mysql-8.0\bin\mysqld --install net start mysql
After the work is finished, stop the web server services again, as shown above.
Troubleshooting
Error (Mutillidae):
By default, Mutillidae only allows access from localhost (127.*.*.*). Edit the .htaccess file to change this behavior (not recommended on a public network).
Solution:
This message states that by default Mutillidae only allows access from 127.*.*.*. It also suggests changing the .htaccess file if you want to change this behavior, which is not recommended in public networks.
This error may occur even if you actually open Mutillidae on the local computer. The fact is that the authors have forgotten about IPv6, and in Windows, when accessing localhost, the local IPv6 address is used, which is not provided in the original .htaccess. Therefore, to remedy the situation without weakening the protection, open the .htaccess file, find and delete the lines there
Order Deny,Allow Deny from all ## This allows access from localhost Allow from 127. Allow from localhost ## This is to allow access from other machines on Virtual Box host-only networks. Allow from 192.168.0.0/16
and add the lines instead:
Require ip 127 Require ip 192.168 Require ip ::1
Error (DVWA):
DVWA System error - config file not found. Copy config/config.inc.php.dist to config/config.inc.php and configure to your environment.
Solution:
You need to copy or rename the config/config.inc.php.dist file in config/config.inc.php, and also enter the username and password of your MySQL server there.
Error (bWAPP):
Warning: mysqli::__construct(): (HY000/1045): Access denied for user 'root'@'localhost' (using password: YES) in C:\Server\data\htdocs\pentest\bWAPP\bWAPP\connect_i.php on line 23 Connection failed: Access denied for user 'root'@'localhost' (using password: YES)
And also:
Fatal error: Uncaught Error: Call to undefined function mysql_connect() in C:\Server\data\htdocs\pentest\bWAPP\bWAPP\connect.php:23 Stack trace: #0 C:\Server\data\htdocs\pentest\bWAPP\bWAPP\sqli_3.php(23): include() #1 {main} thrown in C:\Server\data\htdocs\pentest\bWAPP\bWAPP\connect.php on line 23
Fatal error: Uncaught Error: Call to undefined function mysql_query() in C:\Server\data\htdocs\pentest\bWAPP\bWAPP\sqli_3.php:144 Stack trace: #0 {main} thrown in C:\Server\data\htdocs\pentest\bWAPP\bWAPP\sqli_3.php on line 144
The error is caused by the mysql_connect() function, which is not defined (unknown).
This extension, mysql_connect, has been deprecated since PHP 5.5.0, and has been removed in recent PHP versions. Use MySQLi or PDO_MySQL instead. Alternatives for this feature:
- mysqli_connect()
- PDO::__construct()
If you encounter this error, contact the author to correct it, or edit the source code by yourself to switch from mysql_connect() to mysqli_connect().
Related articles:
- How to hack websites (56.9%)
- How to hack websites (part 2) (56.9%)
- JavaScript Attacks (56.9%)
- Command injection: exploitation and automated vulnerability search (56.9%)
- How to exploit blind command injection vulnerability (56.9%)
- How to install Windows on a USB storage (RANDOM - 14.3%)