How to redirect all traffic through the Tor network
This article is about the capabilities and limitations of the Tor network, as well as about several programs that will increase your anonymity by hiding the real IP. This article is recommended for reading even if you use a Linux distribution that can enable anonymous mode with a couple clicks.
How to use Tor as a transparent proxy
The Tor network is primarily intended to ensure anonymity of users when accessing the Internet by hiding their real IP address. The data transmitted over the network is encrypted, but on the exit node that makes a direct request to the site and receives a response from it, the traffic is in its original state (that is, the traffic that is encrypted by third-party means, for example, HTTPS, it is encrypted, and the traffic transmitted in plain text, available for the exit node in plain text).
The Tor network is primarily designed to access websites, for this reason, and also to avoid collecting user fingerprints (for example, the version of the operating system by the features of network packets), the Tor network supports a very limited set of transmitted traffic. For example, through the Tor network, you can make a request to a website (TCP protocol), but it is impossible to transmit UDP packets or raw packets (everything is forbidden except for a full connection to websites).
The Tor network is suitable for:
- hiding IP from a website you are connecting to
- site blocking bypass
- DNS queries through Tor (DNS is needed to obtain the IP addresses of websites – your browser and system constantly send these queries). In this case, UDP packets are not used, and the data is transmitted in encrypted form
- for scanning open ports by creating a full connection (slower and more noticeable compared to the half-open connection method)
For this reason, when we say “redirect all traffic through Tor” we really mean “redirect all traffic supported by this network through Tor”.
A significant part of the traffic simply cannot be sent through the Tor network, for example, ping, some traceroute methods, scanning with half-open connections, DNS queries via UDP protocol, etc. Based on this, another question arises – what to do with traffic that cannot be transmitted through Tor network: send to the target host bypassing the Tor network or block?
Proxies or iptables for traffic redirection
When configuring the system to use Tor, you can choose different implementation options: proxies or iptables.
When setting up a proxy, you need to remember that Tor works as a SOCKS proxy – not all programs support this protocol. But the most unpleasant thing may be that if system-wide proxy settings are set, then some programs can ignore these settings and connect to remote hosts directly, bypassing proxies and Tor.
In this sense, the iptables program is a more reliable and universal option, which, if configured correctly, will ensure that a particular type of traffic cannot exit the system except through the Tor network, or it will be blocked.
Programs to redirect all traffic through Tor
So, as we already learned, we need to solve a number of problems for working correctly with Tor:
- redirect traffic correctly
- block network packets that cannot be forwarded through Tor
- configure the lookup of DNS queries through Tor
- take care of IPv6 traffic or block it
- quickly restore the system to its original state, since the Tor network is slow and not always needed
For this reason, there are many programs from different authors that implement the described functionality.
Services for finding IP address leaks
The main criteria for choosing a tool to ensure the anonymity of your operating system is the functionality and quality of ensuring anonymity (reliability of redirecting and blocking traffic). You can rate the level of anonymity using the following services:
- Identification of the use of anonymization tools: https://2ip.ru/privacy/
- Search for leaks of your IP or other data important for anonymity: https://whatleaks.com/
- Checking your IP, location and Internet service provider, there is support for IPv6 addresses: https://w-e-b.site/?act=myip
- Service for searching proxy headers and open ports, typical for anonymization tools: https://w-e-b.site/?act=proxy-checker
- Check if you use the Tor network: https://check.torproject.org/ (ATTENTION: be very careful with this service – it does not support IPv6. If traffic routing is not configured on your computer, this service will write that Tor is used, although all IPv6 traffic can go directly, revealing your IPv6 address!)
- Search for various leaks: http://www.doileak.com/
- DNS Leak Search: https://dnsleaktest.com/
- What every web browser knows about you: https://webkay.robinlinus.com/
To check the IPv6 address on the command line and whether IPv6 protocol is blocked:
curl -6 suip.biz/ip/
To check your IP address on the command line:
curl suip.biz/ip/
To check the DNS server used:
dig suip.biz | grep SERVER
orjail
Although all the programs discussed below are slightly different, let's start with the most unusual of them. It is called orjail. The program at the time of launch creates its own network environment for the program to be launched, and in this environment the program can access the Internet only through the Tor network.
Install orjail on Kali Linux
sudo apt install tor bc firejail git clone https://github.com/orjail/orjail cd orjail sed -i 's/USERHOME=$(getent passwd les | cut -d: -f 6)/USERHOME=$(getent passwd $USER | cut -d: -f 6)/' ./usr/sbin/orjail sed -i 's/chown "$USERNAME" "$TORCONFIGFILE"/#chown "$USERNAME" "$TORCONFIGFILE"/' ./usr/sbin/orjail sudo make install
Install orjail on BlackArch
sudo pacman -S orjail sudo sed -i 's/chown "$USERNAME" "$TORCONFIGFILE"/#chown "$USERNAME" "$TORCONFIGFILE"/' /usr/bin/orjail
If you want the PROGRAM to go online through Tor, then run a command of the form:
sudo orjail PROGRAM OPTIONS
For example, the following command shows the external IP of your computer:
curl suip.biz/ip/
Now run the same command with orjail:
sudo orjail curl suip.biz/ip/
Note that the Tor service does not have to be running. The orjail program itself creates virtual network interfaces, starts a new instance of the Tor service itself, and when the main program exits, it stops Tor and removes the temporary network interfaces.
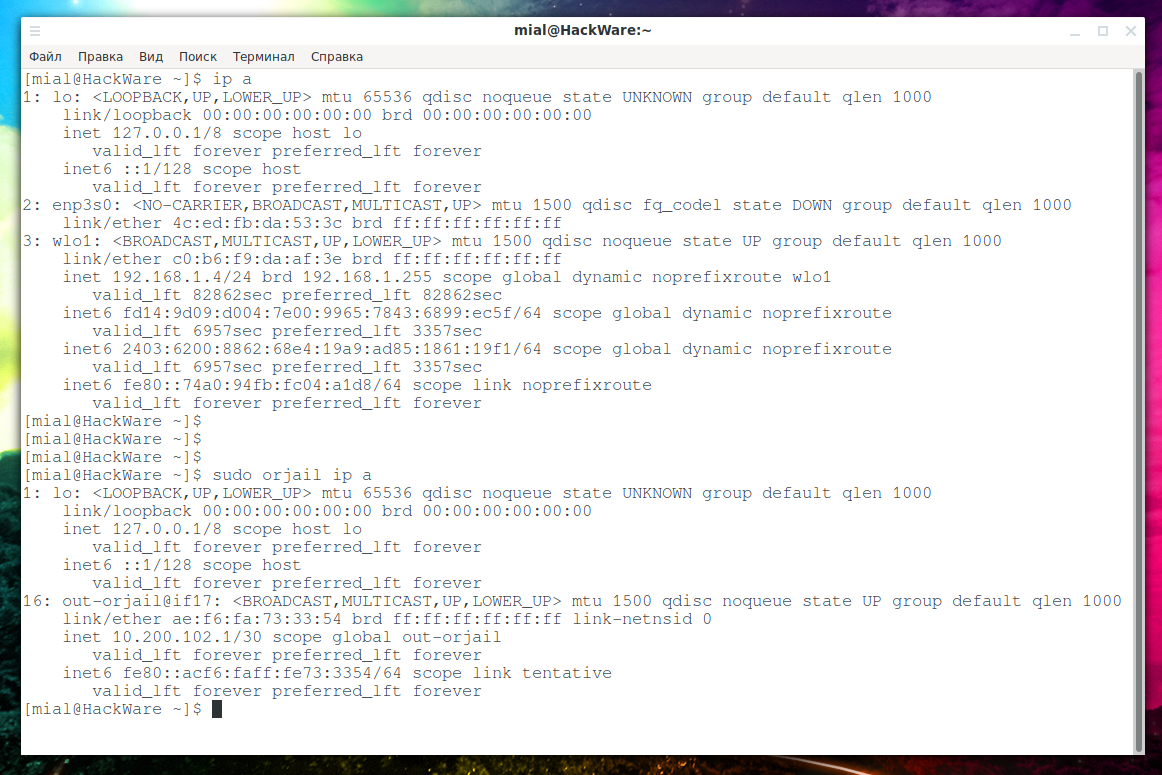
To see this clearly, view information about your network interfaces:
ip a
Now look at what programs launched with orjail see:
sudo orjail ip a
They are in a completely different environment!
You can run programs with a graphical user interface:
sudo orjail firefox -P /tmp/tmpprofile
But be careful with web browsers: orjail is rather a super fast solution when you need to bypass web sites blocking or change your IP. In more serious situations, use Tor Browser – this is safer.
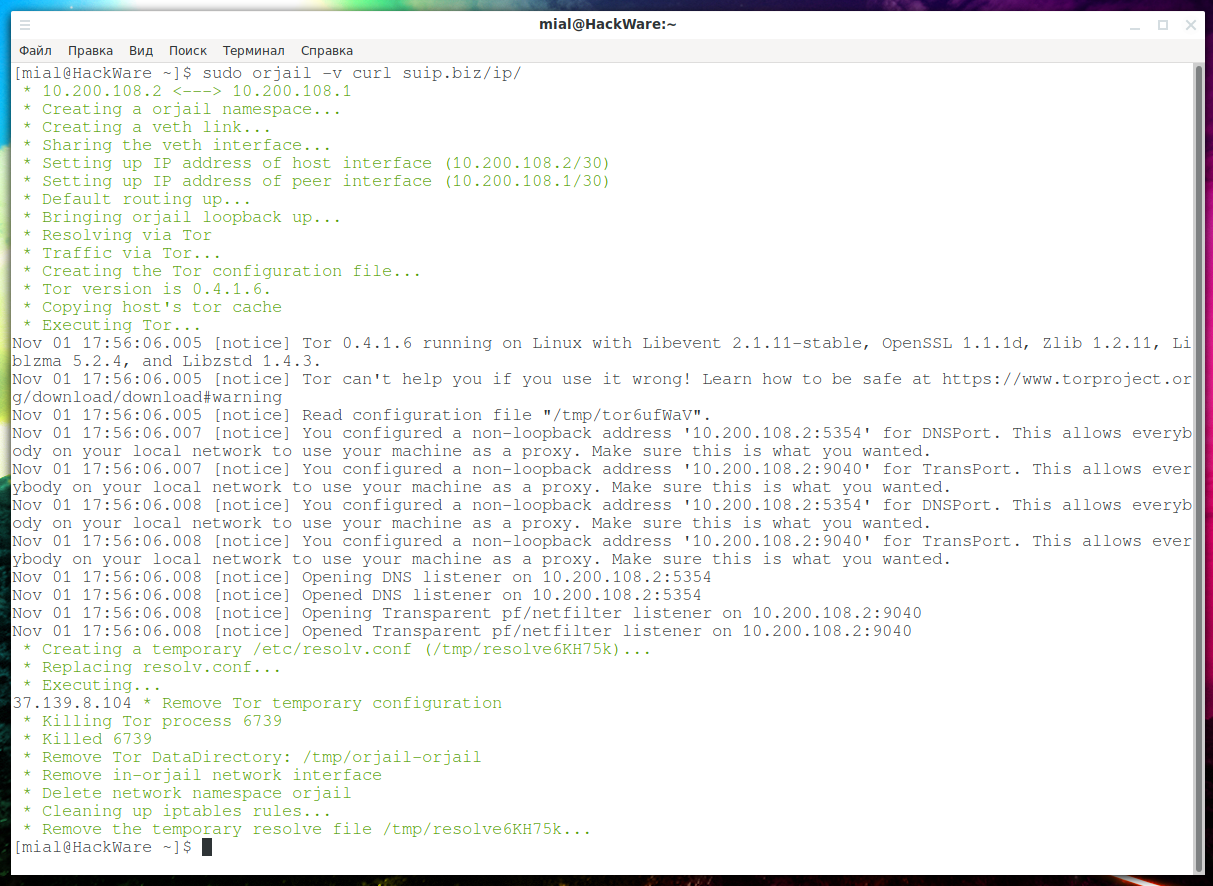
If you run orjail with the -v option, you can see all the processes in progress:
sudo orjail -v curl suip.biz/ip/
Please note that orjail is not able to work with the IPv6 protocol! The fact is that only IP addresses are assigned to the temporary network interfaces that are created. I think adding support for IPv6 is not difficult, but at the moment IPv6 traffic just does not go anywhere.
As we already know, it is impossible to transmit UDP protocol packets through Tor, however, orjail can perform DNS queries:
sudo orjail dig suip.biz
Server from which the DNS response is received is something like:
10.200.194.2#53
That is, DNS queries are processed on the Tor network.
orjail Troubleshooting
Error ‘User root: invalid name or no home directory.’
You may encounter an error:
User root: invalid name or no home directory.
where instead of “root” will be your username.
So the error looks when displaying debugging information:
User root: invalid name or no home directory. [Error] in command: exit 1 * Remove Tor temporary configuration * Killing Tor process * Killed * Remove Tor DataDirectory: /tmp/orjail-orjail * Remove in-orjail network interface Cannot find device "in-orjail" * Delete network namespace orjail Cannot remove namespace file "/run/netns/orjail": No such file or directory * Cleaning up iptables rules...
To fix, open the orjail file (if you have already installed it, this file is located on the path /usr/sbin/orjail), find the line there
USERHOME=$(getent passwd les | cut -d: -f 6)
And replace with:
USERHOME=$(getent passwd $USER | cut -d: -f 6)
Error ‘./usr/sbin/orjail: line 563: /tmp/torpVKzn4: Access denied’
Error example:
sudo ./usr/sbin/orjail curl suip.biz/ip/
./usr/sbin/orjail: строка 563: /tmp/torpVKzn4: Access denied
[Error] in command: cat >> "$TORCONFIGFILE" <<EOF
DataDirectory /tmp/orjail-${NAME}
AutomapHostsSuffixes .onion,.exit
AutomapHostsOnResolve 1
PidFile /tmp/orjail-${NAME}/pid
User ${USERNAME}
VirtualAddrNetworkIPv4 ${IPNETNS}/16
TransPort ${IPHOST}:${TRANSPORT}
DNSPort ${IPHOST}:${DNSPORT}
SOCKSPort 0
RunAsDaemon 1
EOF
[Error] Enable verbose mode to debug (using -v)
Instead of /tmp/torpVKzn4 there can be any arbitrary name.
To fix, open the orjail file again (if you have already installed it, this file is located on the path /usr/sbin/orjail), find the line there
chown "$USERNAME" "$TORCONFIGFILE"
and replace with
#chown "$USERNAME" "$TORCONFIGFILE"
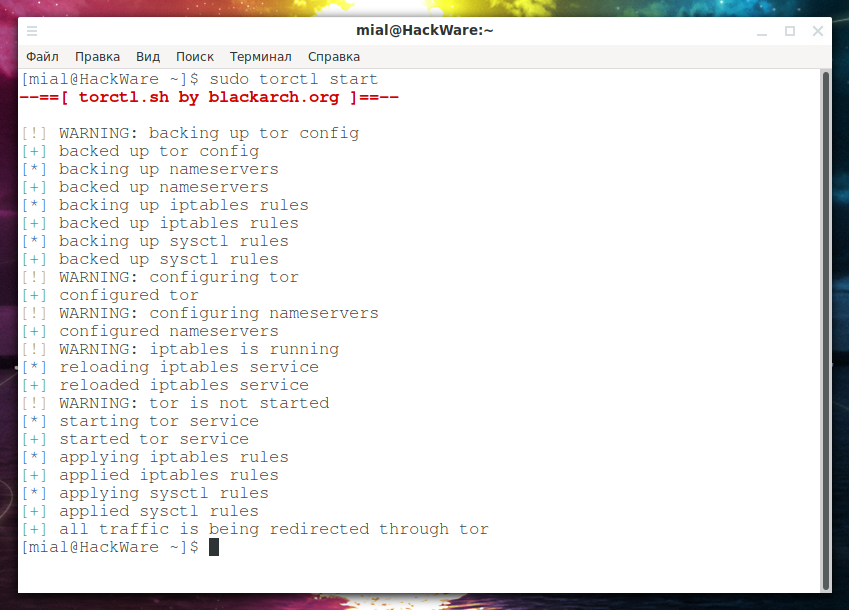
torctl
Further programs are very similar, they all use Tor + iptables, but everything is slightly different.
Let's start with the most versatile torctl program.
This program is written for BlackArch, but it is quite easy to port to other distributions.
Install torctl on Kali Linux
sudo apt install tor macchanger secure-delete git clone https://github.com/BlackArch/torctl cd torctl sudo mv service/* /etc/systemd/system/ sudo mv bash-completion/torctl /usr/share/bash-completion/completions/torctl sed -i 's/start_service iptables//' torctl sed -i 's/TOR_UID="tor"/TOR_UID="debian-tor"/' torctl sudo mv torctl /usr/bin/torctl cd .. && rm -rf torctl/ torctl --help
Install torctl in BlackArch
sudo pacman -S torctl
To find out your current IP, do:
torctl ip
To start Tor as a transparent proxy:
sudo torctl start
To check the status of services:
torctl status
If you want to change the IP on the Tor network:
sudo torctl chngid
To work with the Internet directly, without Tor, run:
sudo torctl stop
To change the MAC address on all network interfaces, run the command:
sudo torctl chngmac
To recover the original MAC addresses:
sudo torctl rvmac
The following command will add the torctl service to startup, that is, immediately after turning on the computer, all traffic will be sent through Tor:
sudo systemctl enable torctl-autostart.service
To remove a service from startup, do:
sudo systemctl disable torctl-autostart.service
You can also enable automatic memory cleaning every time you turn off the computer:
sudo systemctl enable torctl-autowipe.service
To disable this function:
sudo systemctl disable torctl-autowipe.service
This script knows about the existence of IPv6 traffic and successfully blocks it. DNS queries are redirected through Tor.
Anonsurf
If you are familiar with Parrot Linux, then AnonSurf should also be familiar to you - it enables anonymity mode in the system. AnonSurf optionally closes programs that can compromise anonymity, redirects traffic and DNS queries through Tor, and blocks IPv6.
AnonSurf is too integrated in Parrot Linux and on other systems I would recommend choosing some other option, fortunately, there is a choice. I also don’t like the fact that the program tries to start/stop some services without checking their availability and displays errors if they are missing – because of the excess of unnecessary information, you can skip something really important. However, the following shows how to install AnonSurf on Kali Linux. Most of the functionality has been saved, but the “dns - Replacing Your DNS with OpenNIC DNS Servers” command will not work!
Install AnonSurf on Kali Linux
sudo apt install tor git clone https://github.com/ParrotSec/anonsurf cd anonsurf sudo make install sudo mkdir -p /etc/resolvconf/run/ sudo cp /etc/resolv.conf /etc/resolvconf/run/resolv.conf sudo mv /etc/tor/torrc /etc/tor/torrc.back sed 's/9061/53/' /etc/tor/torrc.back > /etc/tor/torrc sed 's/9051/9040/' /etc/tor/torrc.back > /etc/tor/torrc sed -i 's/ln -s \/etc\/resolvconf\/run\/resolv.conf \/etc\/resolv.conf || true//' /usr/bin/anonsurf sed -i 's/rm \/etc\/resolv.conf || true/mv \/etc\/resolv.conf.bak \/etc\/resolv.conf || true/' /usr/bin/anonsurf sed -i 's/\/usr\/sbin\/service tor stop/systemctl stop tor/' /usr/bin/anonsurf anonsurf --help
Display your external IP address:
sudo anonsurf myip
Redirecting all traffic through the Tor network:
sudo anonsurf start
Stopping traffic redirect through Tor:
sudo anonsurf stop
Nipe
Nipe is a script that makes the Tor network your default gateway.
This Perl script allows you to directly send all your traffic from your computer to the Tor network, through which you can anonymously access the Internet, without worrying that your IP will be monitored IP or your identity will be revealed.
Nipe currently only supports IPv4, but work is underway to add support for IPv6.
TOR Router
TOR Router allows you to use the Tor network as a transparent proxy and send all your traffic, including DNS queries, through Tor. The Tor network will become the default gateway for all Internet connections, which will increase privacy/anonymity with minimal effort. The script will work on any system using systemd (if you want to use this tool as a service) and tor.
TOR Router does not change system files, as other tools for routing your traffic, due to minimal impact on the system, in the case of a mistake in the TOR Router service or after uninstalling this tool, your Internet connection will not be affected.
Currently, Tor-router only supports IPv4 traffic, but the author plans to add support for IPv6.
TorIptables2
TorIptables2 script is an anonymizer that configures iptables and tor to redirect all services and traffic, including DNS, through the Tor network.
I already talked about this script in more detail in the article “Free easy way to hide IP in Linux”.
I would not recommend using the last three scripts until IPv6 is added to them, otherwise you can accidentally mess up a lot…
autovpn
This program is added as a bonus – autovpn also allows you to quickly change the IP address, but instead of Tor uses a random public OpenVPN from the specified country. More details in the article “Free easy way to hide IP in Linux”.
Let's look at a few more uses for the Tor network.
Tor browser
Tor Browser is a fully configured and portable browser for browsing websites through the Tor network. The advantages of this option are additional measures for anonymity.
Cons follow from the pros: the more measures for anonymity, the more inconvenient to use.
Tutorials for setting up and using Tor
- Anonymous scanning through Tor with Nmap, sqlmap or WPScan
- How to make proxy with Tor in Windows
- How to install Tor and create Tor hidden service on Windows
- How to install and run Tor Browser on Kali Linux
An article on fine-tuning Tor is also being prepared. Thanks to fine-tuning, you can, for example, exclude nodes from certain countries from the traffic path, or vice versa to make the exit node always located in a specific country or countries – thanks to this, you can make sure that you always have the IP of the desired country.
Related articles:
- Errors in Kali Linux ‘W: Failed to fetch’ and ‘W: Some index files failed to download. They have been ignored, or old ones used instead.’ (SOLVED) (69.5%)
- What to select: Tor, VPN, or proxy? (66.9%)
- How to connect to OpenVPN via proxy or Tor (64.4%)
- autovpn2 and autovpn3 - scripts to automatically connect to a free VPNs (62.5%)
- How to save and open website pages in Tails in a web browser (61.7%)
- How to find out if a site is behind CloudFlare or not (RANDOM - 0.8%)

Such a good article. I have been mindlessly surfing the internet grinding my teeth as to why there is no tor based vpn for desktop. You have very clearly and comprehensively written all the information in one place. Great work (:
I completely agree, this is by far the only article i could find on the topic that is both detailed and easy to understand. Great work!