How to Install and run WPScan on Windows
WPScan is a vulnerability scanner for WordPress powered sites. It is a ‘black box’ scanner, that is, it operates without access to website source code. It can be used to discover security issues of remote WordPress sites.
The vulnerability search process is as follows:
- For the specified site, it searches for installed plugins and themes. Since plugins are placed in the same folders on all sites, it can determine the availability of the plugin by making a request to a specific file. Attempts are also being made to determine the versions for plugins and to detect themes.
- If a plugin is found, then the database checks if it has any known vulnerabilities.
- Additionally, the version of WordPress is determined and known vulnerabilities for this version are displayed.
- Backup files and databases are also searched, a robots.txt file is analyzed, a list of users and other information useful to the site security auditor are displayed.
WPScan is usually used on Linux, this program is already preinstalled on distributions such as Kali Linux and BlackArch. WPScan is written in Ruby and can be run on any operating system that supports Ruby, including Windows. When using WPScan in Windows, there are some nuances that will be discussed later.
To install WPScan on Windows, you need to start by installing Ruby, as described in this article.
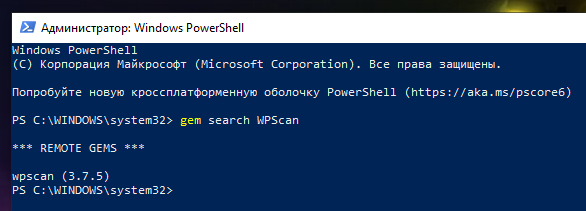
Let’s search WPScan among the gem packages:
gem search WPScan
Found wpscan (3.7.5) package, which is the latest version of WPScan. To install, just type:
gem install wpscan
Now you need to update the WPScan database with information about plugins and WordPress themes:
wpscan --update --disable-tls-checks
If the error “Could not open library 'libcurl.dll', 'libcurl.so.4', 'libcurl.so.4.dll'” occurs during startup, then see its solution here.
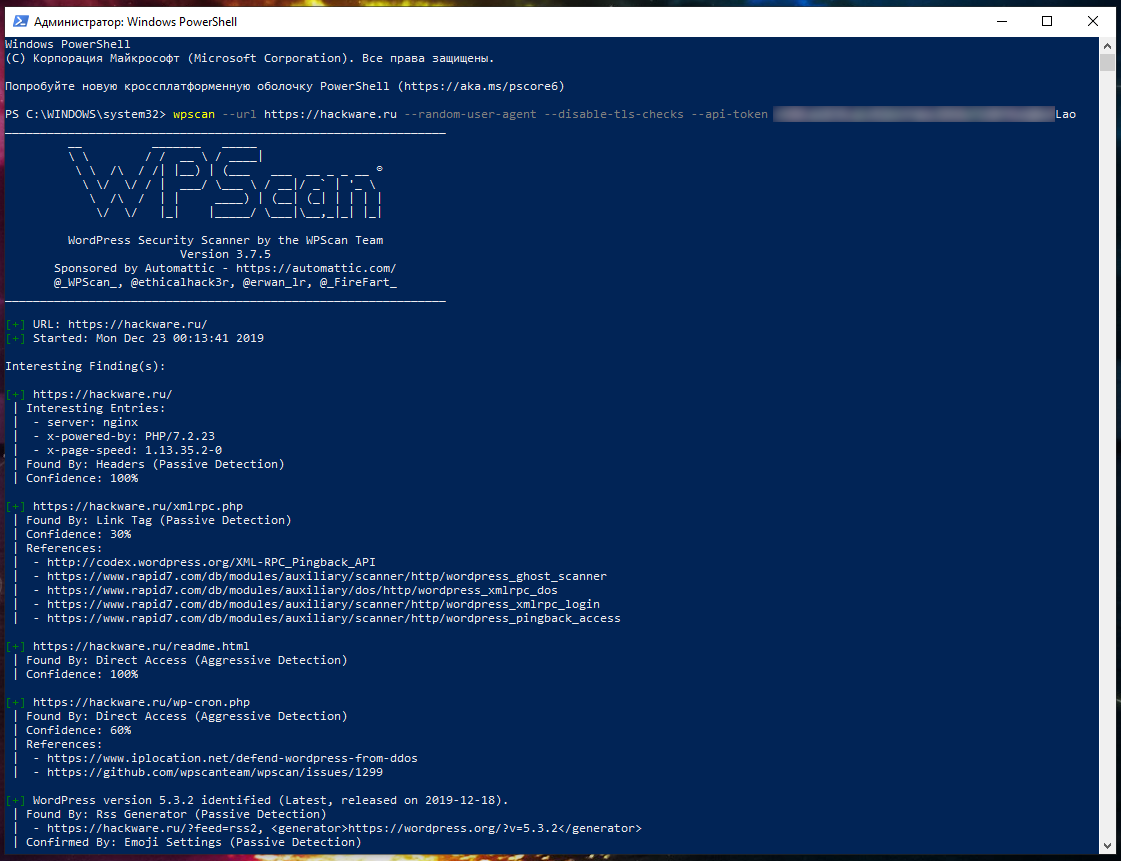
To run WordPress site scanning on Windows using WPScan, run a command of the form:
wpscan --url https://DOMAIN --random-user-agent --disable-tls-checks
For example, I want to scan the URL https://hackware.ru:
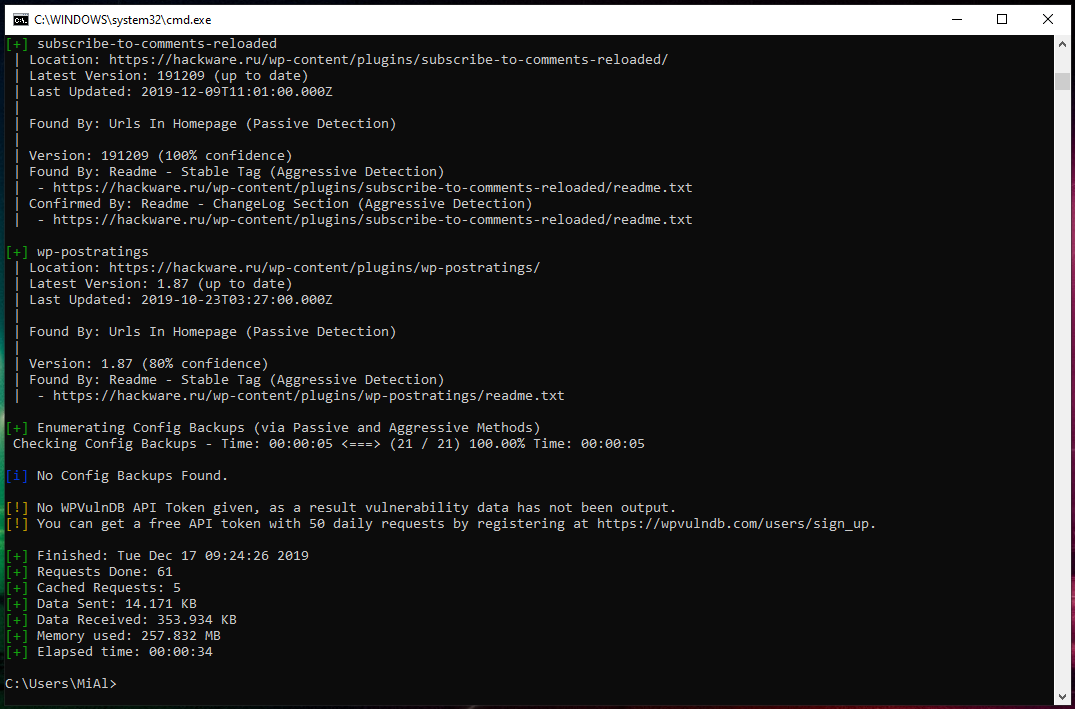
wpscan --url https://hackware.ru --random-user-agent --disable-tls-checks
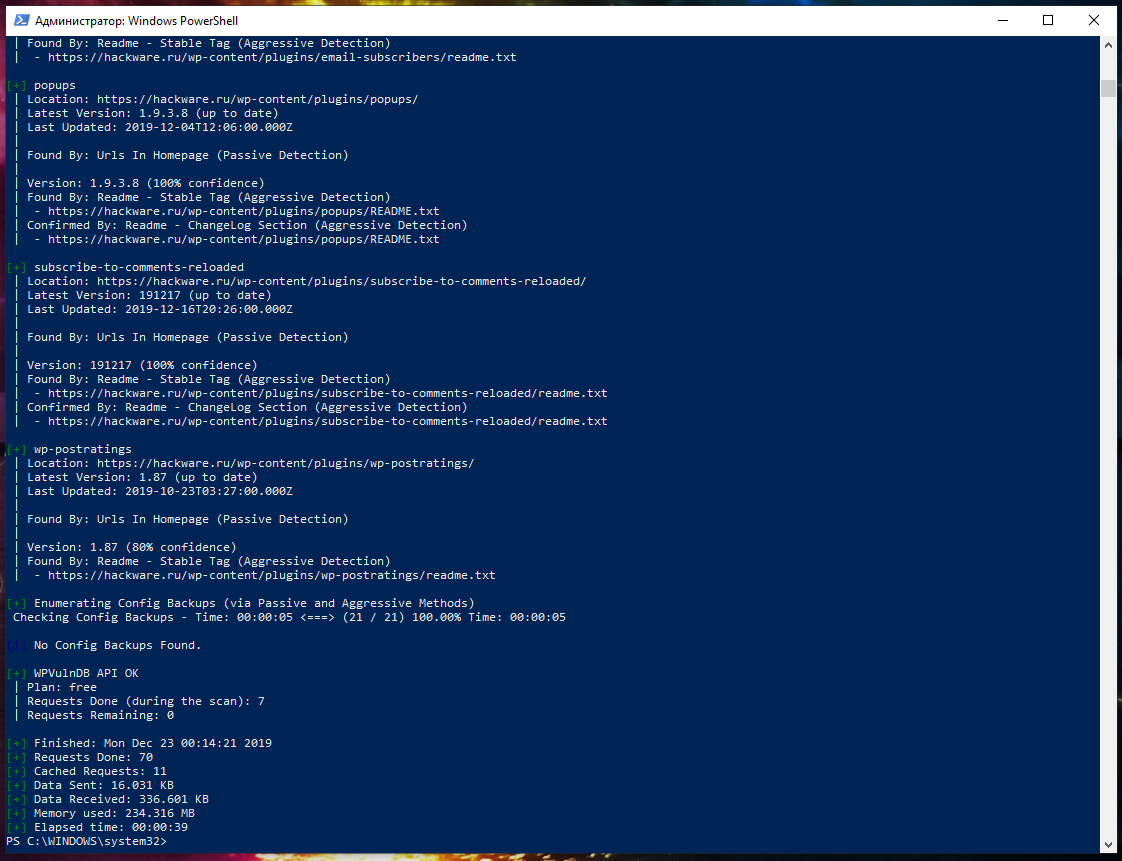
Why WPScan does not show vulnerabilities. How to get WPVulnDB API
Previously, WPScan displayed versions of found plugins and themes, and if a plugin or theme has vulnerabilities, then it displayed them. Now WPScan only shows versions of WordPress, plugins and themes, but does not display vulnerabilities. Instead, the following messages are shown at the end of the scan:
[!] No WPVulnDB API Token given, as a result vulnerability data has not been output. [!] You can get a free API token with 50 daily requests by registering at https://wpvulndb.com/users/sign_up.
There is no catch — just go ahead, sign up and get your free token.
Then add the --api-token option to the command to run:
wpscan --url https://DOMAIN --random-user-agent --disable-tls-checks --api-token API_KEY
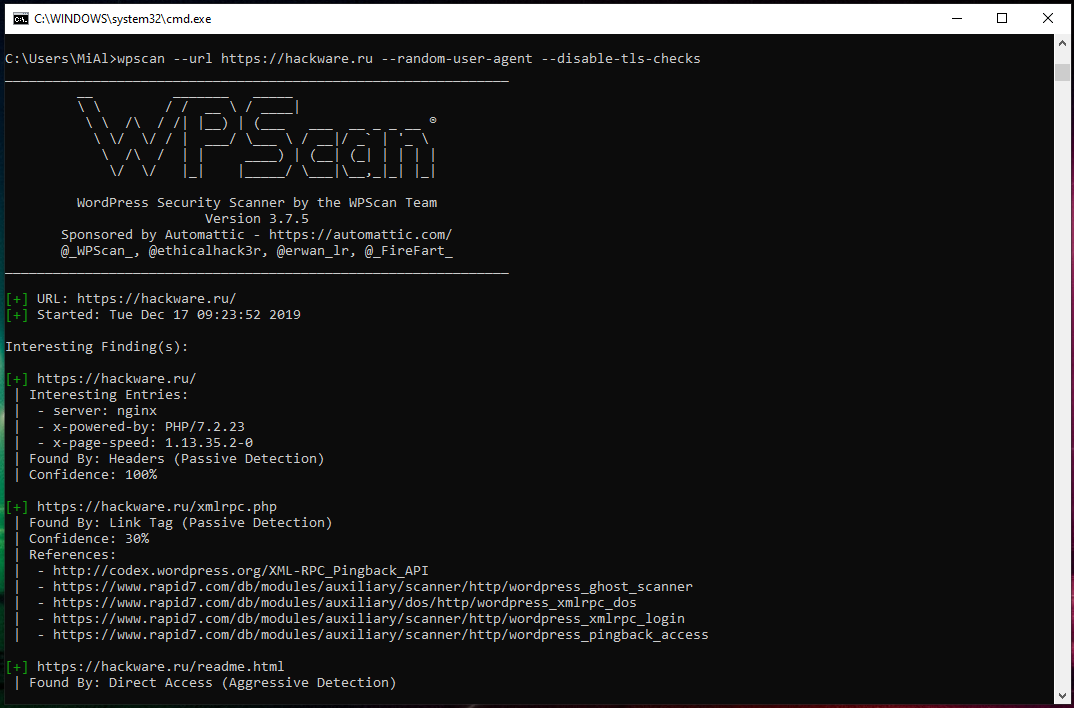
Example scan without an API key:
More information and services
- 5 free and simple steps to secure WordPress web sites
- How to check WordPress sites for vulnerabilities (WPScan)
- Black box WordPress vulnerability scanner online: https://w-e-b.site/?act=wpscan&color=on
- Anonymous scanning through Tor with Nmap, sqlmap or WPScan
Troubleshooting
SSL peer certificate or SSH remote key was not OK
When updating the database, an error may occur:
[i] Updating the Database ... Scan Aborted: Unable to get https://data.wpscan.org/metadata.json.sha512 (SSL peer certificate or SSH remote key was not OK)
The same error can occur when scanning a site using the HTTPS protocol:
Scan Aborted: The url supplied 'https://hackware.ru/' seems to be down (SSL peer certificate or SSH remote key was not OK)
To fix this, add the option --disable-tls-checks to your command, for example:
wpscan --update --disable-tls-checks
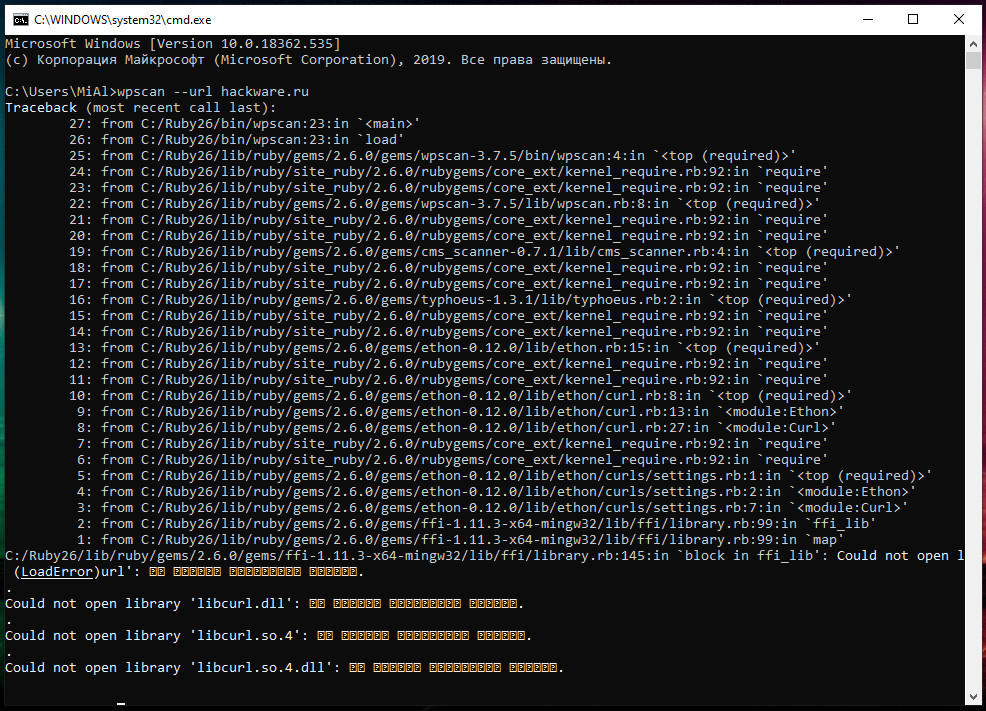
Could not open library 'libcurl.dll', 'libcurl.so.4', 'libcurl.so.4.dll'
When starting WPScan on Windows:
wpscan --url hackware.ru
You may encounter this error:
Traceback (most recent call last):
27: from C:/Ruby26/bin/wpscan:23:in `<main>'
26: from C:/Ruby26/bin/wpscan:23:in `load'
25: from C:/Ruby26/lib/ruby/gems/2.6.0/gems/wpscan-3.7.5/bin/wpscan:4:in `<top (required)>'
24: from C:/Ruby26/lib/ruby/site_ruby/2.6.0/rubygems/core_ext/kernel_require.rb:92:in `require'
23: from C:/Ruby26/lib/ruby/site_ruby/2.6.0/rubygems/core_ext/kernel_require.rb:92:in `require'
22: from C:/Ruby26/lib/ruby/gems/2.6.0/gems/wpscan-3.7.5/lib/wpscan.rb:8:in `<top (required)>'
21: from C:/Ruby26/lib/ruby/site_ruby/2.6.0/rubygems/core_ext/kernel_require.rb:92:in `require'
20: from C:/Ruby26/lib/ruby/site_ruby/2.6.0/rubygems/core_ext/kernel_require.rb:92:in `require'
19: from C:/Ruby26/lib/ruby/gems/2.6.0/gems/cms_scanner-0.7.1/lib/cms_scanner.rb:4:in `<top (required)>'
18: from C:/Ruby26/lib/ruby/site_ruby/2.6.0/rubygems/core_ext/kernel_require.rb:92:in `require'
17: from C:/Ruby26/lib/ruby/site_ruby/2.6.0/rubygems/core_ext/kernel_require.rb:92:in `require'
16: from C:/Ruby26/lib/ruby/gems/2.6.0/gems/typhoeus-1.3.1/lib/typhoeus.rb:2:in `<top (required)>'
15: from C:/Ruby26/lib/ruby/site_ruby/2.6.0/rubygems/core_ext/kernel_require.rb:92:in `require'
14: from C:/Ruby26/lib/ruby/site_ruby/2.6.0/rubygems/core_ext/kernel_require.rb:92:in `require'
13: from C:/Ruby26/lib/ruby/gems/2.6.0/gems/ethon-0.12.0/lib/ethon.rb:15:in `<top (required)>'
12: from C:/Ruby26/lib/ruby/site_ruby/2.6.0/rubygems/core_ext/kernel_require.rb:92:in `require'
11: from C:/Ruby26/lib/ruby/site_ruby/2.6.0/rubygems/core_ext/kernel_require.rb:92:in `require'
10: from C:/Ruby26/lib/ruby/gems/2.6.0/gems/ethon-0.12.0/lib/ethon/curl.rb:8:in `<top (required)>'
9: from C:/Ruby26/lib/ruby/gems/2.6.0/gems/ethon-0.12.0/lib/ethon/curl.rb:13:in `<module:Ethon>'
8: from C:/Ruby26/lib/ruby/gems/2.6.0/gems/ethon-0.12.0/lib/ethon/curl.rb:27:in `<module:Curl>'
7: from C:/Ruby26/lib/ruby/site_ruby/2.6.0/rubygems/core_ext/kernel_require.rb:92:in `require'
6: from C:/Ruby26/lib/ruby/site_ruby/2.6.0/rubygems/core_ext/kernel_require.rb:92:in `require'
5: from C:/Ruby26/lib/ruby/gems/2.6.0/gems/ethon-0.12.0/lib/ethon/curls/settings.rb:1:in `<top (required)>'
4: from C:/Ruby26/lib/ruby/gems/2.6.0/gems/ethon-0.12.0/lib/ethon/curls/settings.rb:2:in `<module:Ethon>'
3: from C:/Ruby26/lib/ruby/gems/2.6.0/gems/ethon-0.12.0/lib/ethon/curls/settings.rb:7:in `<module:Curl>'
2: from C:/Ruby26/lib/ruby/gems/2.6.0/gems/ffi-1.11.3-x64-mingw32/lib/ffi/library.rb:99:in `ffi_lib'
1: from C:/Ruby26/lib/ruby/gems/2.6.0/gems/ffi-1.11.3-x64-mingw32/lib/ffi/library.rb:99:in `map'
C:/Ruby26/lib/ruby/gems/2.6.0/gems/ffi-1.11.3-x64-mingw32/lib/ffi/library.rb:145:in `block in ffi_lib': Could not open l (LoadError)url': �� ������ ��������� ������.
.
Could not open library 'libcurl.dll': �� ������ ��������� ������.
.
Could not open library 'libcurl.so.4': �� ������ ��������� ������.
.
Could not open library 'libcurl.so.4.dll': �� ������ ��������� ������.
Its essence is that the program cannot find the libcurl.dll file it needs. Then it tries to find this file by the alternative names libcurl.so.4 and libcurl.so.4.dll, which also fails.
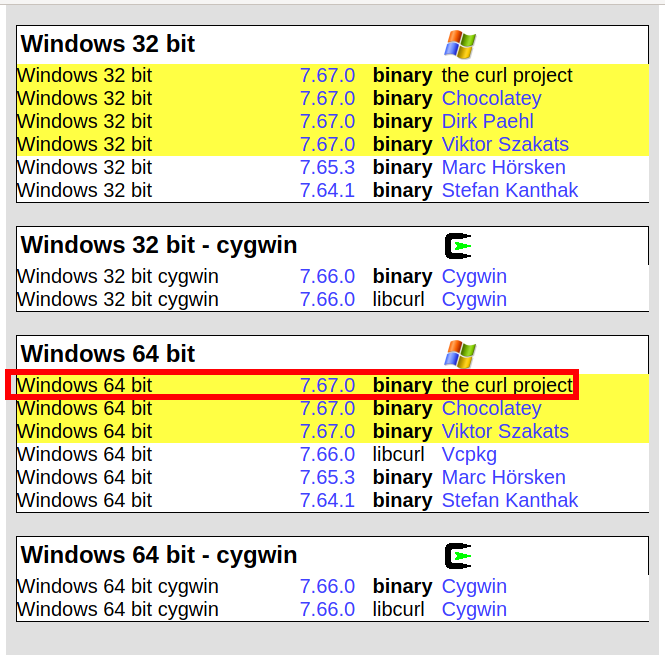
It is quite simple to fix the problem – you need to download the libcurl.dll file. To download the libcurl.dll file, go to the official cURL website and download the latest curl version for Windows there:
In the downloaded archive in the bin folder, find the file libcurl-x64.dll, unzip it and rename it to libcurl.dll. Now this file needs to be moved to the bin folder of the installed Ruby, for example, I have this folder C:\Ruby26\bin\.
After that, the problem will disappear.
Related articles:
- Best Kali Linux tools in WSL (Windows Subsystem for Linux) (Part 1) (91.6%)
- Online Kali Linux programs (FREE) (72.6%)
- JavaScript Attacks: how to bypass Social Locker for WordPress (CASE) (72%)
- Anonymous scanning through Tor with Nmap, sqlmap or WPScan (70.6%)
- 5 free and simple steps to secure WordPress web sites (69.2%)
- Hashcat manual: how to use the program for cracking passwords (RANDOM - 1.1%)
Hi Alexey,
The process above drops off at installing nokogiri 1.10.8 and won't complete wpscan installation.
Windows PowerShell
Copyright (C) 2014 Microsoft Corporation. All rights reserved.
PS C:\Windows\system32> gem search wpscan
*** REMOTE GEMS ***
wpscan (3.7.8)
PS C:\Windows\system32> gem install wpscan
ERROR: Error installing wpscan:
The last version of nokogiri (~> 1.10.4) to support your Ruby & RubyGems was 1.10.8. Try installing it with `gem
install nokogiri -v 1.10.8` and then running the current command again
nokogiri requires Ruby version >= 2.3, < 2.7.dev. The current ruby version is 2.7.0.0.
************SOLUTION****************:
PS C:\Windows\system32\wpscan> gem install nokogiri --platform=ruby
Fetching nokogiri-1.10.8.gem
Temporarily enhancing PATH for MSYS/MINGW…
Building native extensions. This could take a while…
Successfully installed nokogiri-1.10.8
Parsing documentation for nokogiri-1.10.8
Installing ri documentation for nokogiri-1.10.8
Done installing documentation for nokogiri after 3 seconds
1 gem installed
-----
Now run the wpscan installer again
PS C:\Windows\system32\wpscan> gem install wpscan
Successfully installed opt_parse_validator-1.8.1
Successfully installed ruby-progressbar-1.10.1
Successfully installed ethon-0.12.0
Successfully installed typhoeus-1.3.1
Temporarily enhancing PATH for MSYS/MINGW…
Building native extensions. This could take a while…
Successfully installed yajl-ruby-1.4.1
Successfully installed sys-proctable-1.2.2
Successfully installed cms_scanner-0.8.2
Successfully installed wpscan-3.7.8
Parsing documentation for opt_parse_validator-1.8.1
Installing ri documentation for opt_parse_validator-1.8.1
Parsing documentation for ruby-progressbar-1.10.1
Installing ri documentation for ruby-progressbar-1.10.1
Parsing documentation for ethon-0.12.0
Installing ri documentation for ethon-0.12.0
Parsing documentation for typhoeus-1.3.1
Installing ri documentation for typhoeus-1.3.1
Parsing documentation for yajl-ruby-1.4.1
Installing ri documentation for yajl-ruby-1.4.1
Parsing documentation for sys-proctable-1.2.2
Installing ri documentation for sys-proctable-1.2.2
Parsing documentation for cms_scanner-0.8.2
Installing ri documentation for cms_scanner-0.8.2
Parsing documentation for wpscan-3.7.8
Installing ri documentation for wpscan-3.7.8
Done installing documentation for opt_parse_validator, ruby-progressbar, ethon, typhoeus, yajl-ruby, sys-proctable, cms_
scanner, wpscan after 4 seconds
8 gems installed
Thank you for the webpage and information on the installation. I did register for the Vulnerability API and tried to enter it on the command line, but it keeps providing an error that it is invalid. I am entering the parameter as --api-token BaUr1J……
Is that correct, or if not, how do I set/configure an API_KEY parameter?
Hello! Yes, we have to provide the API key after the --api-token options. Please check, whether you copy-paste the key correctly?
sorry my rugby installer folder does not have a bin folder just the setup,i copyed the .dll file and pasted there in rugby installer folder right above the setup icon yet it did not work
Great post! very useful and complete
I installed WPScan on my Win10 with all gems but still have problem with start the app. When I try command C:\wpscan>ruby wpscan.rb, then occured error: [ERROR] cannot load such file -- xmlrpc/client.
My instructions do not contain these commands and I cannot help you with anything. I've just repeated the steps in my instructions – it works fine.
This is an amazing article. After trying several times, I came across this guide and was able to install both Wpscan and Ruby. wpscan works now. But, I am not able to use a wordlist or passwords txt file at all. It keeps saying The Path "root/worlist.txt' does not exist or is not a file. I have tried all possible path formats possible but it's the same error every single time.
Are file paths referenced in a different format in Ruby. I tried dragging and dropping the file into the Ruby window but that doesn't work. If someone knows how to correctly specify the wordlist file path, please share. I will greatly appreciate it. I don't have a coding background obviously.