Comprehensive Guide to John the Ripper. Part 1: Introducing and Installing John the Ripper
Table of contents
1. Introducing and Installing John the Ripper
1.2 How John the Ripper and Hashcat differ
1.3 How to install video card drivers for John the Ripper
1.3.1 Installing video drivers in Windows
1.3.2 Installing video drivers on Linux
1.4 How to compile John the Ripper on Linux from source code
1.5 How to install John the Ripper on Windows
1.7 How to use a graphics card to brute-force in John the Ripper
1.8 How to use a video CPU core in JtR
1.9 How to run John the Ripper benchmark
1.10 How to set up John the Ripper
1.11 Compilation difference with AVX2 and AVX for John the Ripper
1.12 Result for the first part
2. Utilities for extracting hashes
4. Practical examples of John the Ripper usage
6. How to brute force non-standard hashes
7, Johnny – GUI for John the Ripper
8.
9.
What is John the Ripper
John the Ripper is a popular password cracker that is capable of brute-force using both the CPU and the video card and supports many algorithms. To be more precise, this is an offline brute-forcer (online brute-forcers perform the attack by connecting to network services, and offline crackers work with captured hashes (files) to which they guess a password).
Even if you are already familiar with Hashcat (and even more so if you are NOT familiar with Hashcat), you need to learn how John the Ripper works, since they are different.
How John the Ripper and Hashcat differ
1.
Hashcat can use a video card, CPU, or both for brute-force.
John the Ripper can use one thing: either the video card, or the video core of the CPU, or only the CPU.
2.
Hashcat can use the graphics card to crack any supported algorithms.
John the Ripper for GPU Cracking supports only certain kinds of algorithms.
3.
If you have several video cards, Hashcat out of the box supports working with multiple devices at once and by default splits the task into the required number of threads and the size of each task is tied to the performance of the video card.
John the Ripper can work with multiple graphics cards, but by default, splitting a task across multiple graphics cards is only supported for one algorithm.
4.
It doesn't matter to Hashcat how you installed it: built from source or downloaded a binary file.
It is very important for John the Ripper to compile the binary himself, as the compilation takes into account the specifics of your system. As a result, during compilation, the instruction sets supported by the processor will be indicated, for example, AVX2 instead of the default AVX, which will have a very significant impact on performance – for some algorithms, this will speed up brute-forcing by 2 times! Alternatively, John's binaries compiled on newer hardware may not work on some computers.
5.
For Hashcat, you must specify the hash type.
John the Ripper determines the hash itself, or you can explicitly specify the hash format.
6.
The syntax for commands and options varies greatly.
7.
About cracking a password in John the Ripper on a video card, you need to know that brute-force on a graphics card takes a long time to launch – this is noticeable even in the benchmark. Therefore, if you need to execute many short sessions, then sometimes it is more rational to use the CPU, on which the brute-force is launched immediately.
Advantages of John the Ripper:
- John the Ripper work with hashes more flexible - even if the file with hashes contains hashes of other types, John does not exit with an error, but simply uses the hashes of the type specified in the start command. In addition, hash computation utilities often add strings that can cause an “invalid hash” error in Hashcat. John the Ripper works fine with this form of notation.
- More flexible Rule-based attack. John the Ripper and Hashcat have an implementation of Rule-based attack and the syntax for writing the rules has a lot in common. But in John the Ripper, this attack is more powerful because it has more rules and also allows character sets to be used in the rule entry.
- Support for non-standard hashes. Hashcat can only work with hashes provided by the developers of this program. And John the Ripper has a Dynamic mode that allows you to specify the formula by which the hash was calculated. That is, arbitrary types of hashes can be cracked.
How to install video card drivers for John the Ripper
If you want to use the GPU to crack passwords (which is many times faster than on the central processor), then you need to install the video driver.
For brute-force can be used:
- CPU
- video core of CPU
- GPU
You need to choose one of these – the fastest option is a video card.
Of course, the specific configurations of computers may vary: some do not have a discrete graphics card, some do not have a video core on a CPU – I hope you can check this yourself.
Installing video drivers in Windows
In this OS, everything is simple – most likely, the video drivers for your graphics card are already installed. If not, go to the manufacturer's website, download and install the driver.
In order to use the CPU as an OpenCL device, you need to install “OpenCL Runtime for Intel Core and Intel Xeon Processors”. You can find the links in this article on Hashcat, which also uses this software.
Installing video drivers on Linux
On Kali Linux
Upgrade and reboot your Kali installation:
sudo apt update && sudo apt full-upgrade -y reboot
Installing video drivers for NVIDIA on Linux
sudo apt install -y ocl-icd-libopencl1 nvidia-driver nvidia-cuda-toolkit
Enabling OpenCL for Intel
If your CPU supports OpenCL, then install the following packages:
sudo apt install firmware-misc-nonfree intel-opencl-icd
On Arch Linux, BlackArch
Enabling OpenCL for NVIDIA
Remove xf86-video-nouveau there it is:
sudo pacman -R xf86-video-nouveau
Install proprietary NVIDIA driver, CUDA and other required packages:
sudo pacman -S nvidia nvidia-utils opencl-nvidia opencl-headers cuda
Enabling OpenCL for Intel
sudo pacman -S linux-firmware intel-compute-runtime pocl
Friends, I need your help – if you have a different distribution kit or AMD video card, write in the comments how you installed the video driver – I will add this information here.
How to compile John the Ripper on Linux from source code
As already mentioned, it is important to build John the Ripper yourself so that it uses all the features of your processor. Another advantage of this approach is that we get the most recent version of John the Ripper.
Installing the required dependencies in Kali Linux:
sudo apt install build-essential libssl-dev yasm libgmp-dev libpcap-dev libnss3-dev libkrb5-dev pkg-config
Installing required dependencies on Arch Linux, BlackArch:
sudo pacman -S openssl yasm gmp libpcap nss krb5 pkg-config
The following is the same in any distribution:
wget https://github.com/openwall/john/archive/bleeding-jumbo.zip unzip bleeding-jumbo.zip rm bleeding-jumbo.zip cd john-bleeding-jumbo/src/ ./configure && make
Please note that in the last command you can use the -j option after which specify the number of (logical) cores of your processor, for example, I have 12 logical cores, then I use:
./configure && make -j12
Now go to the run folder:
cd ../run
And run the test:
./john --test
You don't need to install John the Ripper at the system level – move the run folder to a location convenient to you and run John from there. In addition to the John the Ripper executable, the run folder contains many scripts for extracting hashes – we will talk about them later.
Remember that if you type in the terminal
john
then the version preinstalled on the system will run, not the one you compiled.
Installing John the Ripper on Debian, Linux Mint, Ubuntu
The installation should be performed exactly the same as in Kali Linux. So refer to the Installing John the Ripper on Kali Linux section. If something did not work out for you, then write here in the comments indicating your distribution kit and error.
How to install John the Ripper on Windows
We'll look at compiling John the Ripper from source on Windows sometime later. Let's use the official binary file.
Install Cygwin first – just go to the official website https://www.cygwin.com/, download the setup-x86_64.exe file and install. If something is not clear about Cygwin, then all the details can be found in the article “How to get started with Linux commands on Windows: Cygwin”.
In Cygwin, you need to install the libOpenCL1 package, which is not available by default. The installation can be performed by running the setup-x86_64.exe file (which installed Cygwin) again, at the stage of selecting packages in the “Search” field, enter “libOpenCL1”, in the “View” drop-down list, switch to “Not Installed”, double-click the word “Skip”.
This will show the version of the package to install, click Next and complete the package installation.
You might like another way better: move the setup-x86_64.exe installation file to the C:\cygwin64\ folder and then open a Windows Terminal (PowerShell) and just run the command:
C:\cygwin64\setup-x86_64.exe -q -P libOpenCL1
See also: How to install packages (programs) in Cygwin
Download the winX64_1_JtR.7z file from https://github.com/openwall/john-packages/releases/tag/jumbo-dev.
Unzip the contents of this archive into the C:\cygwin64\home\<USERNAME> folder, for example, my username is MiAl, so I unpack it to C:\cygwin64\home\MiAl\. Please note that you need to create a folder and copy files into it on behalf of a regular user, because during its work John the Ripper will try to write data to a .pot file in the same folder where the program is running. If you copied the JtR folder in the file manager with elevated rights, then this folder will belong to the Administrator and it is impossible to write anything into it or change the rights to it.
It is actually possible to run John the Ripper on Windows even without Cygwin, but in this case it will not be able to use OpenCL (video cores) for brute-force.
Now in the folder C:\cygwin64\home\<USERNAME>\JtR\run\ find cygOpenCL-1.dll file and rename it to cygOpenCL-1.dll.bac.
Then in the c:\Windows\System32 folder find the OpenCL.dll file and copy it to the C:\cygwin64\home\<USERNAME>\JtR\run\ folder.
Then, in the C:\cygwin64\home\<USERNAME>\JtR\run\ folder, rename the OpenCL.dll file to cygOpenCL-1.dll.
Then the same procedure must be repeated for the file in the C:\cygwin64\bin\ folder. That is, in the C:\cygwin64\bin\ folder, find cygOpenCL-1.dll and rename it to cygOpenCL-1.dll.bac. Then find the OpenCL.dll file in the c:\Windows\System32 folder and copy it to the C:\cygwin64\bin\ folder. Finally, in the C:\cygwin64\bin\ folder, rename the OpenCL.dll file to cygOpenCL-1.dll.
So that you understand why we are doing all this, take a look at the cracking speed on the central processor:
And on the speed of hacking on the video card, which became available thanks to the actions shown above with the substitution of files:
The file swap trick may not work for all systems – but either way, you can use the CPU or integrated graphics to hack.
Open Cygwin console to execute commands.
Run test:
~/JtR/run/john --test=0
Run your system benchmark:
~/JtR/run/john --test
Still, JtR is one of those programs that primarily targets Linux. Further you will see that we will run scripts to generate (extract) hashes from files and, for example, some of the auxiliary programs/scripts need, for example, an installed Python environment, which is present in Linux by default.
John the Ripper check
In this section, we will check what devices John the Ripper sees for use during brute force.
The options are the same on any system, but remember that on Windows, to run John the Ripper, you need to open Cygwin and specify ~/JtR/run/john as the executable file.
If you run a file installed from the standard repositories in Linux, then it is enough to write simply
john
If you run a file compiled from the source code, then go to the directory with the executable file (in the program folder this is the run directory) and specify as the executable file
./john --list=opencl-devices
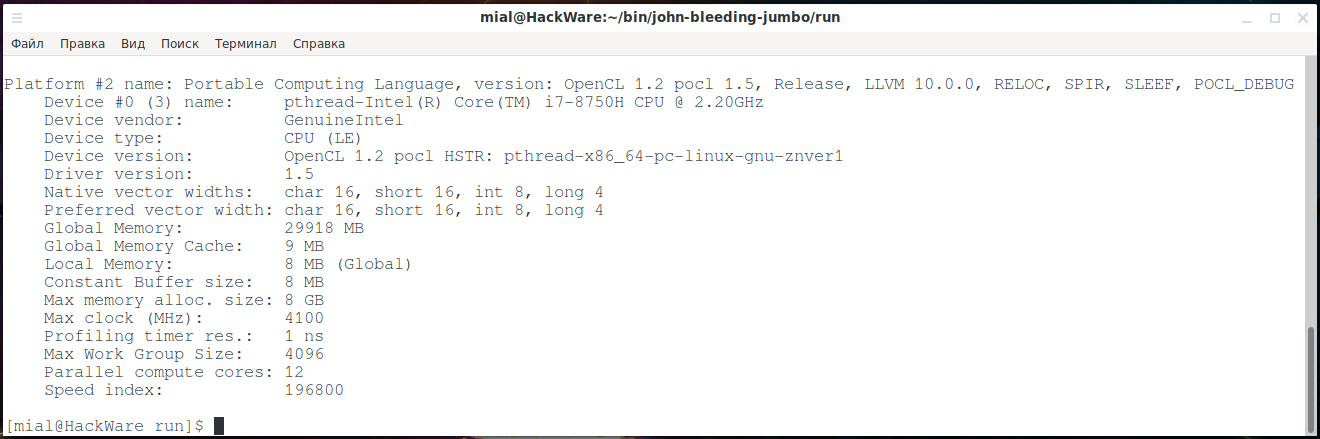
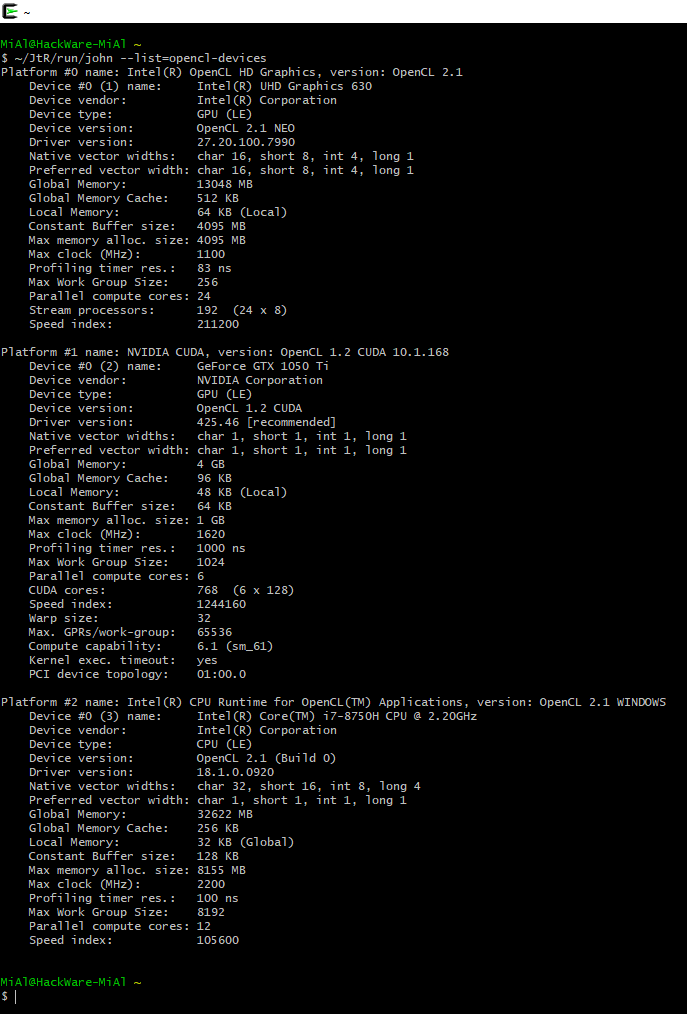
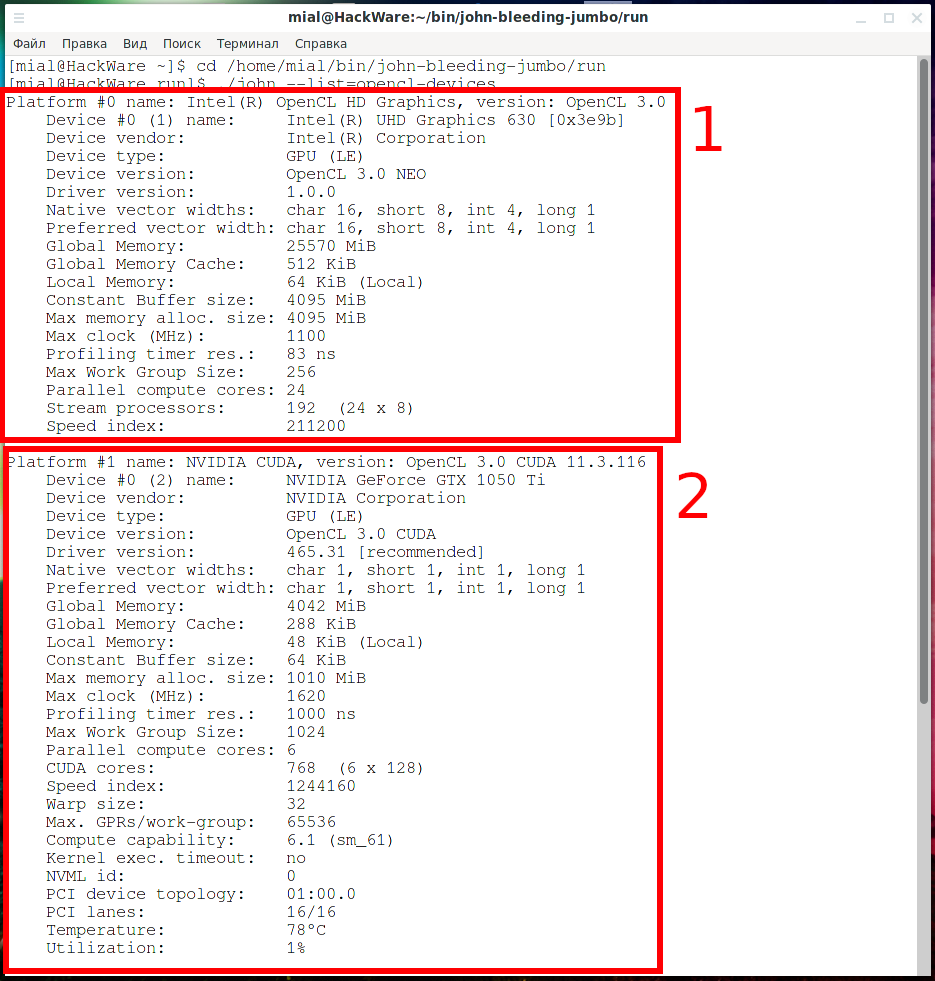
As you can see, I have three devices:
1 – video core of the central processor:
Platform #0 name: Intel(R) OpenCL HD Graphics, version: OpenCL 2.1
Device #0 (1) name: Intel(R) Gen9 HD Graphics NEO
Device vendor: Intel(R) Corporation
Device type: GPU (LE)
Device version: OpenCL 2.1 NEO
2 – discrete video card
Platform #1 name: NVIDIA CUDA, version: OpenCL 1.2 CUDA 11.0.228
Device #0 (2) name: GeForce GTX 1050 Ti
Device vendor: NVIDIA Corporation
Device type: GPU (LE)
Device version: OpenCL 1.2 CUDA
Driver version: 450.66 [recommended]
3 – CPU
Platform #2 name: Portable Computing Language, version: OpenCL 1.2 pocl 1.5, Release, LLVM 10.0.0, RELOC, SPIR, SLEEF, POCL_DEBUG
Device #0 (3) name: pthread-Intel(R) Core(TM) i7-8750H CPU @ 2.20GHz
Device vendor: GenuineIntel
Device type: CPU (LE)
Device version: OpenCL 1.2 pocl HSTR: pthread-x86_64-pc-linux-gnu-znver1
Driver version: 1.5
Likewise on Windows:
~/JtR/run/john --list=opencl-devices
As already mentioned, John the Ripper cannot just work with any supported algorithms using OpenCL – a module must be created for them. Therefore, some algorithms can only be cracked on a CPU, while some algorithms can be cracked on a GPU or on a CPU.
The list of algorithms may vary by OS and by installed dependencies.
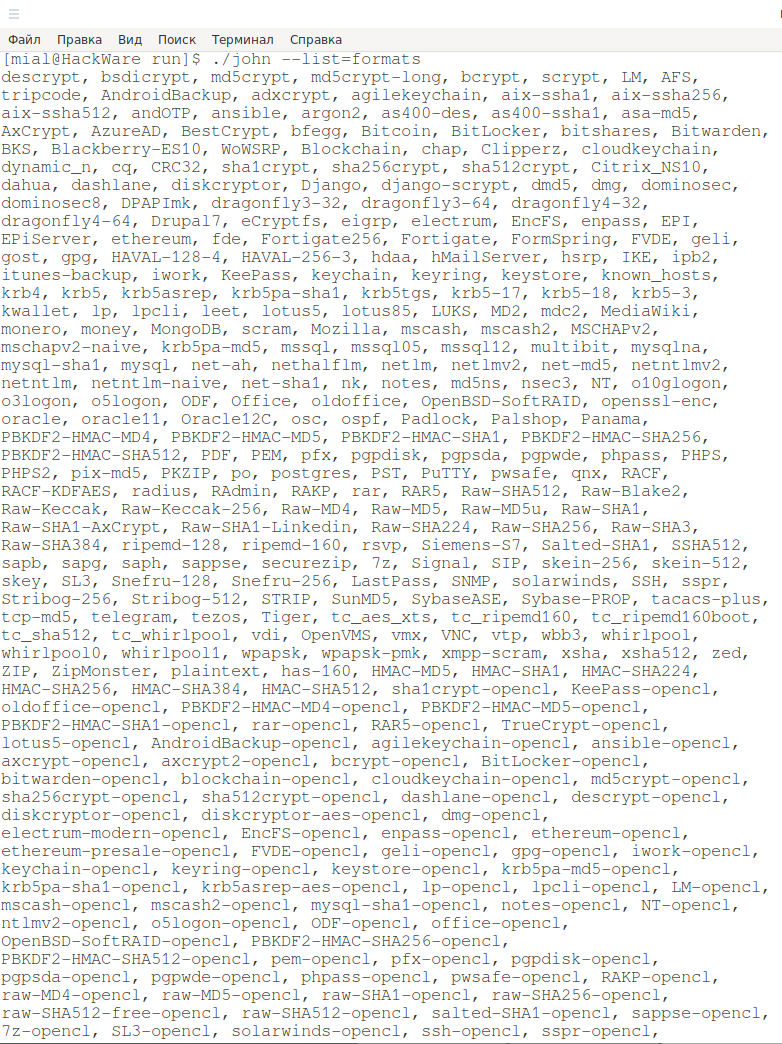
To see the list of supported algorithms:
./john --list=formats
The list is too big for one screen:
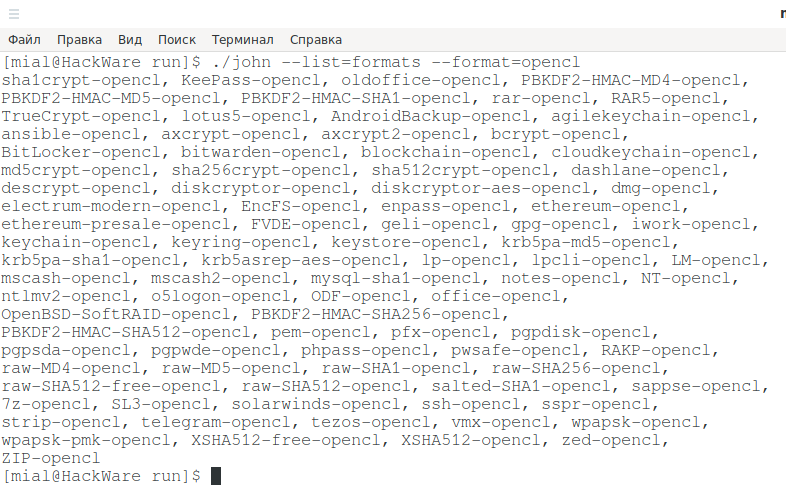
To see a list of algorithms for cracking on OpenCL:
./john --list=formats --format=opencl
Much smaller, but Wi-Fi is there.
How to use a graphics card to brute-force in John the Ripper
By default, JtR uses the CPU even if all the required OpenCL drivers are installed.
To enable the graphics card, you need to use the --format option and explicitly specify the algorithm that OpenCL supports.
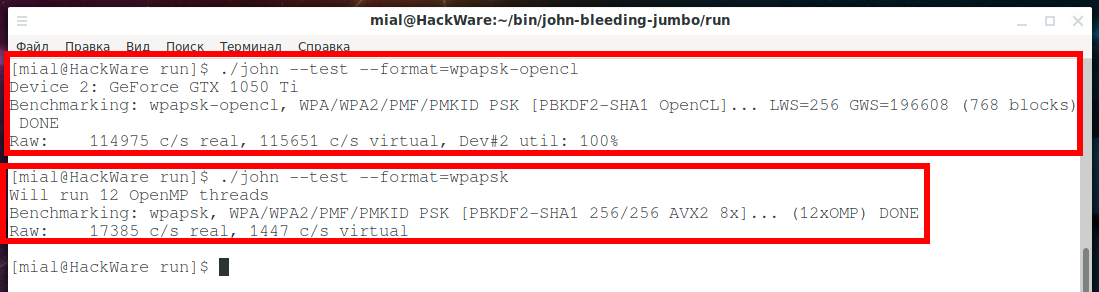
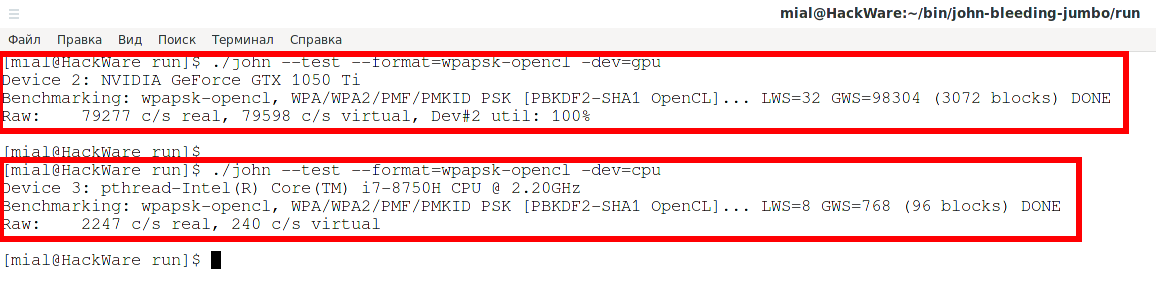
For example, to benchmark the wpapsk algorithm on a video card:
./john --test --format=wpapsk-opencl
To hack wpapsk on the central processor, you need to run something like this:
./john --test --format=wpapsk
As you can see in the screenshots: 114975/17385 = 6.61, that is, the speed of brute-forcing passwords has increased more than 6 times.
How to use a video CPU core in JtR
In this section, we will dwell in more detail on what devices JtR can use to perform computations and how exactly the program chooses between them when there is an alternative.
JtR can perform computation on:
- regular CPU cores
- OpenCL devices
The list of OpenCL devices may include:
- video card
- integrated CPU graphics
- regular CPU cores
As you can see, even without the OpenCL Runtime and video drivers installed, JtR is capable of cracking passwords.
Algorithms that do not have the “-opencl” string in their names, such as wpapsk, can only be brute forced on regular CPU cores.
Algorithms with the string “-opencl” in the name, for example wpapsk-opencl, can be brute forced on:
- video card
- integrated CPU graphics
- regular CPU cores
To see a list of available OpenCL devices, run the command:
./john --list=opencl-devices
Take a look at the following screenshots:
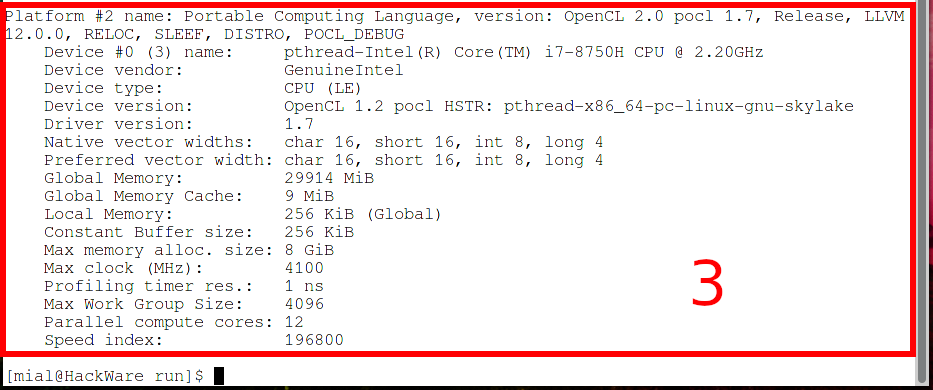
Number one is integrated graphics in the CPU.
Number two is the video card.
Number three are the regular CPU cores that JtR will handle as an OpenCL device.
By default (without a -dev option), JtR uses one OpenCL device that it thinks is likely the fastest.
Using the -dev option, you can select a specific OpenCL device, the device number is in parentheses, on lines starting with “Device #0”, for example:
Device #0 (1) name: Intel(R) UHD Graphics 630 [0x3e9b]
Device #0 (2) name: NVIDIA GeForce GTX 1050 Ti
Device #0 (3) name: pthread-Intel(R) Core(TM) i7-8750H CPU @ 2.20GHz
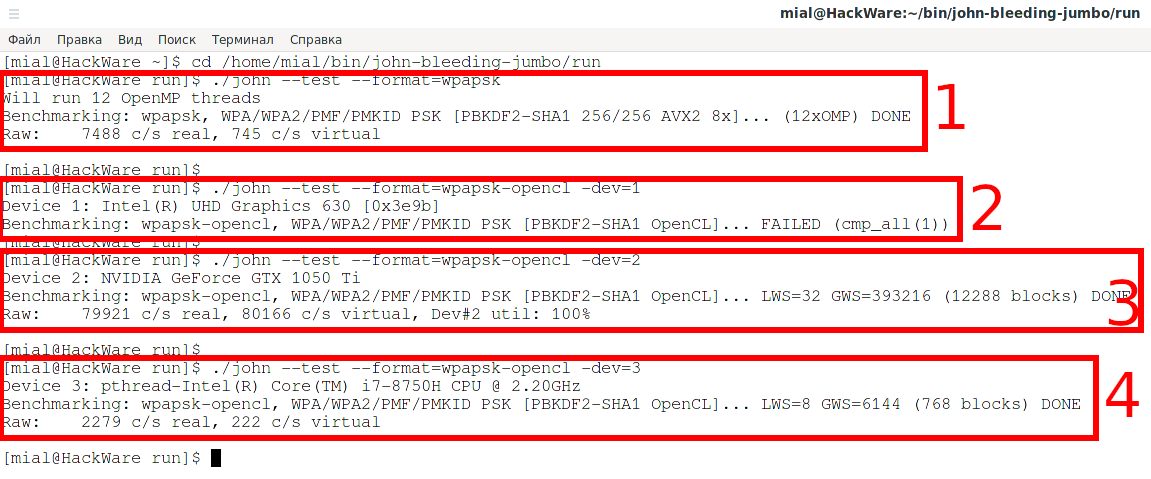
So, to run JtR on regular CPU cores, use the algorithm name without the “-opencl” string:
./john --test --format=wpapsk
To start cracking the password on the first OpenCL device (in my case it is integrated CPU graphics, test failed):
./john --test --format=wpapsk-opencl -dev=1
To start cracking the password on a second OpenCL device in my case it is a discrete graphics card):
./john --test --format=wpapsk-opencl -dev=2
To start cracking a password on a third OpenCL device (in my case it is regular cores of the central processor):
./john --test --format=wpapsk-opencl -dev=3
You can also use the -dev option like this:
- -dev=gpu
- -dev=cpu
These tell JtR, when it uses OpenCL, to use only GPU device(s) or only CPU device(s).
./john --test --format=wpapsk-opencl -dev=gpu ./john --test --format=wpapsk-opencl -dev=cpu
How to run John the Ripper benchmark
To check the speed of brute-force passwords in JtR, use the --test option.
./john --test
This option can be used with a number – the number of seconds that the test will run.
./john --test=10
If you want to check the speed of only a certain algorithm, then use the --format option.
An example of a test of the speed of cracking a Wi-Fi password by a central processor:
./john --test=10 --format=wpapsk
An example of a test of the speed of cracking a Wi-Fi password with a discrete video card:
./john --test=10 --format=wpapsk-opencl
If you only need to check the operation of cracking of various algorithms without running a benchmark, then specify 0 as the value of the --test option:
./john --test=0
How to set up John the Ripper
John the Ripper has a settings file with a lot of options. This file is called john.conf and is located in the same folder as the john executable.
Provide good cooling; watch the temperature. If the OpenCL runtime supports this, the GPU temperature will be monitored and displayed in the status bars, and there is a user-configurable limit in john.conf that will shutdown at 95 ° C.
This setting is set by the directive:
AbortTemperature = 95
The temperature is indicated in degrees Celsius - °C.
Instead of interrupting, you can stop the program for this number of seconds to cool down the GPU when the temperature reaches the AbortTemperature value, then the program will re-check the temperature and either continue or pause. Set to 0 to just quit.
If SleepOnTemperature = 1 (one second) is specified, then no pause/resume messages will be displayed, since such a short value is interpreted as a desire to keep the temperature of the video card near the extreme value. Default directive value:
SleepOnTemperature = 1
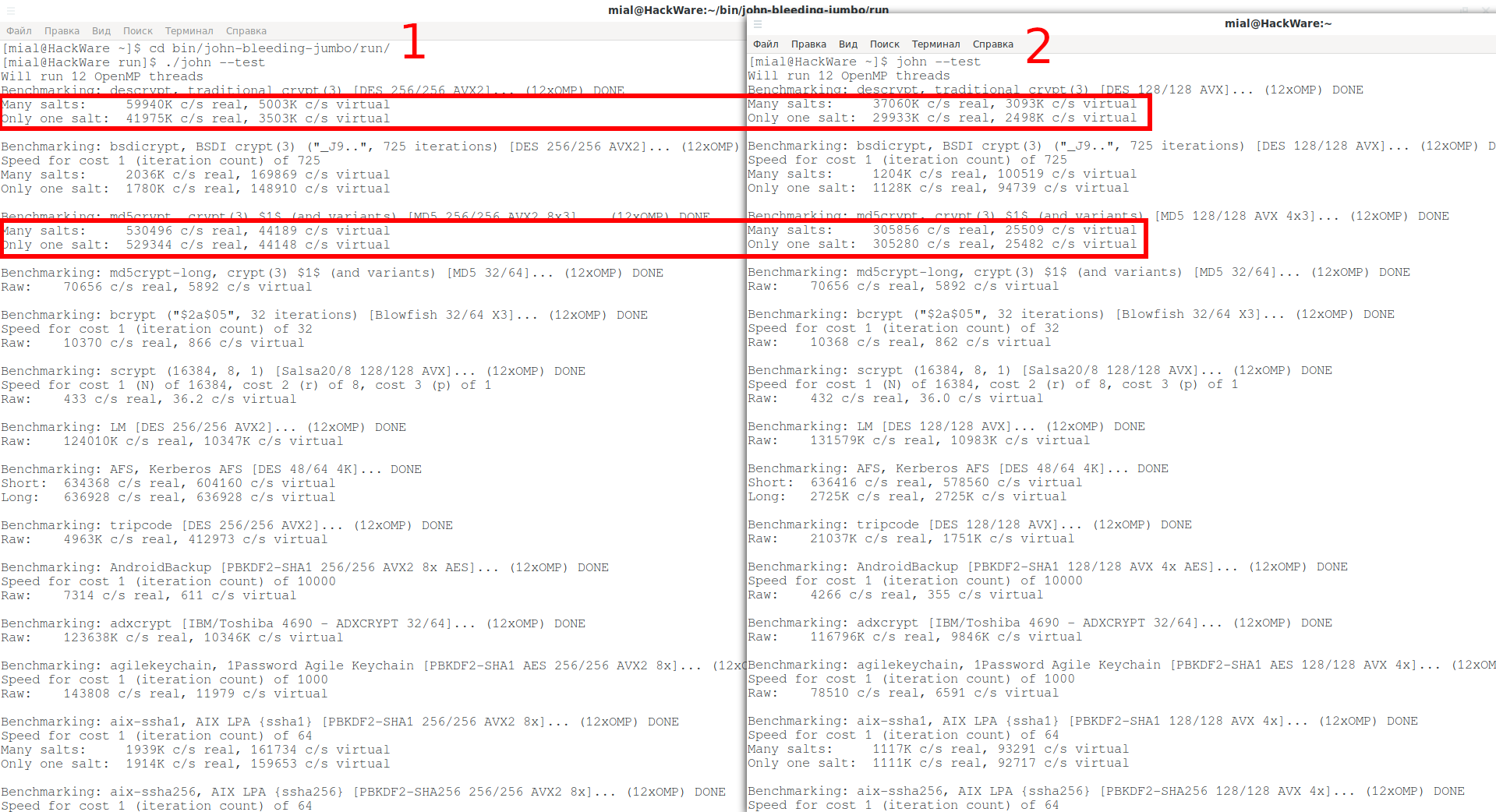
Compilation difference with AVX2 and AVX for John the Ripper
To view build parameters use the --list=build-info option:
./john --list=build-info
Benchmark of two versions of programs:
1. This half of the screenshot is a benchmark for the latest version of JtR that I compiled from source. Since my CPU supports AVX2, John the Ripper supports that as well.
2. And I installed this one from the standard repository of my distribution – it is compiled with AVX.
The difference is significant.
Result for the first part
So, this is the first part on John the Ripper – a popular offline brute force. In it, we learned the tricks for installing JtR, and also learned how to test the speed of brute-forcing passwords, turn on the video card for use and control actions when overheating.
When running such programs (John the Ripper and Hashcat), you need to take care of proper cooling. If your computer/laptop overheats, then the brute-force speed will drop very significantly.
The next parts will be even more interesting! We'll learn how to extract password hashes and launch dictionary and mask attacks, and much more!
Related articles:
- How to Install Drivers for Hashcat on Windows (94.6%)
- Comprehensive Guide to John the Ripper. Part 2: Utilities for extracting hashes (58.6%)
- Comprehensive Guide to John the Ripper. Part 3: How to start cracking passwords in John the Ripper (how to specify masks, dictionaries, hashes, formats, modes) (58.6%)
- How to use precomputed tables to crack Wi-Fi passwords in Hashcat and John the Ripper (58.6%)
- Comprehensive Guide to John the Ripper. Part 4: Practical examples of John the Ripper usage (58.6%)
- What is HNAP, how to find and exploit routers with HNAP (RANDOM - 3.1%)







On January 29, via PayPal, transferred to the site support, my name is David.
It's clearly the best tuto I've found about JTR. Tus, going deeper in this website, I've added it within my favourites and I have made a donation.
Alexey, vsio hochin horocho!:)
Hi David! Thank you for your kind words and for your donation. I added it to the list of donors: https://kali.tools/?page_id=1312
Privet Alex!
I have a quyestion please.
To crack a 8 characters -all ascii- from a hash list , I would use:
john.exe hashes.txt --mask=’?a’ --min-length=8 --max-length=8 --format=raw-MD5-opencl
But how could I force JTR to use at least 1 Upper character, 1 lower, 1 special and 1 decimal character within the password generated?
Spacibo bolchoi.
David
Hi, David!
Well… in short, I don’t have a ready-made solution how to use a mask with rules like this, but I've thought about this a lot, so I can suggest several ways to achieve something like this.
The most realistic method I described in the article “How to generate candidate passwords that match password strength policies (filtering words with grep)”.
Its summary:
1. The maskprocessor program generates all possible password candidates
2. Using the grep command, only those that match the required criteria are filtered
3. Filtered passwords are passed to standard input of JtR/hashcat to crack the hash
Instead of a maskprocessor + grep combination you can use pydictor: “How to generate dictionaries by any parameters with pydictor”.
Another method is theoretical rather than practical. A rule-based attack can force the JtR to use at least 1 upper character, 1 lower character, 1 special character, and 1 decimal character in the generated password. But the problem is that the Rule-based attack only works with a dictionary. Yes, again we can generate all possible password variations and use Rule-based attack, but the dictionary will be too enormous. All the details (and examples) can be found in the following article:
Hi Alex ,
I have installed this software(gui version) to my computer on windows 10. Buy i could not run successfully cause i dont know what i will select to browse button for John the Ripper Executable path.
Thanks for support..
Regards.
Hello! If you don’t plan to use the GPU for brute-force, then download the winX64_1_JtR.7z file from https://github.com/openwall/john-packages/releases/tag/jumbo-dev, unzip it to any folder.
For example, I unzipped it to the root of C: drive, then the path to the executable is C:\JtR\run\john.exe. But you will be able to use for brute-force only CPU.
If you want to use GPU as well, then please wait for the next part, it will be devoted to Johnny with detailed instructions. I'm already working on it.
Hello, again! Using some tricky methods it is possible to force Johnny/John perform computing on a video card.
Everything in the part 7: Johnny – GUI for John the Ripper
Updated instructions for installing on Windows in the latest version of Cygwin, now brute-force on the GPU works again.
Hello
I have a situation which buffles me:
I am using WPA openCL with "-dev=1,2,3,4 --fork=4" (GPUs asignements from john --list )
GPUs are working corectly with the dynamic load mode. What puzzles me if the that ALL 4 CPU cores are used to 99.8% solid.
Any ides ?
Thank you
Hello!! I read your comment 10 times and thought about it for 2 days, but I still didn't understand it, sorry.
I am resending the last one since something strange happend with the test (it dissapeared)
Command options:
REC4
12
--devices=1,2,3,4
--fork=4
--format=wpapsk-opencl
--1=?l?d
--mask=?1?1?1?1?1?1?1?1?1?1
--min-length=8
/root/work/JohnTheRipper/chrisg03.john
--session=chris-A
--progress-every=2
--input-encoding=UTF-8
--internal-codepage=UTF-8
------------------------------
cpu: {'total': 99.6, 'user': 85.5, 'system': 14.1, 'idle': 0.4, 'nice': 0.0, 'iowait': 0.0, 'irq': 0.0, 'softirq': 0.0, 'steal': 0.0, 'guest': 0.0, 'guest_nice': 0.0, 'ctx_switches': 21841, 'interrupts': 12797, 'soft_interrupts': 4652, 'syscalls': 0, 'time_since_update': 3.0022010803222656, 'cpucore': 4}
-------------------------------
GPU load - 7th column is each GPU iv %
20210802 11:25:56 0 110 54 - 100 3 0 0 4513 1569
20210802 11:25:56 1 113 55 - 100 3 0 0 3802 1569
20210802 11:25:56 2 153 54 - 100 4 0 0 5005 1417
20210802 11:25:56 3 63 54 - 100 3 0 0 5005 1582
Why a such high load on CPU?
Thanks
Hello!
The CPU is an OpenCL device as well. Thus, using the --devices=1,2,3,4 option you select all OpenCL devices, including the CPU, to work with JtR.
You can check your OpenCL device numbers with the command:
Let's take a look at my system:
#1 – GPU core of CPU
#2 – dedicated GPU (NVIDIA)
#3 – CPU cores
So if I run JtR with --devices=1,2,3 option, it will use the CPU and GPU (actually it fails to use the GPU core of the CPU, but never mind). So if I want to use the dedicated GPU only, I should use the --devices=2 option (or rather I shouldn’t use any options at all since the dedicated GPU will be selected by default).
Hi!
I use Kali 2021.4 with John the Ripper "1.9.0-Jumbo-1+git20211102-0kali1" and it doesn't recognize the informed option. Can you help me?
Do you have any idea how i can resolve the issue below: ?
I have upgraded kali linux using: sudo apt update && sudo apt full-upgrade -y and install the driver for NVIDIA: sudo apt install -y ocl-icd-libopencl1 nvidia-driver nvidia-cuda-toolkit
john --list=opencl-devices
Section [opencl-devices] not found.
help[:WHAT], subformats, inc-modes, rules, externals, ext-modes, ext-hybrids,
ext-filters, ext-filters-only, build-info, encodings, formats, format-classes,
format-details, format-all-details, format-methods[:WHICH], format-tests,
sections, parameters:SECTION, list-data:SECTION, <conf section name>
Hello,
It seems that your posts on Hashcat and John are amongs the best in terms of details and structure, keep up the good work! In regard to this article, i have noticed that John is able to support blockchain-opencl and i was wondering if that means John tool can crack bitcoin wallet.dat passwords. I am aware that Hashcat can do that, but i have a technical constraint and i am interested in using John for that particular purpose. Thank you!!
Best regards.