Best Kali Linux tools in WSL (Windows Subsystem for Linux) (Part 2)
This is the second collection of Kali Linux tools that work great in WSL (Windows Subsystem for Linux), yet are simple enough to be used by any Windows user, regardless of their Linux skills.
Of course, it is recommended to start with the “Best Kali Linux tools in WSL (Windows Subsystem for Linux) (Part 2)”, and also read the articles on working in WSL, links to which are just given in this first part.
In this article, we will not dwell on how to run Kali Linux in WSL and how to open a graphical desktop environment – all this is in the previous part.
Viewing and clearing metadata
Meta information is such an important issue that it was worth covering it already in the first part, but it turned out to be already extensive.
Start by installing the mat2 program:
sudo apt install mat2
To view the metadata of any file, run a command like (with the -s option):
mat2 -s /PATH/TO/FILE
To clear metadata in files, run a command like:
mat2 /PATH/TO/FILE
As we remember from the section “How to open a Windows file in Linux”, to access the file system, you need to use mounted disks located along the /mnt/ path, for example, the C:/ drive is mounted in the /mnt/c directory.
For example, I want to view the metadata of the 20191110_080512.jpg file located in the C:\Users\MiAl\Documents\testing\foto\ folder. Then the path from Kali Linux to WSL to it will be as follows: /mnt/c/Users/MiAl/Documents/testing/foto/20191110_080512.jpg
We substitute this path into the command given above:
mat2 -s /mnt/c/Users/MiAl/Documents/testing/foto/20191110_080512.jpg
And here it is – metadata!
Pay particular attention to the GPS coordinates – they show the exact location at the time of the photo:
GPSLatitude: 12 deg 35' 20.00" N GPSLatitudeRef: North GPSLongitude: 99 deg 57' 2.00" E GPSLongitudeRef: East GPSPosition: 12 deg 35' 20.00" N, 99 deg 57' 2.00" E
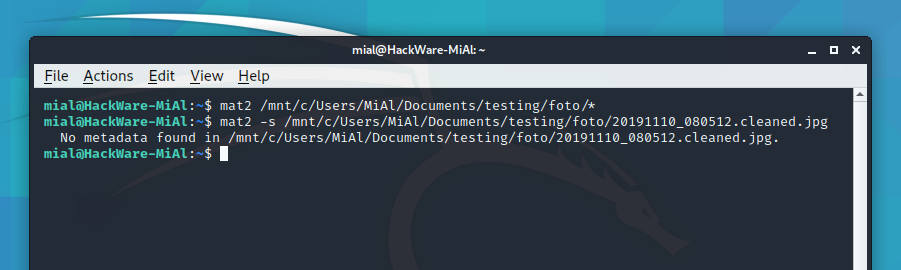
If you want to see the property of all photos in a folder, then instead of the file name specify the * (asterisk) symbol:
mat2 -s /mnt/c/Users/MiAl/Documents/testing/foto/*
If you want to clear the metadata of a specific file, then specify the path to it and its name:
mat2 /mnt/c/Users/MiAl/Documents/testing/foto/20191110_080512.jpg
If you want to clear the metadata of all files in a folder, use * (an asterisk) instead of the file name:
mat2 /mnt/c/Users/MiAl/Documents/testing/foto/*
The old files will remain unchanged, but new files will be created with the string “.cleaned” in the name and completely cleared metadata.
You can see for yourself that there is no more metadata:
mat2 -s /mnt/c/Users/MiAl/Documents/testing/foto/20191110_080512.cleaned.jpg
Pay attention to the “No metadata found” string.
How to generate dictionaries
If you need a list of passwords generated according to a certain pattern, then the Maskprocessor program will help you.
Install this program:
sudo apt remove maskprocessor git clone https://github.com/hashcat/maskprocessor cd maskprocessor/src/ make sudo mv ./mp64.bin /usr/bin/maskprocessor
The use is very simple, the main thing is to remember the conventions of symbol groups:
- ?l – all small Latin letters
- ?u – all uppercase Latin letters
- ?d – all digits
- ?s – special characters, namely: !"#$%&'()*+,-./:;<=>?@[\]^_`{|}~
- ?a – means all the above characters combined
Let's say you need to make a four-digit list of passwords, then the command is as follows:
maskprocessor ?d?d?d?d
A password in which a small letter, then a capital letter, then a number, and then all this is repeated:
maskprocessor ?l?u?d?l?u?d
A password that starts with mial followed by six digits:
maskprocessor mial?d?d?d?d?d?d
I think you got the essence of using this program.
To save the created dictionary to a file, use the “ > FILE-NAME” construction, for example:
maskprocessor mial?d?d?d?d?d?d > mial-pass.txt
How to find the hostname by IP
With the command lie this:
dig -x IP-ADDRESS +short
you can find out the hostname.
For instance:
dig -x 87.250.250.242 +short ya.ru.
One more example:
dig -x 157.245.118.66 +short w-e-b.site.
This method does not always work.
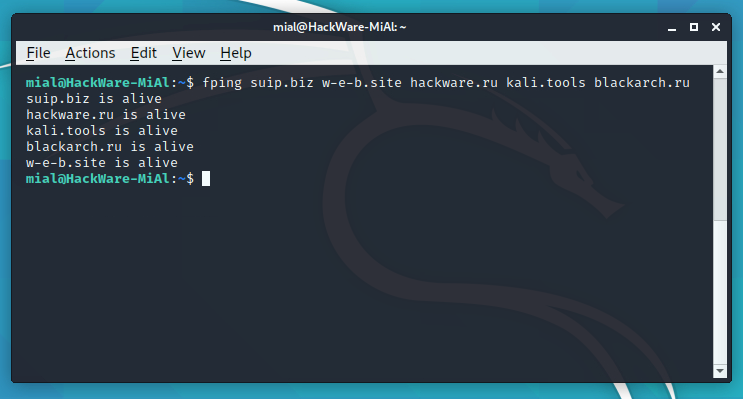
Checking the availability of multiple hosts
If you want to check if a group of sites is currently online, you can use the fping command.
Installing fping:
sudo apt install fping
The usage is very simple – specify all sites separated by a space:
fping suip.biz w-e-b.site hackware.ru kali.tools blackarch.ru
With the -f option, you can specify a file with a list of hosts:
fping -f hosts.txt
Remeber, the file format is as follows: one host per line.
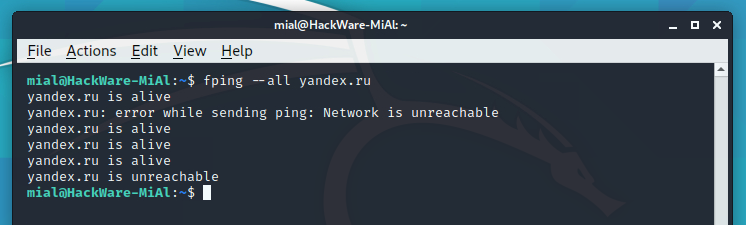
Large sites can have more than one IP address. As a rule, now these are one or more IPv4 addresses and several IPv6 addresses. To check the availability of all of them, use the --all option:
fping --all yandex.ru
For some IPs, you can see an error
is unreachable
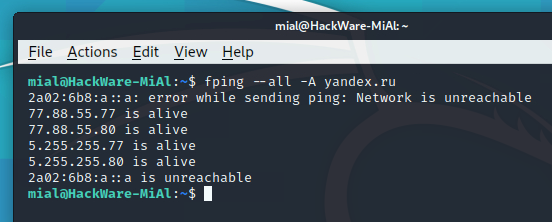
We use the -A option to show the IP addresses:
fping --all -A yandex.ru
That is, IPv6 addresses are not available because my ISP does not support them.
Option -4 and -6 can be specified to ping only IPv4 or only IPv6 addresses:
fping --all -A -4 yandex.ru
Very fast scanning of large networks
In the previous part, we have already covered Nmap, the program for scanning open ports. It is a very powerful program, but when scanning really large networks, it is quite slow.
Another open port scanner, Masscan, will help solve the speed problem.
Install Masscan:
sudo apt install masscan
An example of starting a scan of ports 80.8000-8100 on the 10.0.0.0/8 network at a speed of 10 thousand packets per second:
sudo masscan -p80,8000-8100 10.0.0.0/8 --rate=10000
In fact, 10,000 packets per second is quite a lot. If you lost your Internet connection after running the previous command, then decrease the value of the --rate option.
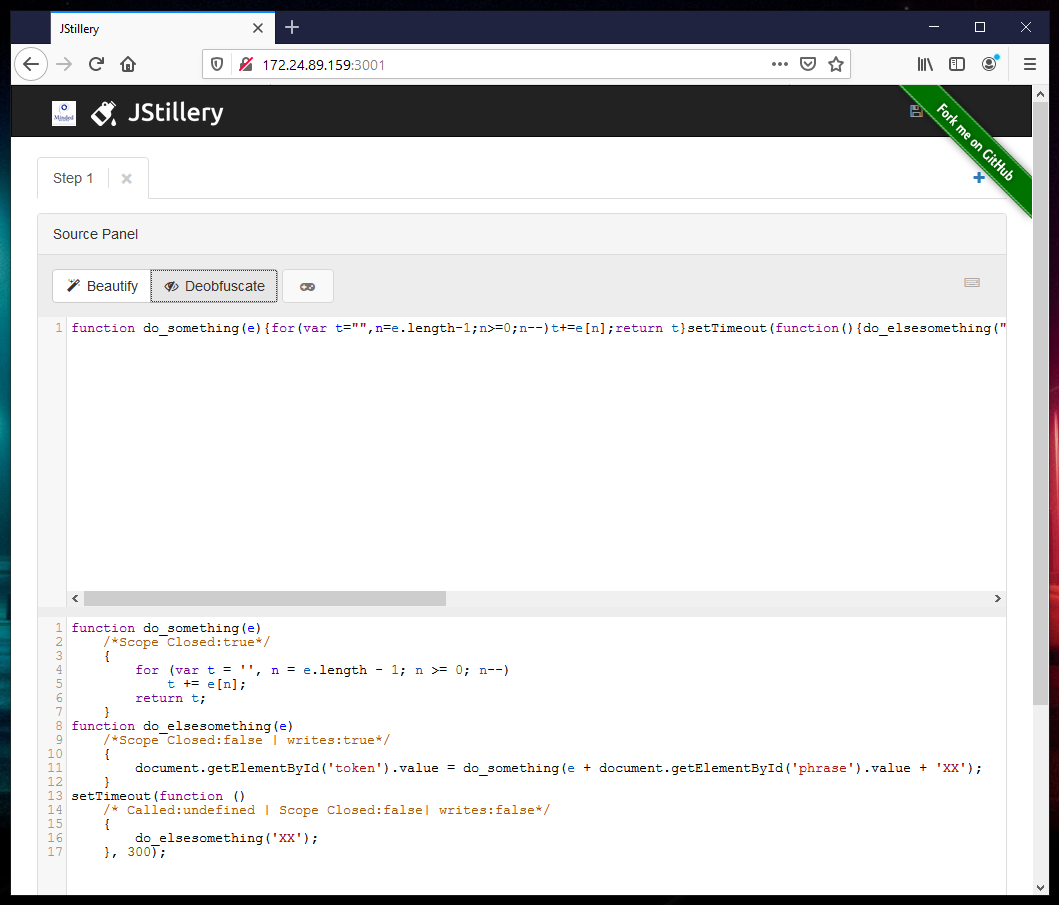
Deobfuscating JavaScript code
If you want to make JavaScript code readable, then JStillery is used for this.
Install Jstillery:
sudo apt install npm git clone https://github.com/mindedsecurity/JStillery cd JStillery sudo npm install
Usage is very simple, just specify the path to the file for deobfuscation:
./jstillery_cli.js /path/to/file
To compile the server (if you need not only a command line tool, but also want to use a web interface):
npm run build_server
To start the server:
npm run start_server
After that, the web interface will be available at http://localhost:3001. If you have not installed a graphical interface in Kali Linux, that is, you cannot open a web browser in it, then you can still access the JStillery web interface.
To do this, look at the IP address of your Kali Linux:
ip a
For example, I have it 172.24.89.159, then the web interface will be accessible from Windows at http://172.24.89.159:3001.
The second part turned out to be no less rich and varied than the first. In the third part, we will focus on website information gathering and finding hidden resources (subdomains, hidden files, administration panels, real IP addresses).
Related articles:
- Anonymous scanning through Tor with Nmap, sqlmap or WPScan (50%)
- How to obfuscate JavaScript code (50%)
- How to view metadata in MS Word files. How to remove and edit Word metadata (47.4%)
- How to extract, delete and edit metadata in LibreOffice files (47.4%)
- Best Kali Linux tools in WSL (Windows Subsystem for Linux) (Part 1) (35%)
- Hacking WPA/WPA2 passwords with Aircrack-ng: dictionary attack, cooperation with Hashcat, maskprocessor, statsprocessor, John the Ripper, Crunch, hacking in Windows (RANDOM - 2.8%)