How to set up Tor hidden service in Debian (Kali Linux, Linux Mint, Ubuntu)
What is Tor Hidden Service and How to Do It
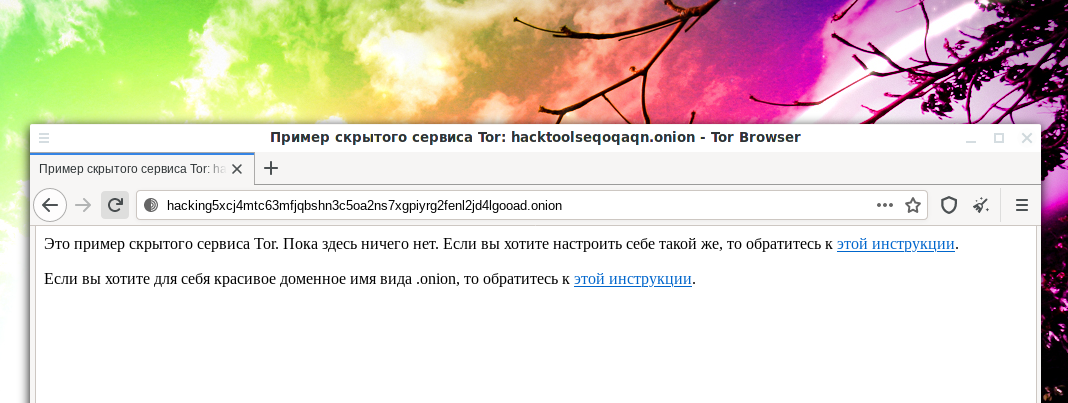
If you are already using hidden TOR services, then make sure you have the address and keys of the third version. That is, earlier the addresses were something like this:
- hacktoolseqoqaqn.onion
And now they have become something like this:
- hacking5xcj4mtc63mfjqbshn3c5oa2ns7xgpiyrg2fenl2jd4lgooad.onion
TOR Onion version 2 hidden services will stop working in October 2021. For some time now, when automatically generating a domain for a hidden service, TOR Onion v3 vanity has been used. But if you are still using the old, second version, then you need to go to the third one with the new address, and use the old address to inform your visitors.
This tutorial on how to configure the hidden Tor service will show you how to configure it in Kali Linux, but it will work for all Debian derivatives, including Linux Mint and Ubuntu. If you run Windows, then for you the instruction “How to install Tor and create Tor hidden service on Windows”.
Tor hidden services have domain names with .onion extensions
Hidden services are only accessible from the Tor network. For example, you can open these addresses if you are using the Tor Browser. The hidden service does not need a white IP, since traffic is routed inside the Tor network and it is fully responsible for data exchange.
Domain name like .onion is issued for free and automatically. It is generated as a random set of characters and you cannot select it. However, the article “How to get a custom domain name for Tor hidden service” explains how this can be circumvented to some extent.
As already mentioned, a white IP is not needed, the only requirement is that the computer must be turned on and must be connected to the Tor network. Also requires a web server. On the server, you can use any technology, including Apache, PHP, database management systems, etc. - everything that you can install on your computer or your server. To install a web server, see the articles:
- The basics of working with a web server for a pentester
- How to install web server on Windows 10 (Apache 2.4, PHP 8, MySQL 8.0 and phpMyAdmin)
It is assumed that you have read the article following the link and you already have a web server installed and you have started it:
sudo systemctl start apache2 sudo systemctl start mysql
Configuring the virtual host of the Tor hidden service
You need to start by setting up a virtual host. It is necessary to make this virtual host available only on the local network. Because if it is available globally, it is very easy to lose your “stealth”.
Open the Apache config file:
sudo gedit /etc/apache2/ports.conf
There I have a line
Listen 80
That is, Apache listens for incoming connections both locally and from outside. That is, if someone wants to connect to your web server, then if he is on your local network or you have a white IP, he can do it. If you don't need this, then replace the line with the following:
Listen 127.0.0.1:80
The web server will only listen on port 80 on the local IP 127.0.0.1.
Now I create a virtual host configuration file for the hidden service:
sudo gedit /etc/apache2/sites-available/hidden.conf
Insert the following into it:
<VirtualHost 127.0.0.1:80> DocumentRoot "/var/www/html/onion" ServerName localhost ServerAdmin you@example.com <Directory /> Options +Indexes +FollowSymLinks +ExecCGI AllowOverride All Order deny,allow Allow from all Require all granted </Directory> </VirtualHost>
Basically, you just need to edit the DocumentRoot "/var/www/html/onion" in it - it shows the path to your website, which will be a hidden Tor service.
Don't forget to create this directory:
sudo mkdir /var/www/html/onion
Activate the virtual host:
sudo a2ensite hidden
Place any of your files in this folder and restart the web server:
sudo systemctl restart apache2
Check the status:
sudo systemctl status apache2
Place some files in the /var/www/html/onion folder and check the server is working:
curl 127.0.0.1
If everything works, then continue.
Connecting a local web server to the Tor network as a Tor hidden service
We need to start by installing Tor:
sudo apt install apache2 tor
Open the file
sudo gedit /etc/tor/torrc
Find the lines there:
#HiddenServiceDir /var/lib/tor/hidden_service/ #HiddenServicePort 80 127.0.0.1:80
The first line specifies where the generated domain name and secret key will be stored. It is enough to simply uncomment it to get:
HiddenServiceDir /var/lib/tor/hidden_service/
The second line also needs to be uncommented. The first number is the port where your hidden service will be hosted - it is better not to change it so that the user does not have to manually specify a non-standard port. The next line is the local address of your virtual host on the web server. The IP should remain the same, and the port, if necessary, change to the one that you assigned to the virtual host of the web server. In my case, it is also 80:
HiddenServicePort 80 127.0.0.1:80
Start (or restart, if installed before) the Tor service:
sudo systemctl restart tor
Check its status:
systemctl status tor
Add the service to startup (optional):
sudo systemctl enable tor
To find out your domain name, type:
sudo cat /var/lib/tor/hidden_service/hostname
Now tell this domain name to the clients of your Tor hidden service. These sites can only be accessed through the Tor network. They are not available on the regular Internet.
If you need several hidden Tor services, then create the required number of virtual hosts for the web server and use the lines
HiddenServiceDir /var/lib/tor/other_hidden_service/ HiddenServicePort 80 127.0.0.1:80 HiddenServicePort 22 127.0.0.1:22
as many times as you need. For each service, you need to specify its own directory where the domain name and private key are located.
My Tor hidden service: hacking5xcj4mtc63mfjqbshn3c5oa2ns7xgpiyrg2fenl2jd4lgooad.onion
Remember to restart the service whenever you change Tor settings:
sudo systemctl restart tor
Related articles:
- How to install Tor and create Tor hidden service on Windows (97.8%)
- How to get a custom domain name for Tor hidden service (94.2%)
- Anonymous scanning through Tor with Nmap, sqlmap or WPScan (56.3%)
- Free easy way to hide IP in Linux (56.3%)
- How to install and run Tor Browser on Kali Linux (56.3%)
- How to Install and run WPScan on Windows (RANDOM - 2.3%)