Port scanner for Windows
If you need to scan ports of computers and devices on a local network or on the Internet from Windows, then one of the best options is a combination of Nmap and Zenmap (a graphical interface for Nmap).
Nmap has a large number of scanning options, and Zenmap's graphical interface makes the program extremely easy to use.
Nmap features include:
- port scanning
- determining the operating system of the remote host
- identification of services, software and their versions on a remote host
Using Nmap scripts, you can check remote hosts for vulnerabilities, weak passwords, collect certain information, look for services that allow anonymous login, and perform other tasks related to the actions of a network administrator or penetration tester.
To download a port scan program, go to the Nmap download page: https://nmap.org/download.html. Find the link to the .exe file there. You can see all the files available for download here: https://nmap.org/dist/
Run the downloaded Nmap installer, in addition to the main program, it will also install several components that are necessary for Nmap to work on Windows.
When everything is ready, a program shortcut will appear on your desktop:
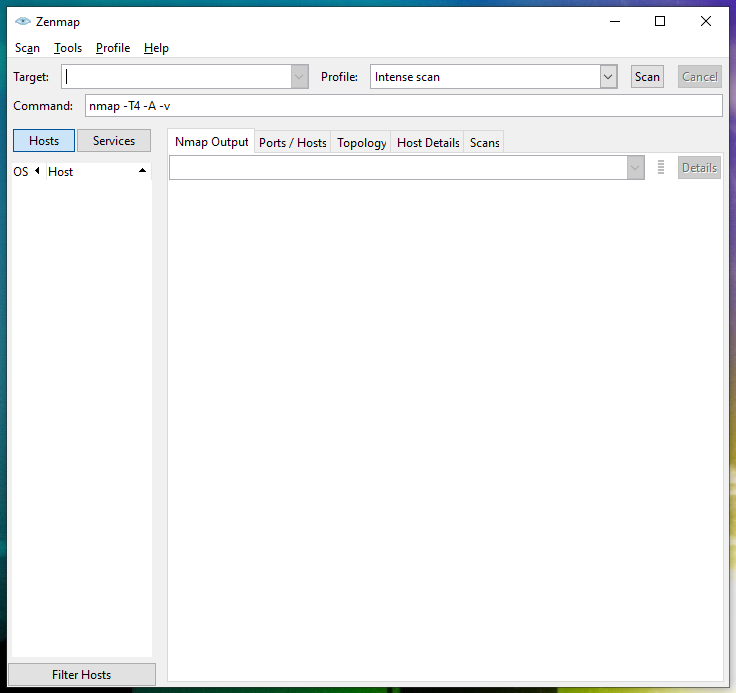
The main program window looks like this:
In the Target field, you need to specify the site address (URL), IP or range of IP addresses for scanning.
In the Profile field, select the desired profile from the drop-down list.
How to Specify Target in Zenmap (Nmap)
Site addresses should be specified without a protocol, for example:
- mi-al.ru
- suip.biz
It would be incorrect to indicate the form https://mi-al.ru, that is, URL.
IP addresses can be specified one by one, for example, 192.168.0.1; using CIDR notation like 192.168.0.1/24; as well as specifying ranges in one or more octets, for example, 192.168.0.1-100, or 192.160-170.50-100.1
What Zenmap Profiles mean
The profiles in the Zenmap main window are a collection of options for typical scans. Let's take a look at all Zenmap profiles.
- Intense scan
An intense, comprehensive scan. The -A option enables OS detection (-O), version detection (-sV), script scanning (-sC), and traceroute (--traceroute). Without root privileges only version detection and script scanning are run. This is considered an intrusive scan.
- Intense scan plus UDP
Does OS detection (-O), version detection (-sV), script scanning (-sC), and traceroute (--traceroute) in addition to scanning TCP and UDP ports.
- Intense scan, all TCP ports
Scans all TCP ports, then does OS detection (-O), version detection (-sV), script scanning (-sC), and traceroute (--traceroute).
- Intense scan, no ping
Does an intense scan without checking to see if targets are up first. This can be useful when a target seems to ignore the usual host discovery probes.
- Ping scan
This scan only finds which targets are up and does not port scan them.
- Quick scan
This scan is faster than a normal scan because it uses the aggressive timing template and scans fewer ports.
- Quick scan plus
A quick scan plus OS and version detection.
- Quick traceroute
Traces the paths to targets without doing a full port scan on them.
- Regular scan
A basic port scan with no extra options.
- Slow comprehensive scan
This is a comprehensive, slow scan. Every TCP and UDP port is scanned. OS detection (-O), version detection (-sV), script scanning (-sC), and traceroute (--traceroute) are all enabled. Many probes are sent for host discovery. This is a highly intrusive scan.
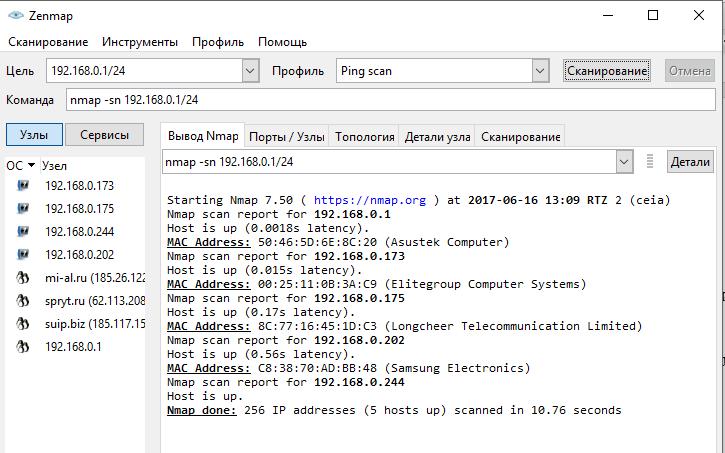
For example, if I want to know which hosts on the subnet are pinged, then I select the Ping scan profile.
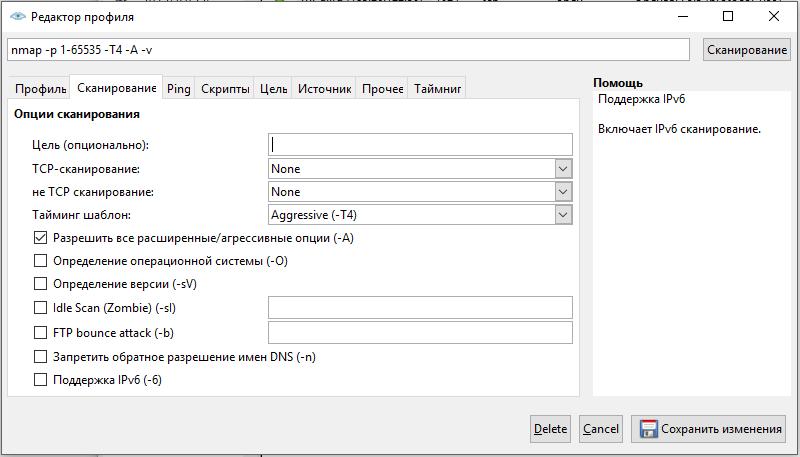
With a handy profile editor, you can edit and create new profiles.
Although the use of the profile editor contains a description of the actions to be performed and, therefore, does not require knowledge of Nmap options, for a deeper understanding of the program you can see the description of all Nmap options at https://en.kali.tools/?p=1433
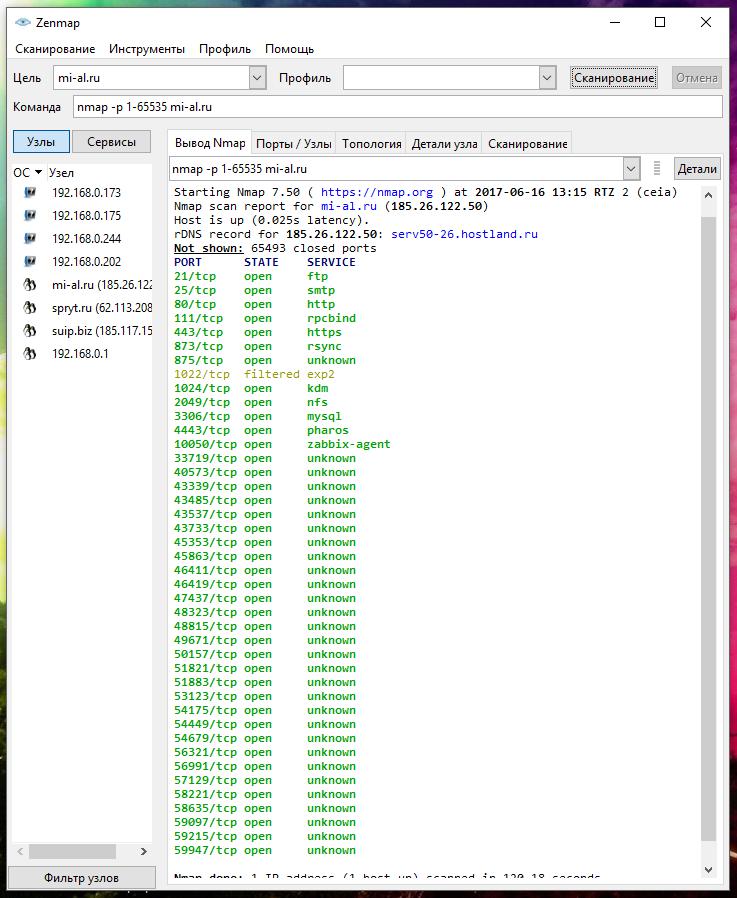
If you want to scan all TCP ports, then specify the target and enter “nmap -p 1-65535” as a command
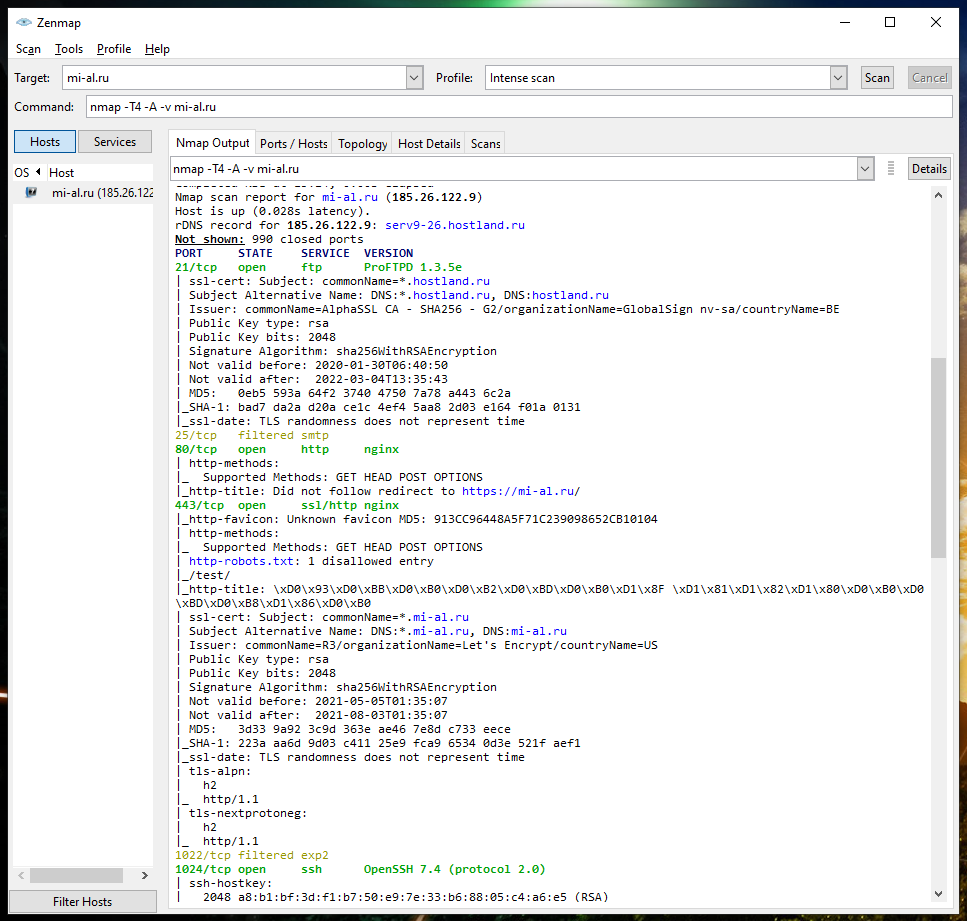
Scan results
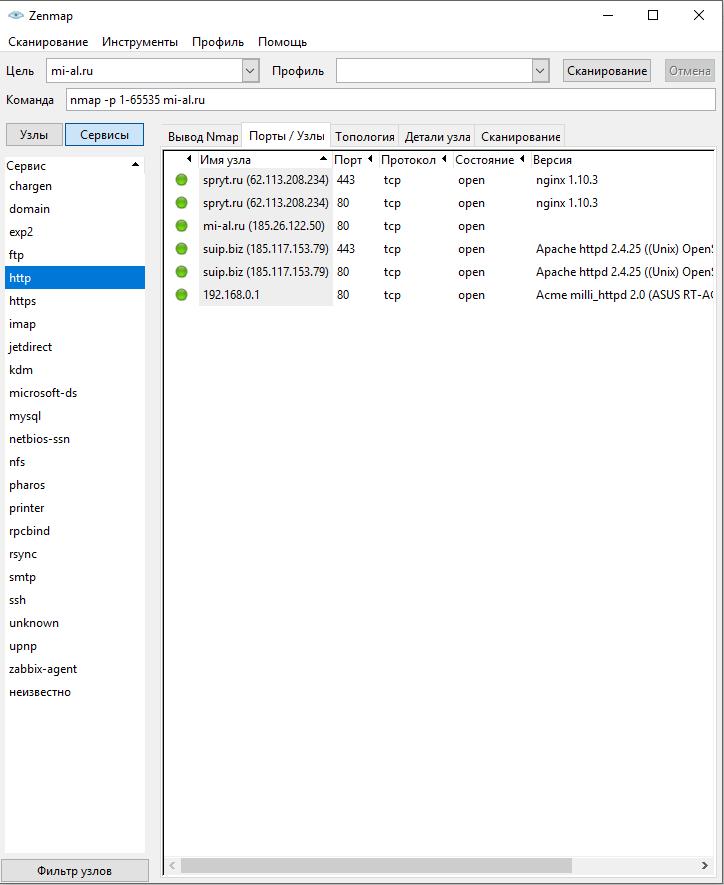
The results from the last scan are visible in the Nmap Output tab. On the left side, you can switch between Sites and Services. When you click on a specific node, you will see the previous scan results. When you click on a service, you will see the host on which the service was found:
To view summary information on a host, click on it and select the Host Details tab:
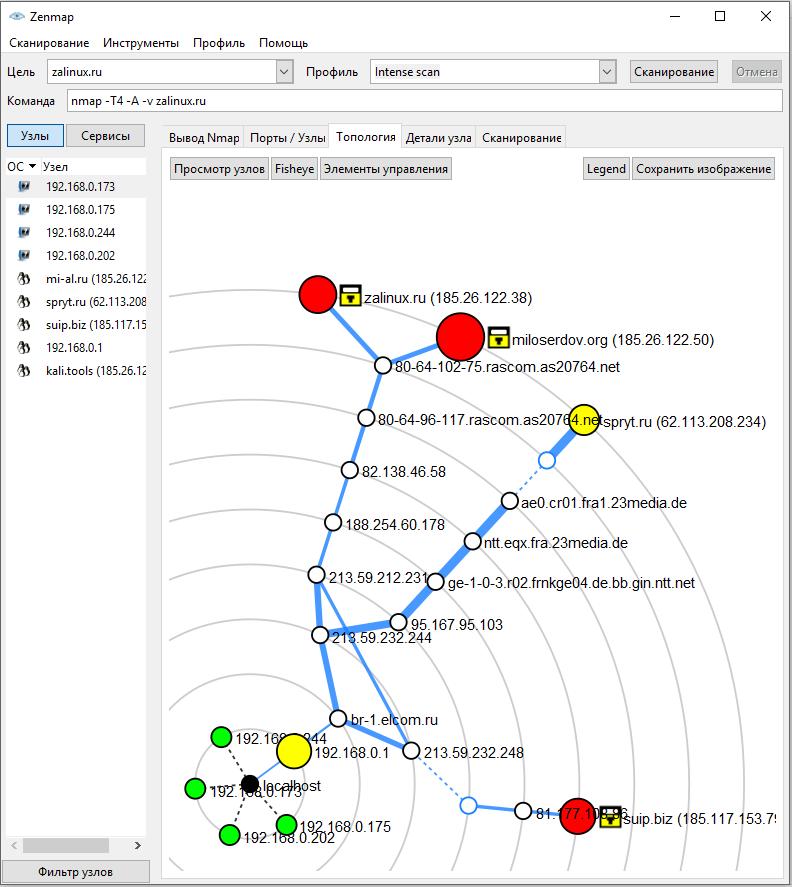
In the Topology tab, you will see information about the links between the scanned/discovered hosts:
How to change the Zenmap interface language
Zenmap interface has been translated into many languages. If there is a translation for the language of your OS, then the program will automatically show the interface in your language.
At the same time, Zenmap lacks options for switching the interface language, therefore, for example, if you do not like the translation, you cannot select another language in the settings, for example, English.
The easiest method to make inscriptions in Zenmap in English is to delete the language folder, for example, to disable Russian localization, you need to delete the C:\Program Files (x86)\Nmap\share\zenmap\locale\ru\ folder.
A slightly more complex method for those who like to tinker with the terminal, it is about setting a new environment variable. The official instructions suggest doing this at the system-wide level, but this is not necessary.
Open PowerShell (Win+x → Windows PowerShell) and enter two commands:
$Env:LANG='C' Start-Process "C:\Program Files (x86)\Nmap\zenmap.exe"
In order not to remember the commands every time, create a Zenmap-en.ps1 file on your desktop and copy into it:
$Env:LANG='C' Start-Process "C:\Program Files (x86)\Nmap\zenmap.exe"
Save and close.
To run, right-click and select Run with PowerShell.
And finally, if you want to change a variable at the system-wide level (as shown in the official instructions), then the name of the variable must be “LANG”, and its value (for English) must be “C”. If there are other applications in the system that respect the value of the LANG variable, this will affect them as well.
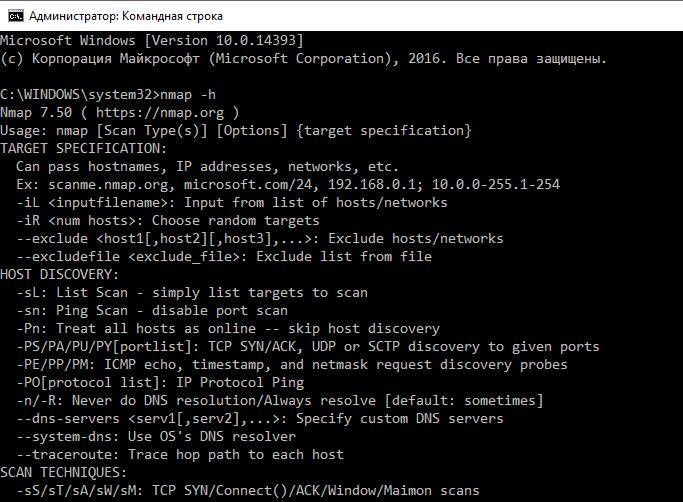
Using Nmap on Windows from the command line
If you need a console version of Nmap, you can use it on Windows just like you do on Linux. When Nmap is installed, it adds the path to the Nmap executable to the environment variables, so you just need to specify the program name on the command line:
nmap -h
If you did not use the installer, but downloaded the zip archive, then it lacks a graphical interface. You also need to install Npcap and Microsoft Visual C++ 2013 Redistributable Package yourself.
Conclusion
Nmap allows Windows to scan computers and other devices for open ports. It is also able to determine the services running on the remote host, their version.
The graphical interface allows you to simplify the use of the program, but it is recommended that you familiarize yourself with all the program options to gain skills in various scanning techniques.
In addition to their main functions – scanning ports and determining the versions of installed software – Nmap scripts allow you to perform various other tasks, including checking for vulnerabilities, weak passwords, and collecting information.
Related articles:
- Nmap usage tips (88.8%)
- Utilities for information gathering, OSINT and network analysis in Windows and Linux (86%)
- GUI Port Scanner for Windows and Linux (Angry IP Scanner) (85.2%)
- Tracerouting tools and methods (75.3%)
- sshprank: SSH mass-scanner, login cracker and banner grabber (68.6%)
- Hacking websites training in Windows (RANDOM - 1.3%)