Hash-generation software
Tools to hash strings
In Linux, there are programs for calculating and validating popular hashes:
- b2sum – в compute and check BLAKE2 (512-bit) message digest
- cksum – checksum and count the bytes in a file
- md5sum – compute and check MD5 (128-bit) message digest
- sha1sum – compute and check SHA1 (160-bit) message digest
- sha224sum – compute and check SHA224 (224-bit) message digest
- sha256sum – compute and check SHA256 (256-bit) message digest
- sha384sum – compute and check SHA384 (384-bit) message digest
- sha512sum – compute and check SHA512 (512-bit) message digest
All these programs are installed by default in most Linux distributions; they allow you to calculate hashes for files or for strings.
The usage of all these programs is similar – you must specify a file name, or pass a string to the standard input.
If you use echo to calculate a hash of a string, it is extremely important to specify the -n option, which prevents the addition of a newline character - otherwise, every hash for strings will be wrong!
An example of calculating a SHA1 hash for the 'test' string:
echo -n 'test' | sha1sum a94a8fe5ccb19ba61c4c0873d391e987982fbbd3 -
Another way to pass a string without adding a newline:
printf '%s' 'test' | md5sum
As you can see, after the hash there is a space and file name (in the case of standard input - a dash is specified) to show only the hash, you can add | awk '{print $1}' or | cut -d" " -f1:
echo -n 'test' | sha1sum | awk '{print $1}'
The same result can be obtained by the following construction:
echo -n 'test' | sha1sum | cut -d" " -f1
Multi hash computing programs
In addition to the listed utilities built into Linux, there are other programs that can calculate various checksums (hashes). Often, they support several hashing algorithms at once; they can have additional input and output options (they support different formats and encodings), some of them are prepared for the audit of the file system (detection of unauthorized changes in files).
List of some popular programs for computing various hashes:
omnihash
A tiny little tool to hash strings, files, input streams and network resources using various common hashing algorithms.
To install omnihash in Kali Linux:
sudo pip install omnihash[sha3,pyblake2]
omnihash Usage:
omnihash [OPTIONS] [HASHMES]...
If there is a file at hashme, read and omnihash that file. Elif hashme is a string, omnihash that.
omnihash options:
-s Hash input as string, even if there is a file with that name.
-v Show version and quit.
-c Calculate CRCs as well.
-f TEXT Select one or more family of algorithms: include only algos having
TEXT (ci) in their names.
-m TEXT Match input string.
-j Output result in JSON format.
--help Show this message and exit.
omnihash usage examples:
Hash stings:
omnihash "correct horse battery staple" Hashing string 'correct horse battery staple'.. DSA: abf7aad6438836dbe526aa231abde2d0eef74d42 DSA-SHA: abf7aad6438836dbe526aa231abde2d0eef74d42 MD4: 131adffe1d8712c1b624ba62b5bcf3fd MD5: 9cc2ae8a1ba7a93da39b46fc1019c481 MDC2: b41edfd5e9cb278433a4a5c740898ffb RIPEMD160: 5e708aa85ae8b0d080837c50bd63634d584edc00 SHA: 99add446c4eed3772a92fabe3ab2c56fc2c9a26e SHA1: abf7aad6438836dbe526aa231abde2d0eef74d42 SHA224: 636f080709f287ec5c5ea79442fc4bb914924cd5c6ca8ff84e3410c4 SHA256: c4bbcb1fbec99d65bf59d85c8cb62ee2db963f0fe106f483d9afa73bd4e39a8a SHA384: c24b92449c871f33bbbf1fc1989e5e1037cfa9a3dfdb17947f8172226181e7825ebb4c750763915835bf125a590e05ae SHA512: be5ef7679d88ab9a9045f6267e55f5e5784b4b8cd764b5cd855a5244f91c626953cd46c43d7668873fd6efbd3b221249315580031963472a078781fe046e62ae dsaEncryption: abf7aad6438836dbe526aa231abde2d0eef74d42 dsaWithSHA: abf7aad6438836dbe526aa231abde2d0eef74d42 ecdsa-with-SHA1: abf7aad6438836dbe526aa231abde2d0eef74d42 whirlpool: 8c0e81ff1650da90c70a859319ba923b8807ad26af0940f8562fd62e75878eed13f434ba47860223ac55d92d91a169b3f9a1cbd4f10f3fca1b877088e5675891 SHA3_224: 5ee454bfad2d1e25ba74884af244379d17bf50ef46dbe644e7587fc8 SHA3_256: af9ac3dac56b02f1ea017e7657a9bb7e1778274e31509f134f023e41a5953866 SHA3_384: 5a1caac1441d4d002d6650f558b6bb10593095fe4664496b8f1665f239d923e69f95cbd141c5dcf833770542ff2322e8 SHA3_512: 4b65d7b7acc886f9add07db3a5d42bf0032fe0109a1fd56f623c7093e8a59689f9246918a4f388034ddf393231eaba0742b3dc1840e4556270a729ce56098f35 BLAKE2s: 239dd0a7e138f5fced884939c200b9ed35e092c17cd27f6049a5d0bda9fd7b8b BLAKE2b: 84793833af5cf79ef9548fd505dbb6633e54c1b4ec2c4f577c3a0ae41764e50ce8278ab8f6e0edd3e90ab6ef0914ff0e49329e0703ecc2fb7fdac12a4823fea7
Hash files:
omnihash /etc/hosts Hashing file '/etc/hosts'.. DSA: 0ec93cf2b8000b5b339d0c5435251ad14f85b553 DSA-SHA: 0ec93cf2b8000b5b339d0c5435251ad14f85b553 MD4: 226fb465616a070fd027f8a5db118561 MD5: 8efb3881814e54b95b030ff37012e22a MDC2: 8df8bca5c8dbfc87e9c399aad2c326ac RIPEMD160: f98ef6e7b10b8c4d7e0d129136f42f66163b8767 SHA: 2c8e7f4dade830ae6a4fdc6d20fd4a93b43bbbae SHA1: 0ec93cf2b8000b5b339d0c5435251ad14f85b553 SHA224: 43f81c9b4e15a835a0857ceba586239932210c718e8861b8235e4dff SHA256: 04f186e74288a10e09dfbf8a88d64a1f33c0e698aaa6b75cdb0ac3aba87d5644 SHA384: f7592a8db187f42957834132d964be00266a38b2b1bf5511bb7e636ae13822a4f858b386c11a77f680e34c49ca9cd8c1 SHA512: df9896fc36a18cd04c1a133c3a79a4783456a301b4380e9b30ebe56012708c373456681d6066ad7608f26cbcc147bd171cf57f1f9a6e977bf16295945e32047b dsaEncryption: 0ec93cf2b8000b5b339d0c5435251ad14f85b553 dsaWithSHA: 0ec93cf2b8000b5b339d0c5435251ad14f85b553 ecdsa-with-SHA1: 0ec93cf2b8000b5b339d0c5435251ad14f85b553 whirlpool: 69f0d48f1e134a09dc6172953527c344465d759d02d0a3a932d6b97a57d2e0ca1fba324180a013e84a7e7cd912de1fb6e50deb15d05a56c27f8ec53d58c768c2 SHA3_224: 2a8d5b60d3d6003c25516d110ebd53284d3c669a61e03a81cc756a26 SHA3_256: e40fa76654213ce8fb8e449f5659294fd3f3bb2fa461ff8678e7ea99d94cec1e SHA3_384: 9e8df099fd06ca136ff87c63b17cdd284eaa03558515c35053db41b116bb91419710b948e908e74edddc74ca9cd3b76f SHA3_512: 8158c2f4a2aab1e0abe63ec83711fe3343531f6683c89e5ff539cf8d29eb7bce931443646cd2704a9f1b901436741cc28d230bc58c5e98ed42b676fc15bfa354 BLAKE2s: e84408c7fac52f8436c4f3ba5e4e2abd038e4735a343de471f7c1dc548cd6ddf BLAKE2b: 2c23f27128614351712d3e2851c9c24763499512117ceb55b3f277863880767a11272ec5abe5527a9ae08cdea367264aa31b9160da148c00f732806200076954
Hash URLs:
omnihash https://cryptome.org Hashing content of URL 'https://cryptome.org'.. DSA: f63c8212d4769f2740306d30df6e56e4d773c412 DSA-SHA: f63c8212d4769f2740306d30df6e56e4d773c412 MD4: 2a61fd067f31bc161545e7e6eb08e31f MD5: 12d4aca3c58007350edae822301d7d83 MDC2: fe7acaffad747aa9ab644bd37314b916 RIPEMD160: 1e7b92befcd56f70b90f7a6b5d6b3e8b8c56a3f9 SHA: 124876e226334bfadaf71c00e60f2e77551b140a SHA1: f63c8212d4769f2740306d30df6e56e4d773c412 SHA224: 5af71e96da3d3383ddff0fa308bd7714f91af5873f17f7fa944aa5c0 SHA256: c320ec6af2dc3c1129e238e3d06653cbe6f01d5c791763db4b9dcabe169debc6 SHA384: 0cf01cf20737f91c9736c924ab4cd2c503bfbb055ed630b5fa80d94b598e26a2376c739c4d195e464e2259c0cb4f6313 SHA512: c978e3544a6d4b11ed180463e6916ac562d3c90c007a107205e2f61118e2f3d032caf2053bd4ee0ab5c4a287279d0294dec4663ab2e3ed90e3e7312c2ae69abc dsaEncryption: f63c8212d4769f2740306d30df6e56e4d773c412 dsaWithSHA: f63c8212d4769f2740306d30df6e56e4d773c412 ecdsa-with-SHA1: f63c8212d4769f2740306d30df6e56e4d773c412 whirlpool: c12d0362a5c30aa8848db7e6fd3f13d8bd5094201a89389c0ab24793dbee6733834d03362f6a960816abd450a900c016797996ac46e50af38bb02681054f30e7 SHA3_224: 7bdb6efdc640a25a30dbbf51cc7f22e17f6c1963d871f89506292b35 SHA3_256: 31cb08dadd163c309e7a551e7a8104ea5f935c1933c0e9a4005ee26809958766 SHA3_384: c2257da2c3352c4165acbd3ada334eb0034c0ee514da8609823eb537bd089d8ddde2ef63eead0867208f8c5d10f866b3 SHA3_512: bd36ece65851c5238882d3861343c980f58888cc0057a6ac808e20ef28ce2e8970d1123c88360c13064f3dbd332a10369df6b4be9483a9b8860b9d2156dd3e65 BLAKE2s: f4b0dd61772776ba04a4f0c94975a92acc41eb61ac2745e60b3adb7a08dc88d4 BLAKE2b: c1635df205326331b565959edb4b3b64a81a352ec594c869d35a2373ee8f1b8288e9135c0627b6cc44d54378a4b1f1fb39e124065644b7b9a62f57dd0e16e8ab2c23f27128614351712d3e2851c9c24763499512117ceb55b3f277863880767a11272ec5abe5527a9ae08cdea367264aa31b9160da148c00f732806200076954
hashdeep
hashdeep — is a set of cross-platform tools to compute hashes, or message digests, for any number of files while optionally recursively digging through the directory structure. It can also take a list of known hashes and display the filenames of input files whose hashes either do or do not match any of the known hashes. This version supports MD5, SHA-1, SHA-256, Tiger, and Whirlpool hashes.
hashdeep is the new name that the program received after the support for all hashes was combined into one executable file. Earlier the program was called md5deep, to which, in the form of separate programs, were gradually added:
- sha1deep
- sha256deep
- sha3deep
- tigerdeep
- whirlpooldeep
In some operating systems, the md5deep program or even all of the above programs are installed with hashdeep.
How to install hashdeep in Kali Linux:
sudo apt install hashdeep
hashdeep usage:
hashdeep [OPTION]... [FILES]...
hashdeep options:
-c <alg1,[alg2]> - Compute hashes only. Defaults are MD5 and SHA-256
legal values: md5,sha1,sha256,tiger,whirlpool,
-p <size> - piecewise mode. Files are broken into blocks for hashing
-r - recursive mode. All subdirectories are traversed
-d - output in DFXML (Digital Forensics XML)
-k <file> - add a file of known hashes
-a - audit mode. Validates FILES against known hashes. Requires -k
-m - matching mode. Requires -k
-x - negative matching mode. Requires -k
-w - in -m mode, displays which known file was matched
-M and -X act like -m and -x, but display hashes of matching files
-e - compute estimated time remaining for each file
-s - silent mode. Suppress all error messages
-b - prints only the bare name of files; all path information is omitted
-l - print relative paths for filenames
-i/-I - only process files smaller than the given threshold
-o - only process certain types of files. See README/manpage
-v - verbose mode. Use again to be more verbose
-d - output in DFXML; -W FILE - write to FILE.
-j <num> - use num threads (default 1)
Hashdeep usage examples:
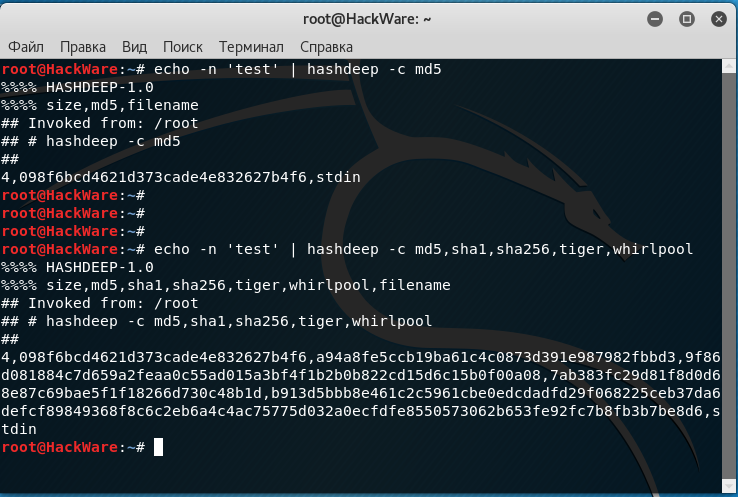
Calculate the md5 hash (-c md5) of the string ‘test’:
echo -n 'test' | hashdeep -c md5 %%%% HASHDEEP-1.0 %%%% size,md5,filename ## Invoked from: /home/mial ## $ hashdeep -c md5 ## 4,098f6bcd4621d373cade4e832627b4f6,stdin
Calculate all supported hashes (-c md5, sha1, sha256, tiger, whirlpool) of the string ‘test’:
echo -n 'test' | hashdeep -c md5,sha1,sha256,tiger,whirlpool %%%% HASHDEEP-1.0 %%%% size,md5,sha1,sha256,tiger,whirlpool,filename ## Invoked from: /root ## # hashdeep -c md5,sha1,sha256,tiger,whirlpool ## 4,098f6bcd4621d373cade4e832627b4f6,a94a8fe5ccb19ba61c4c0873d391e987982fbbd3,9f86d081884c7d659a2feaa0c55ad015a3bf4f1b2b0b822cd15d6c15b0f00a08,7ab383fc29d81f8d0d68e87c69bae5f1f18266d730c48b1d,b913d5bbb8e461c2c5961cbe0edcdadfd29f068225ceb37da6defcf89849368f8c6c2eb6a4c4ac75775d032a0ecfdfe8550573062b653fe92fc7b8fb3b7be8d6,stdin
Create a control file (/tmp/auditfile) filled with hashes of files in the directory (dir) for the audit with a recursive traversal (-r):
hashdeep -r dir > /tmp/auditfile
Perform an audit (-a) on the specified known hash file (-k /tmp/auditfile) recursively trversalling (-r) the specified directory (dir):
hashdeep -a -k /tmp/auditfile -r dir
Hasher
Hashes is a tool to quickly hash plaintext strings, or compare hashed values with a plaintext. The reason I wrote this is because when on an assessment, I don't, and won't, send hashes that I found to an online "hash generator" that I don't trust. I'd rather have an easy way to generate hash values, or compare hashes to plaintext values, quickly. Hashes does this.
How to install Hasher in Kali Linux:
sudo pip install hashes
Hasher usage:
hashes [-h] [--list] [-G] [-C] [--hash-type md5] [--plaintext password]
[--hash HASH] [--rounds 5000] [--salt SALT]
[--username USERNAME]
Hasher options:
-h, --help show this help message and exit --list List all supported hash algorithms -G Generate a hash from the provided string. -C Compare provided plaintext with a hash --hash-type md5 The hashing algorithm you want to use --plaintext password Plaintext string to hash --hash HASH Hash used for comparison --rounds 5000 Number of rounds to hash your plaintext string --salt SALT Salt used for hashing --username USERNAME Only required for select hash types
Hasher usage examples:
Generate a hash (-G) from the specified string (--plaintext 'test') using the MD5 hash algorithm (--hash-type md5):
hashes -G --plaintext 'test' --hash-type md5
hashrat
Hashrat is a hash-generation utility that supports the md5, sha1, sha256, sha512, whirlpool, jh-244, jh256, jh-384 and jh-512 hash functions, and also the HMAC versions of those functions. It can output in 'traditional' format (same as md5sum and shasum and the like), or it's own format. Hashes can be output in octal, decimal, hexadecimal, uppercase hexadecimal or base64. It supports directory recursion, hashing entire devices, and generating a hash for an entire directory.
How to install hashrat in Kali Linux:
sudo apt install hashrat
hashrat usage:
hashrat [options] [path to hash]... hashrat -c [options] [input file of hashes]...
hashrat options:
--help Print this help
-help Print this help
-? Print this help
--version Print program version
-version Print program version
-md5 Use md5 hash algorithmn
-sha1 Use sha1 hash algorithmn
-sha256 Use sha256 hash algorithmn
-sha512 Use sha512 hash algorithmn
-whirl Use whirlpool hash algorithmn
-whirlpool Use whirlpool hash algorithmn
-jh224 Use jh-224 hash algorithmn
-jh256 Use jh-256 hash algorithmn
-jh384 Use jh-384 hash algorithmn
-jh512 Use jh-512 hash algorithmn
-hmac HMAC using specified hash algorithm
-8 Encode with octal instead of hex
-10 Encode with decimal instead of hex
-H Encode with UPPERCASE hexadecimal
-HEX Encode with UPPERCASE hexadecimal
-64 Encode with base64 instead of hex
-base64 Encode with base64 instead of hex
-i64 Encode with base64 with rearranged characters
-p64 Encode with base64 with a-z,A-Z and _-, for best compatibility with 'allowed characters' in websites.
-x64 Encode with XXencode style base64.
-u64 Encode with UUencode style base64.
-g64 Encode with GEDCOM style base64.
-a85 Encode with ASCII85.
-z85 Encode with ZEROMQ variant of ASCII85.
-t Output hashes in traditional md5sum, shaXsum format
-trad Output hashes in traditional md5sum, shaXsum format
-bsd Output hashes in bsdsum format
-tag Output hashes in bsdsum format
--tag Output hashes in bsdsum format
-r Recurse into directories when hashing files
-f <listfile> Hash files listed in <listfile>
-i <patterns> Only hash items matching a comma-seperated list of shell patterns
-x <patterns> Exclude items matching a comma-sepearted list of shell patterns
-n <length> Truncate hashes to <length> bytes
-c CHECK hashes against list from file (or stdin)
-cf CHECK hashes against list but only show failures
-C <dir> Recursively CHECK directory against list of files on stdin
-Cf <dir> Recursively CHECK directory against list but only show failures
-m MATCH files from a list read from stdin.
-lm Read hashes from stdin, upload them to a memcached server (requires the -memcached option).
-X In CHECK or MATCH mode only examine executable files.
-exec In CHECK or MATCH mode only examine executable files.
-dups Search for duplicate files.
-memcached <server> Specify memcached server. (Overrides reading list from stdin if used with -m, -c or -cf).
-mcd <server> Specify memcached server. (Overrides reading list from stdin if used with -m, -c or -cf).
-h <script> Script to run when a file fails CHECK mode, or is found in MATCH mode.
-hook <script> Script to run when a file fails CHECK mode, or is found in FIND mode
-color Use ANSI color codes on output when checking hashes.
-strict Strict mode: when checking, check file mtime, owner, group, and inode as well as it's hash
-S Strict mode: when checking, check file mtime, owner, group, and inode as well as it's hash
-d dereference (follow) symlinks
-fs Stay on one file system
-dir DirMode: Read all files in directory and create one hash for them!
-dirmode DirMode: Read all files in directory and create one hash for them!
-devmode DevMode: read from a file EVEN OF IT'S A DEVNODE
-lines Read lines from stdin and hash each line independently.
-rawlines Read lines from stdin and hash each line independently, INCLUDING any trailing whitespace. (This is compatible with 'echo text | md5sum')
-rl Read lines from stdin and hash each line independently, INCLUDING any trailing whitespace. (This is compatible with 'echo text | md5sum')
-cgi Run in HTTP CGI mode
-net Treat 'file' arguments as either ssh or http URLs, and pull files over the network and then hash them (Allows hashing of files on remote machines).
URLs are in the format ssh://[username]:[password]@[host]:[port] or http://[username]:[password]@[host]:[port]..
-idfile <path> Path to a ssh private key file to use to authenticate INSTEAD OF A PASSWORD when pulling files via ssh.
-xattr Use eXtended file ATTRibutes. In hash mode, store hashes in the file attributes, in check mode compare against hashes stored in file attributes.
-txattr Use TRUSTED eXtended file ATTRibutes. In hash mode, store hashes in 'trusted' file attributes. 'trusted' attributes can only be read and written by root. Under freebsd this menas SYSTEM attributes.
-attrs comma-separated list of filesystem attribute names to be set to the value of the hash.
-cache Use hashes stored in 'user' xattr if they're younger than the mtime of the file. This speeds up outputting hashes.
-u <types> Update. In checking mode, update hashes for the files as you go. <types> is a comma-separated list of things to update, which can be 'xattr' 'memcached' or a file name. This will update these targets with the hash that was found at the time of checking.
-hide-input When reading data from stdin in linemode, set the terminal to not echo characters, thus hiding typed input.
-star-input When reading data from stdin in linemode replace characters with stars.
-xsel Update X11 clipboard and primary selections to the current hash. This works using Xterm command sequences. The xterm resource 'allowWindowOps' must be set to 'true' for this to work.
Hashrat can also detect if it's being run under any of the following names (e.g., via symlinks)
md5sum run with '-trad -md5'
shasum run with '-trad -sha1'
sha1sum run with '-trad -sha1'
sha256sum run with '-trad -sha256'
sha512sum run with '-trad -sha512'
jh224sum run with '-trad -jh224'
jh256sum run with '-trad -jh256'
jh384sum run with '-trad -jh384'
jh512sum run with '-trad -jh512'
whirlpoolsum run with '-trad -whirl'
hashrat.cgi run in web-enabled 'cgi mode'
hashrat usage examples:
Generate an md5 hash of data read from stdin (default hash type is md5).
hashrat
Generate a jh-256 hash of data read from stdin
hashrat -jh256
Generate an sha-256 hash of data read from stdin, output with base64 encoding.
hashrat -sha256 -64
Read lines from stdin, and generate an sha-256 with base64 encoding FOR EVERY LINE. This strips any whitespace from the end of the line (including \r and/or \n line terminators).
hashrat -sha256 -64 -lines
Read lines from stdin, and generate an md5 hash in 'traditional' format for every line INCLUDING TRAILING WHITESPACE. This is compatible with 'echo text | md5sum' where 'text' is one line, as 'echo' adds a newline to the end of the text it outputs.
hashrat -md5 -trad -rawlines
Read data from stdin, hash it with sha256, then hash the resulting hash with whirlpool, then with md5
hashrat -type sha256,whirl,md5
Generate a list of hashes for files in the current directory (default hash type is md5).
hashrat *
Generate a list of hashes for files in the current directory, AND ALL SUBDIRECTORIES, using sha1 hashing.
hashrat -r -sha1 * > hashes.sha1
Check hashes listed in 'hashes.sha1'
cat hashes.sha1 > hashrat -c
Check hashes listed in 'hashes.sha1'. If hashes are NOT in 'traditional' format than the '-strict' flag will cause hashrat to check the files uid, gid, size, mtime and inode and print a failure message if any of those don't match.
cat hashes.sha1 > hashrat -c -strict
Check hashes listed in 'hashes.sha1' but only output failures
cat hashes.sha1 > hashrat -cf
Read a list of hashes from stdin, and search recursively for files matching them.
cat APT1.md5 | hashrat -m -r /
Read a list of hashes from stdin, and register them in a memcached server for later use in a search/check.
cat APT1.md5 | hashrat -lm -memcached 127.0.0.1
Extract hashes from an Open IOC file and register them in a memcached server for later use in a search/check.
cat APT1.ioc | hashrat -lm -memcached 127.0.0.1
Search recursively for files whose hashes are stored in a memcached server.
hashrat -m -memcached 127.0.0.1 -r /
Generate a whirlpool hash of the entire device /dev/sda1. Output result in base 64.
hashrat -devmode -whirlpool -64 /dev/sda1
Generate sha1 hashes of files in /bin/* on the remote machine 'myhost'
hashrat -sha1 -net ssh:user:password@myhost/bin/*
Generate whirlpool hash for the listed URL. (Note, many webpages have dynamic content that changes every time, so this will only return the same hash over and over if the page is static and doesn't change.
hashrat -whirlpool -net http://myhost.com/webpage.html
Search for duplicate files under /home. Update hashes stored in filesystem attributes as you go
hashrat -dups -r /home -u xattr
Related articles:
- How to identify hash types (100%)
- How to hack a Windows password (100%)
- How to decrypt stored Windows passwords using mimikatz and DAPA (100%)
- Comprehensive Guide to John the Ripper. Part 6: How to brute force non-standard hashes (100%)
- Comprehensive Guide to John the Ripper. Part 7: Johnny – GUI for John the Ripper (100%)
- How to decrypt NS3 passwords from ZyXEL config file (NDMS V2) (RANDOM - 50%)