New Wash and Reaver Features
Reaver implements a brute force attack against Wifi Protected Setup (WPS) registrar PINs in order to recover WPA/WPA2 passphrases. Wash is an auxiliary tool designed to display WPS enabled Access Points and their main characteristics. Wash program is included in the Reaver package.
Some time ago a number of innovations were added to these programs and various bugs were fixed. In this article I want to talk about the new possibilities of these programs.
To test new programs features together with me, set your wireless in monitor mode:
sudo systemctl stop NetworkManager sudo airmon-ng check kill sudo ip link set wlan0 down sudo iw wlan0 set monitor control sudo ip link set wlan0 up
Note: the original name of my wireless interface is wlan0. The new name is wlan0 either.
New -j // --json option
The extended WPS information (serial, model…) from the AP probe answer will be printed in the terminal (in json format).
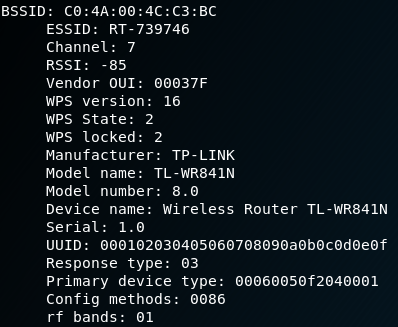
The probe response is a key element to analyze a target as it contains crucial information such as the exact model, the serial number, the wifi chip model, etc… assuming WPS is enabled. You can see here a sample with the kind of data that can be found in the extended WPS information from a probe response:
With the -j tag this information will be displayed in json format (one equally formed line for every router) in order to simplify the automatic parsing and scripting with wash. In the next picture you can see the -j option in action:
Notice that wash is logically a bit slower when you use the -j option as a probe response from the Access Point is needed.
Let’s try the new option:
sudo wash -i wlan0 -j
The output:
JSON format is hardly suite to analyze by a human.
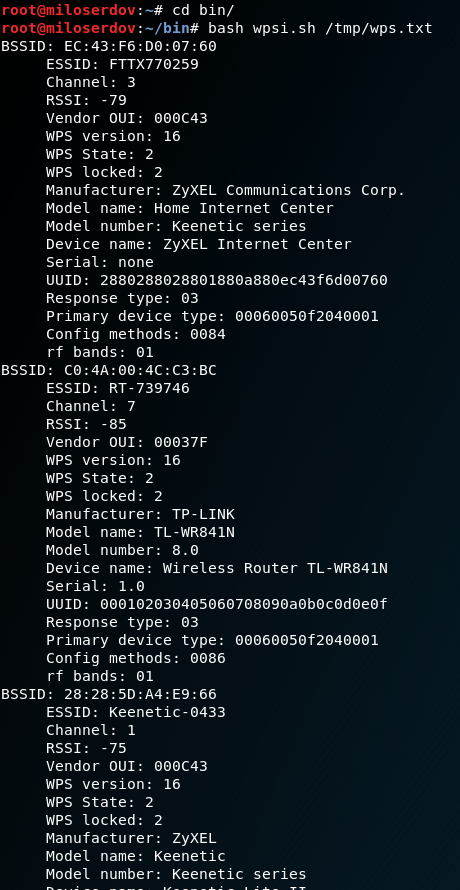
To analyze the output, I wrote a script. To use it, redirect the wash output to a file, like this:
sudo wash -i wlan0 -j > /tmp/wps.txt
Create a file named wpsi.sh:
gedit wpsi.sh
and copy-paste there:
#!/bin/bash
if [[ "$1" && -f "$1" ]]; then
FILE="$1"
else
echo 'Specify the file to analyze.';
echo 'Usage:';
echo -e "\tbash wpsi.sh /tmp/wps.txt";
exit
fi
cat $FILE | sed 's/\" : \"/\\/g' | sed 's/\", \"/\\/g' | sed 's/\" : /\\/g' | sed 's/, \"/\\/g' | awk -F"\\" '{print "BSSID: "$2} {print " ESSID: "$4} {print " Channel: "$6} {print " RSSI: "$8} {print " Vendor OUI: "$10} {print " WPS version: "$12} {print " WPS State: "$14} {print " WPS locked: "$16} {print " Manufacturer: "$18} {print " Model name: "$20} {print " Model number: "$22} {print " Device name: "$24} {print " Serial: "$26} {print " UUID: "$28} {print " Response type: "$30} {print " Primary device type: "$32} {print " Config methods: "$34} {print " rf bands: "$36}'
Usage:
bash wpsi.sh path/to/wash/output/file
Example:
bash wpsi.sh /tmp/wps.txt
The information will be displayed in convenient for perception form:
Power to the user with the pipe compatibility
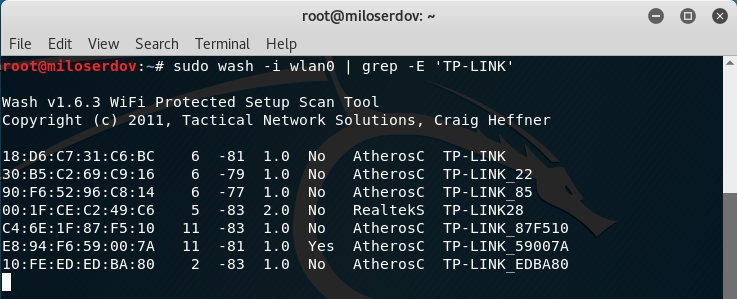
You can now modify "on the fly" wash's stdout with pipe compatibility. Let's take an example: Some users asked to introduce an eSSID filter and others asked to introduce a bSSID filter. It is now possible to do both things with a basic grep command.
Examples:
sudo wash -i wlan0 | grep -E '28:28:5D'
sudo wash -i wlan0 | grep -E 'TP-LINK'
And so much more… You could for example filter by model using the extended information from the new -j option or use a custom script to generate a default PIN with some algorithm and (why not?) colorize the stdout.
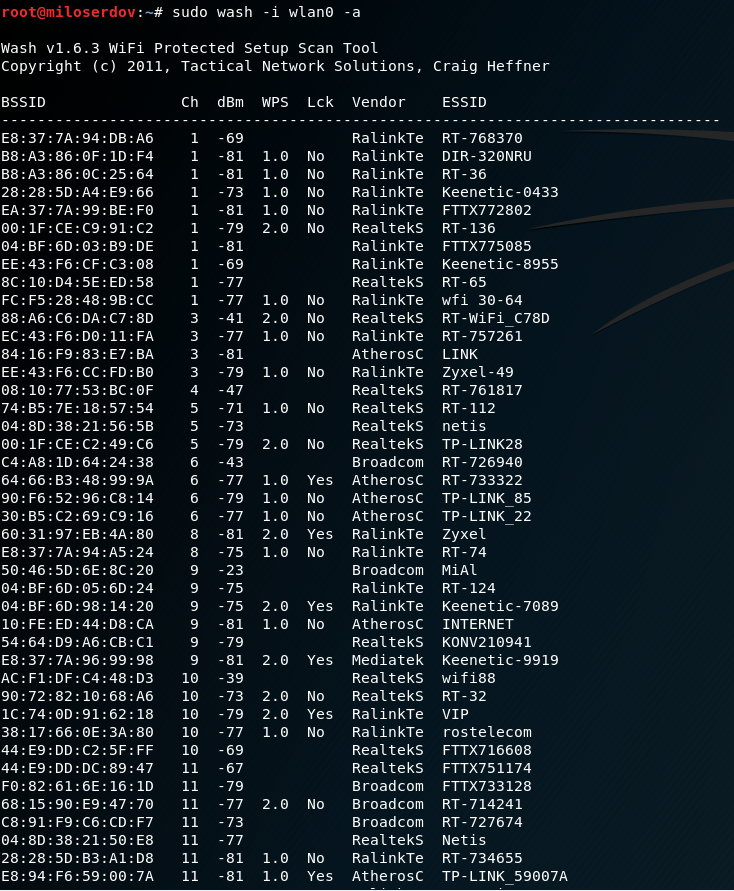
New -a // --all option
While we do a WiFi scan focused on WPS it might be convenient to see APs without WPS enabled too. If you use the -a, --all option, all the Acess Point (with or without WPS) that are detected will show up in the shell.
sudo wash -i wlan0 -a
Other changes:
- wash: several bugfixes for 5 GHz mode
- wash: support WPS 2.0 display
- wash/reaver: display AP chipset vendor
- reaver: reintroduce -vvv debug verbosity mode
- reaver: fix missing display of WPA PSK with -N
- reaver: fix several bugs that made it hard to use RALINK chips
- reaver: add some new infos to output
- build system: build all objects from toplevel makefile
- wash: fixed missing handling of EXT bit in radiotap present field,
- which caused wrong/missing dbm values with some drivers
- final big endian fix
- several other minor issues
- wash/reaver: remove several options
Related articles:
- How to hack Wi-Fi using Reaver (100%)
- How to install airgeddon on Linux Mint or Ubuntu (56.9%)
- WiFi-autopwner: script to automate searching and auditing Wi-Fi networks with weak security (56.9%)
- Automated Pixie Dust Attack: receiving WPS PINs and Wi-Fi passwords without input any commands (56.9%)
- How to find out the exact model of a router (wireless access point) (56.9%)
- Virtual Wi-Fi interfaces for simultaneous use of a Wi-Fi adapter in different modes (RANDOM - 51.5%)