Word lists for brute-force
wordlistctl: large database of dictionaries [Dictionary Collection]
wordlistctl is a program that contains a large database of dictionaries. In fact, it is this database that is of interest, dictionaries can be downloaded directly, without this program – I will give links to the databases below, they are in JSON format, that is, quite readable.
wordlistctl is created by blackarch.org developers, web site: https://github.com/BlackArch/wordlistctl
How to install wordlistctl
Installing wordlistctl on Kali Linux:
sudo apt install python3-pip python3-libtorrent python3-coloredlogs git clone https://github.com/BlackArch/wordlistctl cd wordlistctl
Open the requirements.txt file
gedit requirements.txt
And remove the line from there
libtorrent
Then continue:
sudo pip3 install -r requirements.txt python3 ./wordlistctl.py
In BlackArch, this program is in the standard repository – install directly from there.
sudo pacman -S wordlistctl
How to use wordlistctl
All dictionaries are divided into 5 categories:
- username
- password
- hostname
- filename
- misc = other
To show all dictionaries, for example, in the password category:
wordlistctl -F password
With the -S option, you can search by dictionary names, for example, search for ‘rus’:
wordlistctl -S rus --==[ wordlistctl by blackarch.org ]==-- [*] searching for rus in urls.json [+] wordlist russian_users found: id=842 [+] wordlist rus_surnames_date099_fin found: id=1022 [+] wordlist rus_surnames_first_letter found: id=1046 [+] wordlist rus_surnames_fin found: id=1094 [+] wordlist rus_surnames_date19002020_fin found: id=1104 [+] wordlist rus_names_date099_fin found: id=1163 [+] wordlist rus_names_translit found: id=1185 [+] wordlist rus_cities_translit found: id=1206 [+] wordlist rus_names_date19002020_fin found: id=1209 [+] wordlist rus_eng found: id=1245 [+] wordlist rus_names_fin found: id=1278 [+] wordlist rus_mat found: id=1316 [+] wordlist rus_latin found: id=1323 [+] wordlist rus_names_kb_chage found: id=1324 [+] wordlist rus_cities_kbchange found: id=1401 [+] wordlist rus-mini found: id=1705 [+] wordlist russian found: id=1710 [+] wordlist russian2 found: id=1711 [+] wordlist russian_31799 found: id=1712 [+] wordlist russian_name found: id=1713 [+] wordlist russkie-maty found: id=1714 [+] wordlist rus_months_en found: id=1768 [+] wordlist rus_months_translit found: id=1769
To download dictionaries, create a wordlists folder in the current directory:
mkdir wordlists
And download to this folder (-d wordlists) a dictionary that has the identifier 1714 (-f 1714), unpack it and delete the original archive (-Xr):
wordlistctl -f 1714 -d wordlists -Xr
Brute-force word list collection for Kali Linux [Dictionary Collection]
Kali.Tools has a page that does not contain dictionaries from various sources and with different purposes.
You will find some of these dictionaries right in your Kali Linux system. For the rest are given links to download.
A page with brute force dictionaries and their description: https://kali.tools/?p=1896
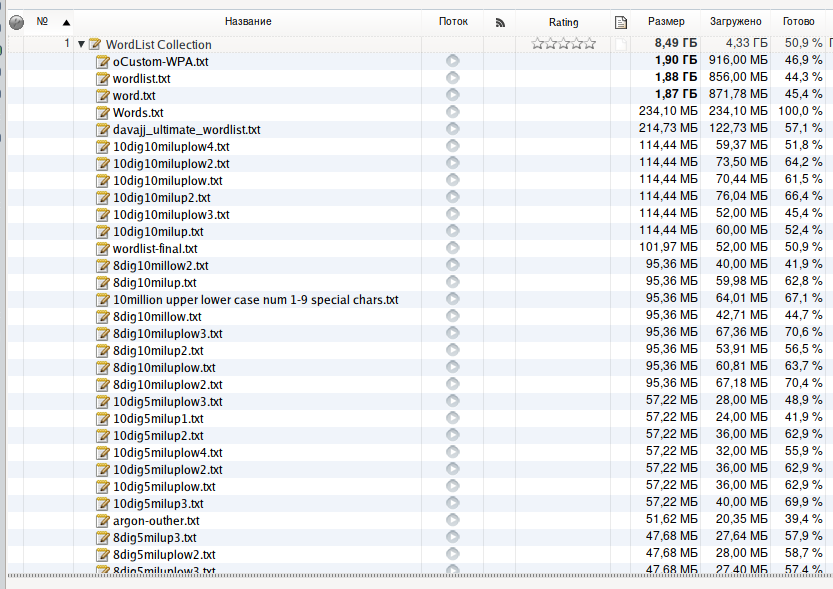
Collection of dictionaries from the WirelessHack.org site [Dictionaries for hacking Wi-Fi]
The WirelessHack.org site collected dictionaries that have been hanging around for some time here and there.
Description page: https://www.wirelesshack.org/wpa-wpa2-word-list-dictionaries.html
Included dictionaries:
- BIG-WPA-LIST-1 (size 247MB)
- BIG-WPA-LIST-2 (size 307MB)
- BIG-WPA-LIST-3 (size 277MB)
- Darkc0de.lst (size 17.4MB) - this was the default dictionary in Backtrack 5
- Rockyou.txt (size 133MB) - default dictionary in Kali Linux
- Names (size 3.7MB) - names and variants of names
Besides them, there are still quite a few dictionaries, for a total of 8.5 GB. If you use dictionaries infrequently, it is recommended to compress them for save storage space – they are plain text files that may be compressed very well – after archiving they will take about 10 times less space.
Magnet link:
magnet:?xt=urn:btih:6c89df058f71559dec6c5c7c9f2cb419182b3294&dn=Collection+of+Wordlist+%28Dictionaries%29+for+cracking+WiFi+WPA/WPA2&tr=udp%3A//tracker.leechers-paradise.org%3A6969&tr=udp%3A//zer0day.ch%3A1337&tr=udp%3A//tracker.coppersurfer.tk%3A6969&tr=udp%3A//public.popcorn-tracker.org%3A6969
The torrent file: https://miloserdov.org/wp-content/uploads/2019/03/1544257923-WordList-Collection.zip
Related articles:
- Comprehensive Guide to John the Ripper. Part 3: How to start cracking passwords in John the Ripper (how to specify masks, dictionaries, hashes, formats, modes) (100%)
- Comprehensive Guide to John the Ripper. Part 4: Practical examples of John the Ripper usage (100%)
- Comprehensive Guide to John the Ripper. Part 5: Rule-based attack (100%)
- Comprehensive Guide to John the Ripper. Part 6: How to brute force non-standard hashes (100%)
- Comprehensive Guide to John the Ripper. Part 7: Johnny – GUI for John the Ripper (100%)
- Hashcat doesn't detect AMD CPUs (SOLVED) (RANDOM - 67.2%)