How to install Greenbone Vulnerability Management (GVM) (formerly OpenVAS) on Kali Linux
OpenVAS is now renamed Greenbone Vulnerability Management (GVM)
When the OpenVAS project was created, it only consisted of a vulnerability scanning engine. Greenbone Networks received funding shortly thereafter to provide professional vulnerability scanning support. Greenbone took over development leadership, added a few software components, and turned OpenVAS into a multi-pronged vulnerability management solution that still retains the value of open and free software.
Over the years, it became apparent that the use of OpenVAS as a trademark for an open source project and funding for almost all of the project's development had not been appreciated from outside. Therefore, after the release of the OpenVAS 9 platform, it was renamed Greenbone Vulnerability Management (GVM) and released as Greenbone Source Edition (GSE). Since GVM 10, the term OpenVAS is used only for the scanner component, as it was at the beginning of the project.
Greenbone Vulnerability Management (GVM) packages: https://github.com/greenbone
Errors when installing and starting GVM, OpenVAS
During the installation and launch process, I encountered quite a few errors, which, nevertheless, were resolved. Under the assumption that these errors are common to everyone (not just my particular installation), I described these errors right during the installation process, as a result of which the instructions became cluttered.
If during the installation process you do not encounter the described errors, please write about it in the comments – if the errors do not appear for everyone, then I will put them at the very end of the article, due to which, in general, the instruction will become clearer.
How to install OpenVAS (GVM)
Since the authors renamed openvas to gvm (more precisely, divided it into different packages), now the main package is gvm, when it is installed, all other necessary packages will also be obtained as dependencies.
Installation is done like this:
sudo apt update sudo apt install gvm
Setting up OpenVAS
Let's start by setting up the Open Vulnerability Assessment Scanner (OpenVAS) for Greenbone Vulnerability Management (GVM) solution.
It is used in Greenbone Security Manager and is a full-fledged scan engine that performs constantly updated and expanded submissions of Network Vulnerability Tests (NVTs).
The scanner needs a running Redis server to temporarily store the collected information on the scanned hosts. Configuring the Redis server is done like this (these commands need to be executed once):
wget https://raw.githubusercontent.com/greenbone/openvas-scanner/master/config/redis-openvas.conf sudo cp redis-openvas.conf /etc/redis/ sudo chown redis:redis /etc/redis/redis-openvas.conf echo 'db_address = /run/redis-openvas/redis.sock' | sudo tee /etc/openvas/openvas.conf
Starting the Redis server (must be done after every computer restart):
sudo systemctl start redis-server@openvas.service
Or, if you like, add it to startup:
sudo systemctl enable redis-server@openvas.service
The Greenbone Vulnerability Management (gvmd) service acts as an OSP client to connect to and manage scanners. openvas does not act as an OSP service – you need the OSPD-OpenVAS module for that. Actual user interfaces (like GSA or GVM-Tools) will only interact with gvmd and/or ospd-openvas, not the scanner. You can run openvas to load plugins in Redis using the following command:
sudo openvas -u
but ospd-openvas will update automatically.
Please note that although you can run openvas as a non-elevated user, it is recommended that you run openvas as root because some network vulnerability tests (NVTs) require root privileges to perform certain operations, such as package spoofing. If you run openvas as a user without permission to perform these operations, the scan results are likely to be incomplete.
Since openvas will be launched from the ospd-openvas process using sudo, the following configuration is required in the sudoers file:
sudo visudo
add this line to allow the user running ospd-openvas to run openvas as root
USERNAME ALL = NOPASSWD: /usr/sbin/openvas
Replace USERNAME with your Linux username.
You can find out the username with the command:
echo $USER
If something does not work, then you can view the log with the command:
cat /var/log/gvm/openvas.log
Configuring Greenbone Vulnerability Management (GVM)
Greenbone Vulnerability Manager is the central management service between security scanners and user clients.
It manages the storage of any vulnerability management configuration and scan results. Data, control commands, and workflows are accessed through the XML-based Greenbone Management Protocol (GMP). Scanners such as OpenVAS are controlled through the Open Scanner Protocol (OSP).
Deployment script (instead of openvas-setup):
sudo gvm-setup
This script needs to be run only once.
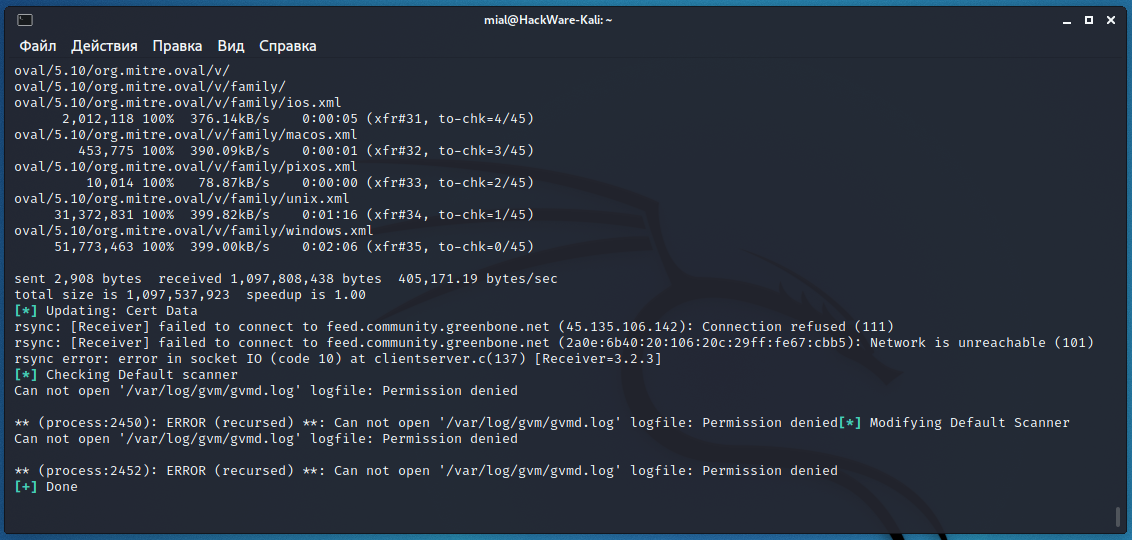
The script ended with an error:
sent 2,908 bytes received 1,097,808,438 bytes 405,171.19 bytes/sec total size is 1,097,537,923 speedup is 1.00 [*] Updating: Cert Data rsync: [Receiver] failed to connect to feed.community.greenbone.net (45.135.106.142): Connection refused (111) rsync: [Receiver] failed to connect to feed.community.greenbone.net (2a0e:6b40:20:106:20c:29ff:fe67:cbb5): Network is unreachable (101) rsync error: error in socket IO (code 10) at clientserver.c(137) [Receiver=3.2.3] [*] Checking Default scanner Can not open '/var/log/gvm/gvmd.log' logfile: Permission denied ** (process:2450): ERROR (recursed) **: Can not open '/var/log/gvm/gvmd.log' logfile: Permission denied[*] Modifying Default Scanner Can not open '/var/log/gvm/gvmd.log' logfile: Permission denied ** (process:2452): ERROR (recursed) **: Can not open '/var/log/gvm/gvmd.log' logfile: Permission denied [+] Done
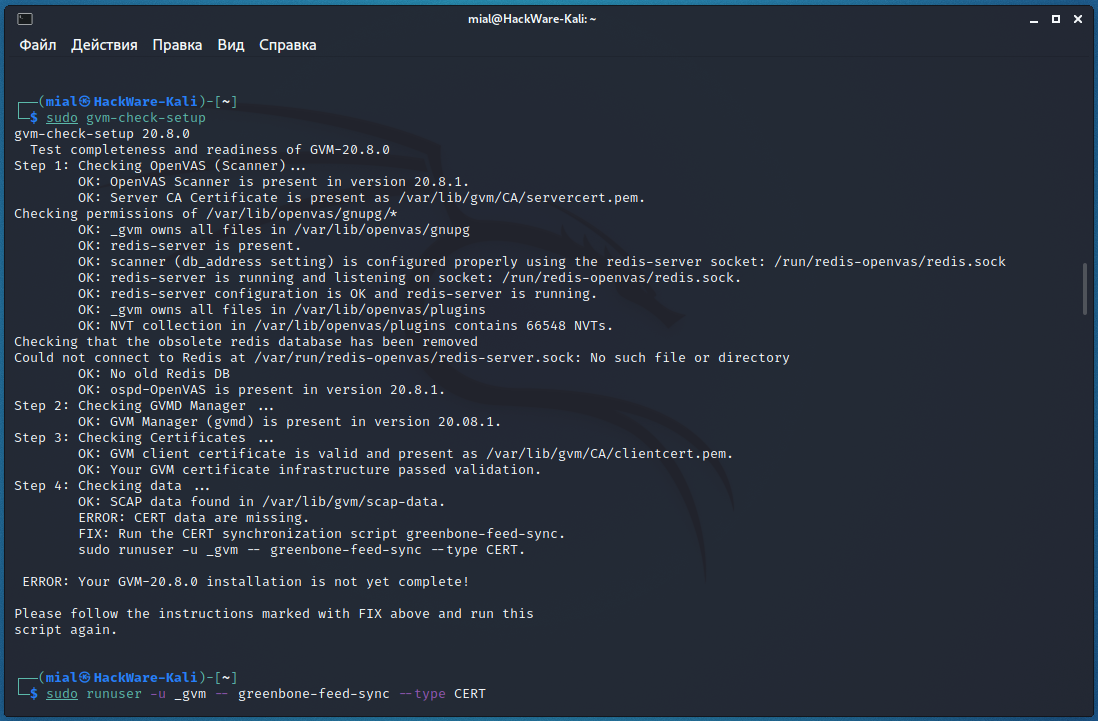
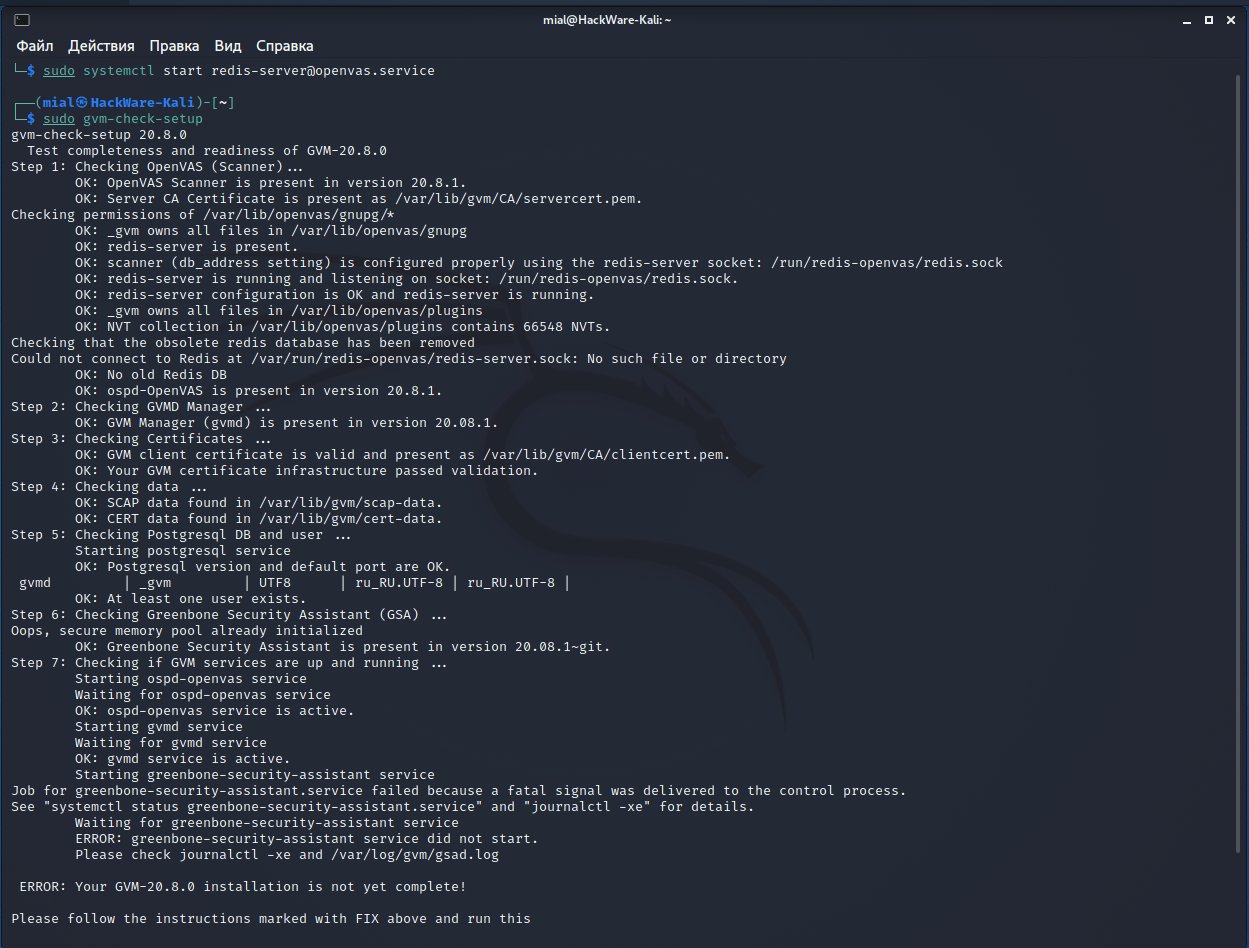
Running check:
sudo gvm-check-setup
also showed an error in the fourth step:
gvm-check-setup 20.8.0
Test completeness and readiness of GVM-20.8.0
Step 1: Checking OpenVAS (Scanner)...
OK: OpenVAS Scanner is present in version 20.8.1.
OK: Server CA Certificate is present as /var/lib/gvm/CA/servercert.pem.
Checking permissions of /var/lib/openvas/gnupg/*
OK: _gvm owns all files in /var/lib/openvas/gnupg
OK: redis-server is present.
OK: scanner (db_address setting) is configured properly using the redis-server socket: /run/redis-openvas/redis.sock
OK: redis-server is running and listening on socket: /run/redis-openvas/redis.sock.
OK: redis-server configuration is OK and redis-server is running.
OK: _gvm owns all files in /var/lib/openvas/plugins
OK: NVT collection in /var/lib/openvas/plugins contains 66548 NVTs.
Checking that the obsolete redis database has been removed
Could not connect to Redis at /var/run/redis-openvas/redis-server.sock: No such file or directory
OK: No old Redis DB
OK: ospd-OpenVAS is present in version 20.8.1.
Step 2: Checking GVMD Manager ...
OK: GVM Manager (gvmd) is present in version 20.08.1.
Step 3: Checking Certificates ...
OK: GVM client certificate is valid and present as /var/lib/gvm/CA/clientcert.pem.
OK: Your GVM certificate infrastructure passed validation.
Step 4: Checking data ...
OK: SCAP data found in /var/lib/gvm/scap-data.
ERROR: CERT data are missing.
FIX: Run the CERT synchronization script greenbone-feed-sync.
sudo runuser -u _gvm -- greenbone-feed-sync --type CERT.
ERROR: Your GVM-20.8.0 installation is not yet complete!
Please follow the instructions marked with FIX above and run this
script again.
To fix the error “ERROR: CERT data are missing. FIX: Run the CERT synchronization script greenbone-feed-sync” run the following command:
sudo runuser -u _gvm -- greenbone-feed-sync --type CERT
Re-running the check showed an error at the fifth step:
Step 5: Checking Postgresql DB and user ...
OK: Postgresql version and default port are OK.
gvmd | _gvm | UTF8 | ru_RU.UTF-8 | ru_RU.UTF-8 |
Can not open '/var/log/gvm/gvmd.log' logfile: Permission denied
** (process:2699): ERROR (recursed) **: Can not open '/var/log/gvm/gvmd.log' logfile: Permission denied ERROR: No users found. You need to create at least one user to log in.
FIX: create a user by running 'sudo runuser -u _gvm -- gvmd --create-user=<name> --password=<password>'
ERROR: Your GVM-20.8.0 installation is not yet complete!
Please follow the instructions marked with FIX above and run this
script again.
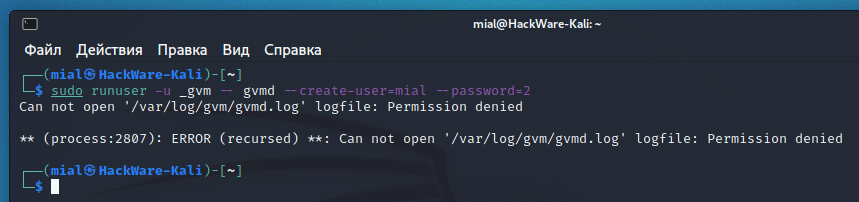
There are several errors at once, but the key one is “ERROR: No users found. You need to create at least one user to log in.”, To fix it, run a command like this:
sudo runuser -u _gvm -- gvmd --create-user=<USERNAME> --password=<PASSWORD>
For example, to create a user named mial and password 2:
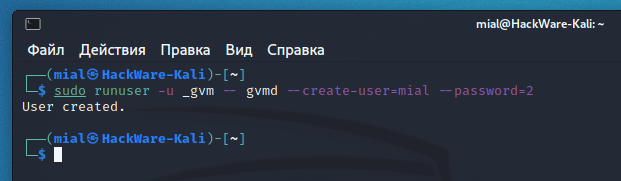
sudo runuser -u _gvm -- gvmd --create-user=mial --password=2
The previous command failed:
Can not open '/var/log/gvm/gvmd.log' logfile: Permission denied ** (process:2807): ERROR (recursed) **: Can not open '/var/log/gvm/gvmd.log' logfile: Permission denied
The essence of the error is that the command does not have enough permissions to write to the /var/log/gvm/gvmd.log file, even though the previous command was run with sudo. To fix the error, run the following command:
sudo chmod 666 /var/log/gvm/gvmd.log
Then run the new user creation again.
And one more mistake at the seventh step:
Step 7: Checking if GVM services are up and running ...
OK: ospd-openvas service is active.
Starting gvmd service
Waiting for gvmd service
OK: gvmd service is active.
Starting greenbone-security-assistant service
Job for greenbone-security-assistant.service failed because a fatal signal was delivered to the control process.
See "systemctl status greenbone-security-assistant.service" and "journalctl -xe" for details.
Waiting for greenbone-security-assistant service
ERROR: greenbone-security-assistant service did not start.
Please check journalctl -xe and /var/log/gvm/gsad.log
ERROR: Your GVM-20.8.0 installation is not yet complete!
Please follow the instructions marked with FIX above and run this
script again.
I don't know how to solve it completely, but I know how to get around it.
Let's move on to starting the necessary services.
Do not forget that before starting the service you need to start the Redis server, that is, type following before executing the primary command:
sudo systemctl start redis-server@openvas.service
Main service start:
sudo gvm-start
And we get the following:
[*] Please wait for the GVM / OpenVAS services to start. [*] [*] You might need to refresh your browser once it opens. [*] [*] Web UI (Greenbone Security Assistant): https://127.0.0.1:9392 Job for greenbone-security-assistant.service failed because a fatal signal was delivered to the control process. See "systemctl status greenbone-security-assistant.service" and "journalctl -xe" for details.
The essence of the messages is that everything started fine, except for the greenbone-security-assistant, that is, gsa, that is, Web UI (Greenbone Security Assistant), that is, the web interface.
You can see the contents of the log file:
cat /var/log/gvm/gsad.log
Output:
gsad main:MESSAGE:2021-04-15 09h07.55 utc:1650: Starting GSAD version 20.08.1~git gsad main:CRITICAL:2021-04-15 09h07.55 utc:1651: main: start_https_daemon failed!
https daemon failed to start .
gsad has a --http-only option which only runs HTTP without HTTPS. Let's use it:
sudo gsad --http-only
Again, the next message will be displayed that something is wrong:
Oops, secure memory pool already initialized
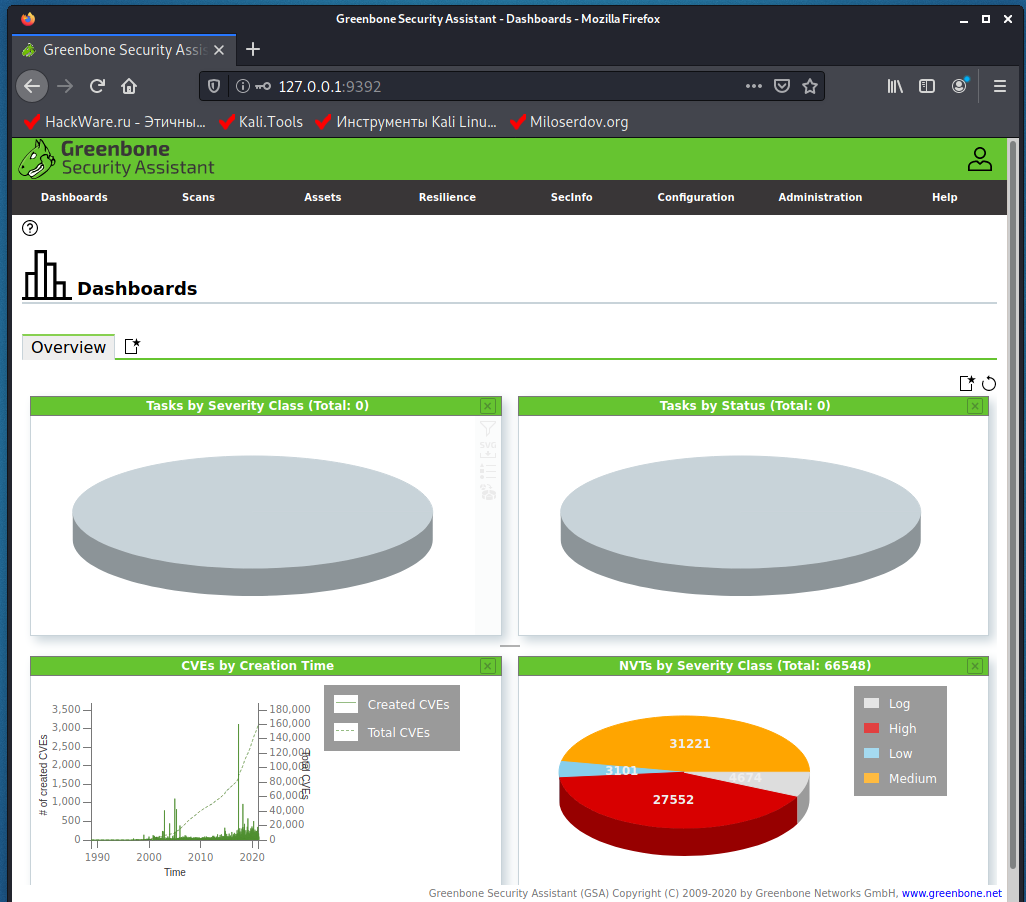
However, the web interface is now available at http://127.0.0.1:9392 (but not available at https://127.0.0.1:9392!).
Log in using the credentials that you came up with when creating a new user.
To stop the service:
sudo gvm-stop
Other:
sudo gvm-cli sudo gvm-feed-update sudo gvm-manage-certs sudo gvm-pyshell gvm-script
In the future, sometimes run the command to update signatures:
sudo runuser -u _gvm -- greenbone-nvt-sync
If something does not work, then you can view the log with the command:
sudo cat /var/log/gvm/gvmd.log
Conclusion
One of the following instructions will be devoted to how to work in Greenbone Vulnerability Management (GVM) (formerly OpenVAS).
And do not forget to write – have you encountered the described errors during installation?
Related articles:
- Default passwords in Kali Linux (100%)
- Kali Linux Rolling post install tips (51.1%)
- How to install OWASP Mutillidae II and Damn Vulnerable Web Application (DVWA) in Kali Linux (51.1%)
- How to install and run VLC, Google Chrome, and Chromium on Kali Linux (51.1%)
- How to update Kali Linux (51.1%)
- Configuring and starting network services on Kali Linux (Apache, MySQL, SSH, PostgreSQL, NetworkManager and Bluetooth) (RANDOM - 51.1%)


Dear Sir,
I found feed status are "update in progress" and "scap database is required" on my Open VAS GVM platform.I have tried may option to update feeds but notings works.
This is log OPEN VAS:
libgvm util:MESSAGE:2021-09-11 06h52.30 utc:5664: Updated NVT cache from version 0 to 202109101034
libgvm util:MESSAGE:2021-09-11 09h04.08 utc:1213: Updated NVT cache from version 0 to 202109101034
libgvm util:MESSAGE:2021-09-11 09h48.54 utc:1297: Updated NVT cache from version 0 to 202109101034
libgvm util:MESSAGE:2021-09-11 10h09.17 utc:1168: Updated NVT cache from version 0 to 202109101034
libgvm util:MESSAGE:2021-09-11 13h05.31 utc:1220: Updated NVT cache from version 0 to 202109101034
libgvm util:MESSAGE:2021-09-11 13h23.30 utc:1159: Updated NVT cache from version 0 to 202109101034
libgvm util:MESSAGE:2021-09-11 13h55.51 utc:1148: Updated NVT cache from version 0 to 202109101034
libgvm util:MESSAGE:2021-09-11 15h45.48 utc:1197: Updated NVT cache from version 0 to 202109101034
libgvm util:MESSAGE:2021-09-11 17h46.23 utc:1712: Updated NVT cache from version 0 to 202109101034
libgvm util:MESSAGE:2021-09-11 18h09.25 utc:1194: Updated NVT cache from version 0 to 202109101034
libgvm util:MESSAGE:2021-09-13 15h31.07 utc:1204: Updated NVT cache from version 0 to 202109101034
libgvm util:CRITICAL:2021-09-13 15h31.17 utc:2876: redis_find: redis connection error to /run/redis-openvas/redis.sock: No such file or directory
libgvm util:CRITICAL:2021-09-13 15h31.17 utc:2876: get_redis_ctx: redis connection error to /run/redis-openvas/redis.sock: No such file or directory
libgvm util:CRITICAL:2021-09-13 15h31.17 utc:2876: get_redis_ctx: redis connection error to /run/redis-openvas/redis.sock: No such file or directory
libgvm util:CRITICAL:2021-09-13 15h37.41 utc:3412: redis_find: redis connection error to /run/redis-openvas/redis.sock: No such file or directory
libgvm util:CRITICAL:2021-09-13 15h37.41 utc:3412: get_redis_ctx: redis connection error to /run/redis-openvas/redis.sock: No such file or directory
libgvm util:CRITICAL:2021-09-13 15h37.41 utc:3412: get_redis_ctx: redis connection error to /run/redis-openvas/redis.sock: No such file or directory
libgvm util:MESSAGE:2021-09-13 16h25.01 utc:3395: Updated NVT cache from version 0 to 202109131026
libgvm util:MESSAGE:2021-09-13 16h34.58 utc:1214: Updated NVT cache from version 0 to 202109131026
Regards,
Nasim
Hi! thanks for the tutorial!
on "sudo gvm-setup" i get this:
rsync: [generator] failed to set permissions on "/var/lib/openvas/plugins/2014/gb_fedora_2014_5004_httpd_fc19.nasl": Function not implemented (38)
rsync: [generator] failed to set permissions on "/var/lib/openvas/plugins/2014/gb_fedora_2014_5006_json-c_fc20.nasl": Function not implemented (38)
rsync: [generator] failed to set permissions on "/var/lib/openvas/plugins/2014/gb_fedora_2014_5015_elfutils_fc20.nasl": Function not implemented (38)
etc… for all files
what's up? how to solve?
thanks
Hi Mial,
I was able to install with NO errors as per your instructions.
HW: Raspberry Pi 4
OS: Linux kali 5.4.83-Re4son-v7l+
└─$ sudo gvm-check-setup
gvm-check-setup 21.4.2
Test completeness and readiness of GVM-21.4.2
Step 1: Checking OpenVAS (Scanner)…
OK: OpenVAS Scanner is present in version 21.4.2.
OK: Server CA Certificate is present as /var/lib/gvm/CA/servercert.pem.
Checking permissions of /var/lib/openvas/gnupg/*
OK: _gvm owns all files in /var/lib/openvas/gnupg
OK: redis-server is present.
OK: scanner (db_address setting) is configured properly using the redis-server socket: /run/redis-openvas/redis.sock
OK: redis-server is running and listening on socket: /run/redis-openvas/redis.sock.
OK: redis-server configuration is OK and redis-server is running.
OK: _gvm owns all files in /var/lib/openvas/plugins
OK: NVT collection in /var/lib/openvas/plugins contains 77207 NVTs.
Checking that the obsolete redis database has been removed
Could not connect to Redis at /var/run/redis-openvas/redis-server.sock: No such file or directory
OK: No old Redis DB
OK: ospd-OpenVAS is present in version 21.4.2.
Step 2: Checking GVMD Manager …
OK: GVM Manager (gvmd) is present in version 21.4.3.
Step 3: Checking Certificates …
OK: GVM client certificate is valid and present as /var/lib/gvm/CA/clientcert.pem.
OK: Your GVM certificate infrastructure passed validation.
Step 4: Checking data …
OK: SCAP data found in /var/lib/gvm/scap-data.
OK: CERT data found in /var/lib/gvm/cert-data.
Step 5: Checking Postgresql DB and user …
OK: Postgresql version and default port are OK.
gvmd | _gvm | UTF8 | C.UTF-8 | C.UTF-8 |
OK: At least one user exists.
Step 6: Checking Greenbone Security Assistant (GSA) …
Oops, secure memory pool already initialized
OK: Greenbone Security Assistant is present in version 21.4.2.
Step 7: Checking if GVM services are up and running …
Starting ospd-openvas service
Waiting for ospd-openvas service
OK: ospd-openvas service is active.
Starting gvmd service
Waiting for gvmd service
OK: gvmd service is active.
Starting greenbone-security-assistant service
Waiting for greenbone-security-assistant service
OK: greenbone-security-assistant service is active.
Step 8: Checking few other requirements…
OK: nmap is present in version 21.4.2.
OK: ssh-keygen found, LSC credential generation for GNU/Linux targets is likely to work.
WARNING: Could not find makensis binary, LSC credential package generation for Microsoft Windows targets will not work.
SUGGEST: Install nsis.
OK: xsltproc found.
WARNING: Your password policy is empty.
SUGGEST: Edit the /etc/gvm/pwpolicy.conf file to set a password policy.
It seems like your GVM-21.4.2 installation is OK.
Thanks.
Cheers,
Randy
Hi again -- Even though I was able to install with NO errors, I could not access the website. Do you know where the port number is configured? I ran the "
sudogsad --http-only" command due to the error in the logs, but that still didn't allow me to access the website.Randy
after all the installation if i try to set a new scan config i have the error "Failed to find config 'daba56c8-73ec-11df-a475-002264764cea'"
me too
Hi,
run
sudogvm-feed-updateand then check in the web ui Administration -> Feed StatusMake sure they have completed ipdating, then try adding a scan againA
HI,
How to fix this problem in Kali2022.2 gvm 21.4.4??
Regard,
AN
I've found this article after trying to setup GSM on ParrotOS because currently it's not working from parrot repos. So here's some of my notes on doing it there:
1. Do "apt search openvas" and remove all pre-installed parrot packages
2. Add kali repo to your system step by step like in this article
https://miloserdov.org/?p=3609
3. sudo apt install -t kali-rolling gvm
4. During "Setting up OpenVAS" step do this command instead:
echo'db_address = /run/redis-openvas/redis-server.sock'|sudotee/etc/openvas/openvas.confThis is the correct name for .sock and will fix error during "gvm-check-setup" later on
5. At some point you will encounter postresql error, to fix it do
sudo pg_lsclusters
sudo pg_dropcluster --stop 14 main
sudo pg_upgradecluster 13 main
sudo pg_dropcluster --stop 13 main
6. And another error that you'll encounter is "redis-server is not running or listening on socket"
To fix it you need to edit /etc/redis/redis.conf
And uncomment
#unixsocket /var/run/redis/redis-server.sock
#unixsocketperm 700
I've managed to set up OpenVAS like this, hope it'll help
Michael, thank you so much for sharing!